thumbnail
Endpoint Security
Tech Companies Promise 'Secure by Design' ProductsTech Companies Promise 'Secure by Design' Products
Over 60 companies have signed CISA's Secure by Design pledge to consider security from the design phase and throughout the product life cycle.

Ask the Experts
Read MoreFEATURED THREAT MONITOR
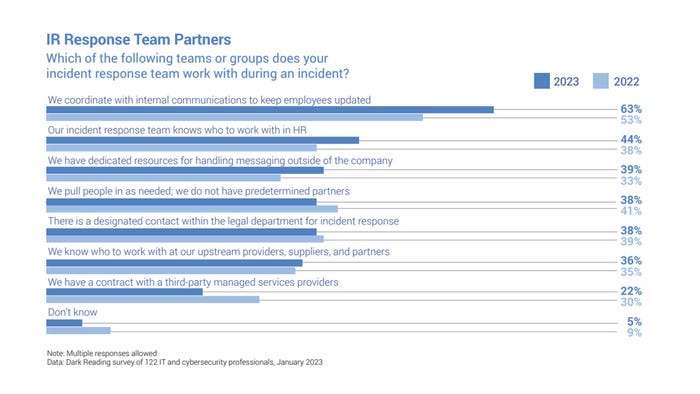
Effective Incident Response Relies on Internal and External Partnerships
Dark Reading research finds increased collaboration between security incident responders and groups within the HR, legal, and communications functions.