Mobile Security
Android logo on a smart phone
Сloud Security
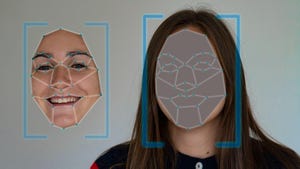
Billions of Android Devices Open to 'Dirty Stream' AttackBillions of Android Devices Open to 'Dirty Stream' Attack
Microsoft has uncovered a common vulnerability pattern in several apps allowing code execution; at least four of the apps have more than 500 million installations each; and one, Xiaomi's File Manager, has at least 1 billion installations.
Keep up with the latest cybersecurity threats, newly discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or weekly right to your email inbox.






.jpg?width=100&auto=webp&quality=80&disable=upscale)