
News, news analysis, and commentary on the latest trends in cybersecurity technology.
Adaptive Access Technologies Gaining Traction for Security, Agility
With companies pushing to adopt zero-trust frameworks, adaptive authentication and access — once languishing — looks finally ready to move out of the doldrums.
March 31, 2023

Although only seeing tepid adoption to date, adaptive access and authentication is set to gain steam among businesses this year as organizations pursue zero-trust capabilities that grant and restrict access to data and systems based on context.
In the latest sign of life in the evolving industry, startup company Oleria announced on March 21 that it had jumped into the market for providing adaptive access that can keep applications secure and allow access while minimizing blind spots and the overprovisioning of privileges. The company's executives maintained that easing deployment of granular and adaptive authentication will convince business customers to more rapidly adopt the technologies.
Companies already know that they need the context-aware security that adaptive access provides, says Jagadeesh Kunda, co-founder and chief product officer of Oleria.
"Modern IT has become a continuous, complex system, adapting dynamically to business needs, [but] the gap we hear from CISOs and CIOs is the ability to effectively manage access," he says. "With the typical organization running hundreds of applications to support an ever-changing environment, assigning roles and access on a static basis is no longer sufficient or sustainable."
While most companies strive for more granular access controls, adaptive technologies have foundered due to the complexity of the solutions. In its 2022 "MarketScape" report for advanced authentication, analyst firm International Data Corp. estimated that fewer than three in 10 companies use multifactor authentication (MFA), which is only an initial step toward the more advanced access controls represented by adaptive access and authentication. Overall, only 9% of companies have added context-based access policies, which in many ways are the foundation of adaptive access controls, according to Okta's 2022 "State of Zero Trust" report.
Cloud Native Security Means Adapting
Yet companies are convinced of the necessity of adaptive access because the ability to grant users access to the appropriate data in the proper way has become significantly more important. While only 9% of companies currently have access controls based on context, a significant 42% of businesses intend to implement those policies in the next 12 to 18 months, Okta stated in its report.
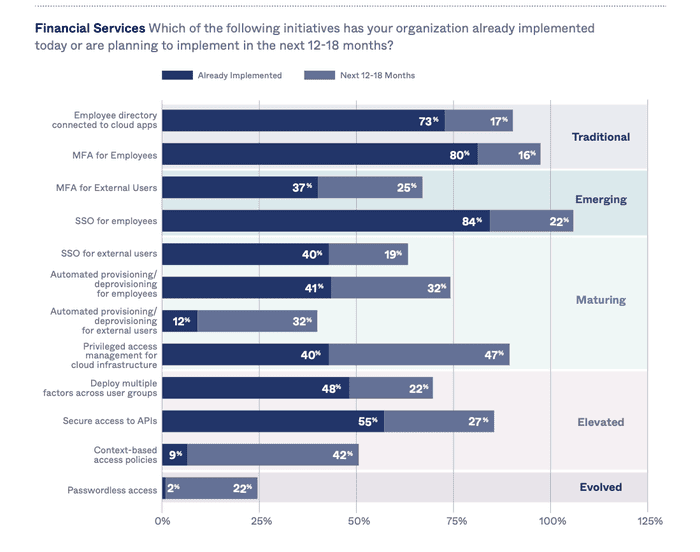
Only 9% of companies use context-based access policies, but 42% plan to adopt them. Source: Okta
The technology allows companies — and their security teams — to be more agile, says Chris Niggel, chief security officer for the Americas at Okta.
"It helps protect data by allowing the organization to be confident that sensitive data is only being accessed by approved individuals using approved systems," he says. "It allows IT and security teams to enable the business by more quickly granting and revoking access to this sensitive data."
While seemingly similar, adaptive access and adaptive authentication are slightly different concepts, Oleria's Kunda says. Adaptive access gives a user permissions to specific resources based on the user's behavior, the context of the request, the state of their device, and the overall organizational risk level, while adaptive authentication allows for changing privileges based on those criteria.
With the two technologies, companies can determine the level of access that is appropriate in a particular context and deliver that access, he says.
"As organizations increasingly recognize the importance of dynamically granting or denying access based on contextual factors, such as user behavior and risk level, adoption of adaptive access approaches will continue to increase," Kunda says.
Pursuing Zero Trust
With so much of companies' infrastructure relying on the cloud, executives have increasingly focused on zero-trust frameworks as a way to harden security while still accommodating hybrid workers.
In addition to a secondary code or token offered by two-factor authentication, a variety of other factors can be taken into account, such as the access device, user's location, time of day, and current level of risk for the organization. Depending on those criteria, the user may have an easier authentication experience if they are logging into a network or service from a common location, at a regular time of day, and using a known device.
"An access management tool might collect signals about what kind of endpoint you are working on, where you are in the world, and what your previous access patterns are to determine level of risk," says Michael Kelley, senior director analyst at Gartner. "That determination of level of risk is used to decide how you are authenticated and, potentially, what you have access to, and what kind of access you have once you have been authenticated."
While most modern applications continue to use static authentication, adaptive authentication is expanding. Over the past four years, nearly every provider of access management tools has added some form of adaptive access to their products, he says.
Adaptive access (AA) is a step along the path of zero trust, says Andras Cser, a vice president and principal analyst for security and risk at Forrester Research.
"Adaptive access means lower customer friction as AA solutions only raise friction for those users that indicate [they pose] higher risk levels, [such as] using new devices, using a hitherto unknown IP address geolocation, displaying 'superman' travel — logins in 10 minutes from places that are 1000s of miles apart," Cser says.
About the Author
You May Also Like

