Threat Intelligence
Breaking news, news analysis, and expert commentary on cybersecurity threat intelligence, including tools & technologies.
Screenshot of Gartner chart regarding security operations and SOAR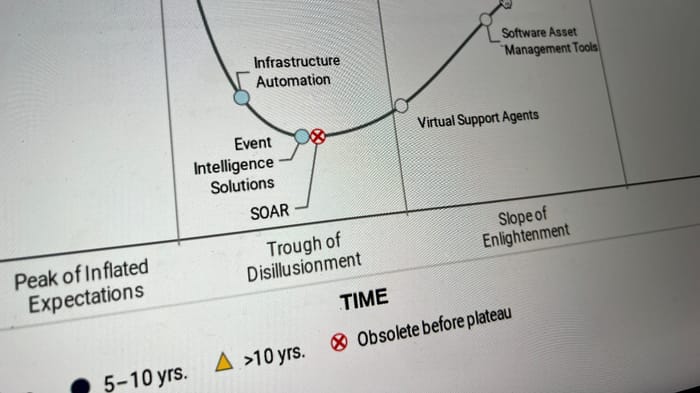
Cybersecurity Operations
SOAR Is Dead, Long Live SOARSOAR Is Dead, Long Live SOAR
Business intelligence firm Gartner labels security orchestration, automation, and response as "obsolete," but the fight to automate and simplify security operations is here to stay.
Keep up with the latest cybersecurity threats, newly discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or weekly right to your email inbox.







.jpg?width=100&auto=webp&quality=80&disable=upscale)



































_Daniren_Alamy.jpg?width=700&auto=webp&quality=80&disable=upscale)
