Enterprise cybersecurity technology research that connects the dots.
Longer Support Periods Raise the Bar for Mobile Security
With Google's announcement of seven years of support, other smartphone makers risk falling behind.

Consumers want their devices to be secure and need to be supported for longer, according to Omdia's new survey of 1,578 consumers across 13 major countries in the Americas, Asia & Oceania, and Europe in September 2023. Google and Fairphone are pushing this forward, but governments are also stepping in to ensure security is taken seriously — benefiting consumer safety and the environment.
The Need for Security Updates
While every effort can be put in place by a device manufacturer to ensure the device is "secure by design" or even certified to regulatory or standardized requirements, vulnerabilities are constantly evolving. Updates are key to ensure that new vulnerabilities are found and remediated in a timely manner.
This is happening as consumers increasingly use their mobile phones for sensitive activities such as online banking, identity verification and even relying on services such as Apple or Google Pay.
The update support period is therefore crucial, as well as the frequency of updates and the ability for security-specific updates to be rolled out independent of wider software updates — which is now offered by many of the leading smartphones.
How Much Support Do Consumers Need?
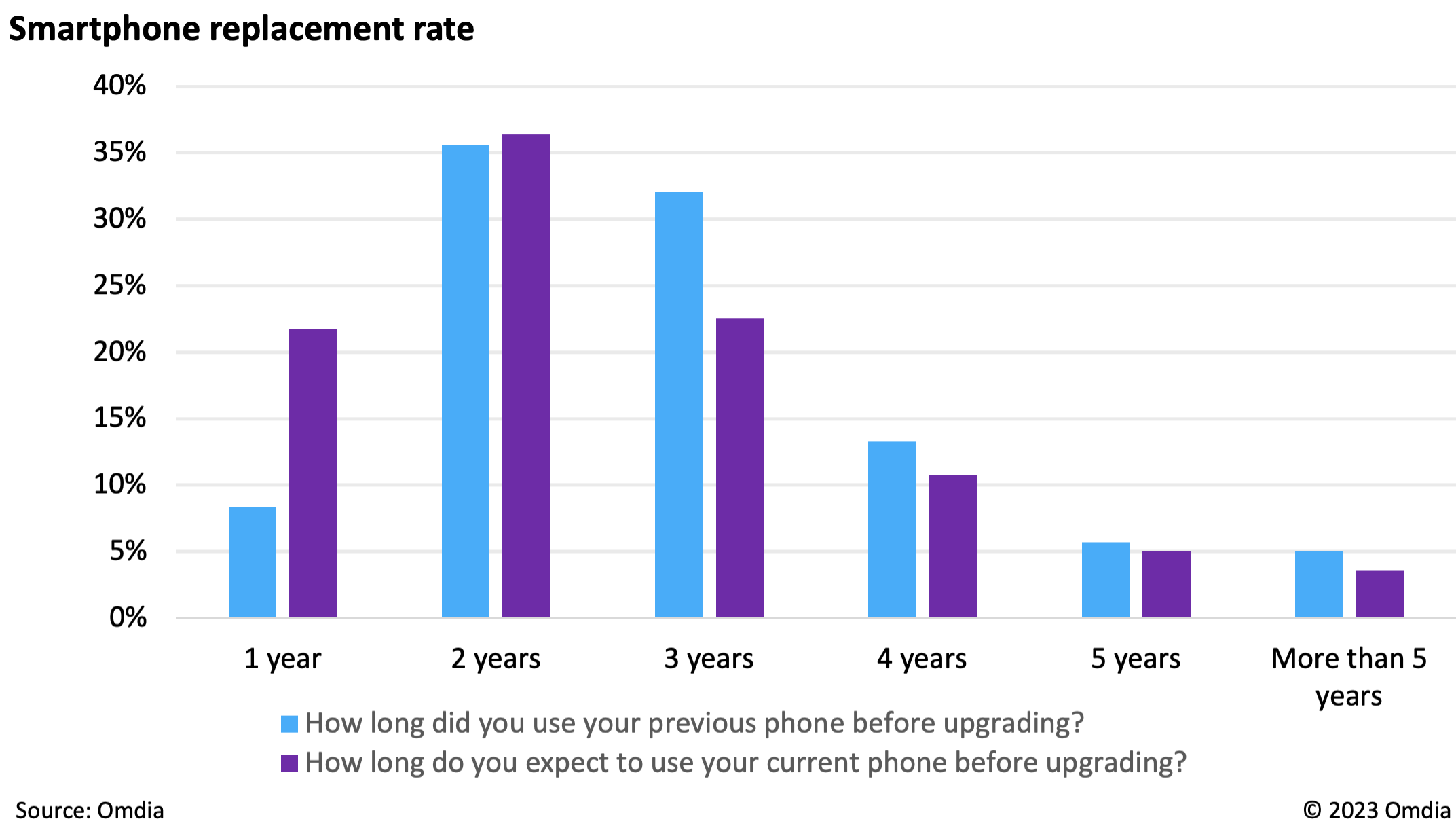
Security update periods and replacement cycle rates are frequently a topic of discussion among those pushing for sustainable tech. There's also skepticism as to how long devices should realistically be updated for, with some questioning the usefulness of five-year+ support.
However, shedding light on the actual usage of mobile devices makes it clear that the longer the support, the better — for both security and sustainability. As such, we asked consumers how long they are using their smartphones.
Security updates for many phones under $500 only last two years, yet 56% of consumers used their previous phone for longer. While premium phones typically have five years' support, more than 5% reported that they kept their previous phone longer — beyond the support of any phone available at the time. This also doesn't take into account how late after release the consumer is buying it; if you bought a Samsung Galaxy S22 Ultra now, you'd get a little over three years of support. If you bought a refurbished iPhone 11, you'd get under 1 year. This is effectively stifling a growing second-hand phone market — and leaving those devices potentially vulnerable.
Currently the only phones to offer more than five years of guaranteed security updates are the Google Pixel 8 and Pixel 8 Pro (seven years) and the Fairphone 5 (eight years). Longer updates can help to slow replacement and production rates, effectively keeping working phones in consumers' hands for longer. By reducing phone production, it drastically reduces the environmental impacts of the smartphone industry.
Source: Omdia
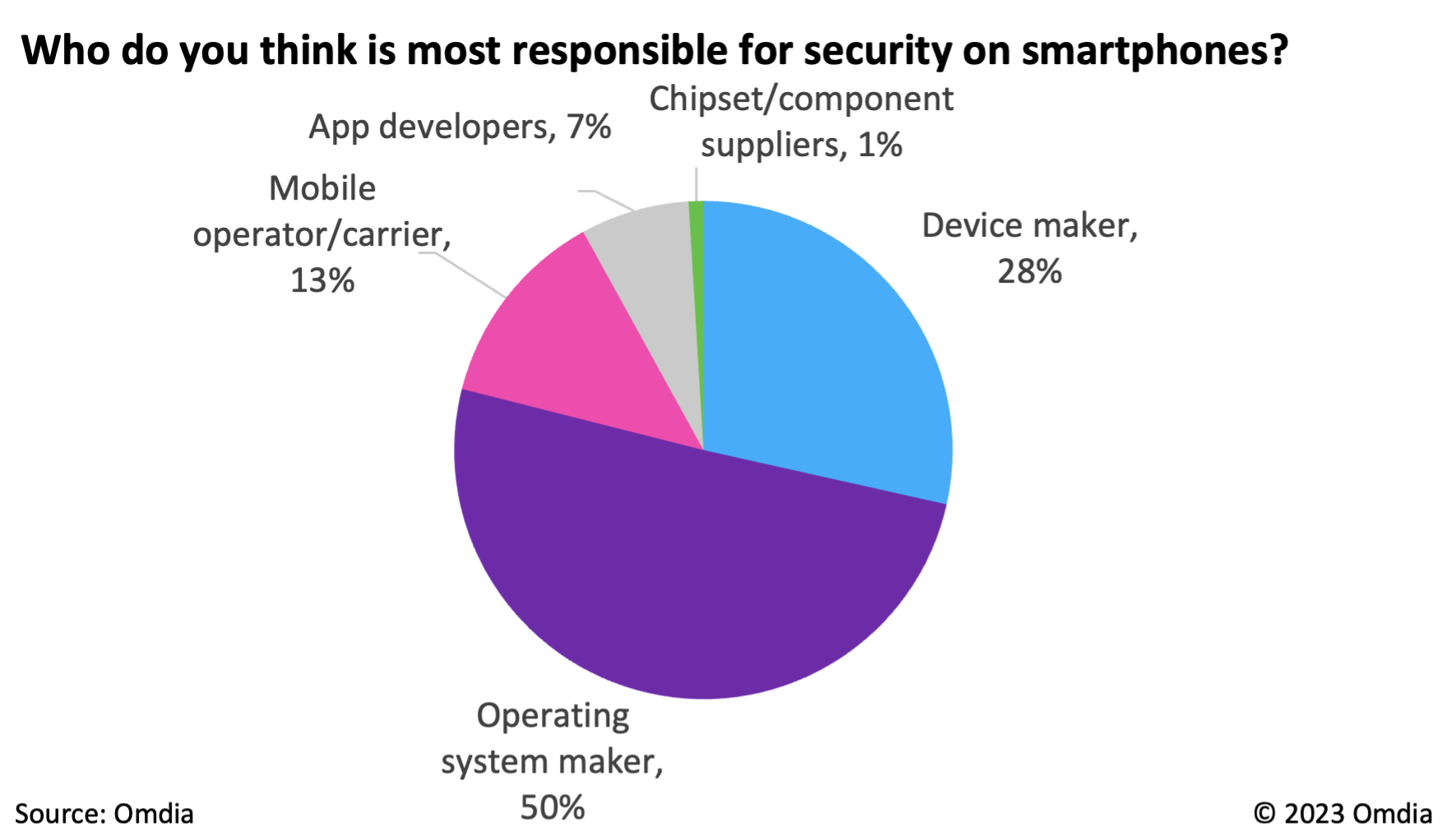
Who's Responsible?
Fifty percent of consumers believe it should be the operating system developer (either Apple or Google) that is responsible for the security of their smartphone. However, how long a phone is supported is primarily down to the device maker and its negotiations with the chipset maker.
Apple and Google are in the unique position of making their own chip, device, and operating system. They are, therefore, their own arbiters. This is likely how Google can commit to seven years — but for Samsung and other Android brands, it would be a more complex process.
Ultimately, regulatory pressure, discussed below, will put mandatory security requirements on device manufacturers, and in some cases importers and distributors, to ensure device update transparency.
Source: Omdia
Security Is a Key Purchase-Driver
Consumers have security top-of-mind when considering their next phone. Forty-six percent confirmed better security features would be a purchase driver, while just 7% said no.
Sixty-nine percent of survey respondents said good security features were critical or important when deciding which smartphone to purchase, although this is second to key hardware specs such as long battery life, durability, and processor speed. When comparing two similar phones, security and brand trust could become the most important and deciding factor.
Governments, Policymakers and Standards Bodies Must Step In
There has historically been a lack of standardization and transparency from equipment manufacturers on security measures for their devices. As a result, governments and standards bodies are developing standards to define baseline requirements, defining product labels to increase consumer visibility and choice, and eventually mandating minimum security requirements.
For example, while Apple has historically given five years of support, it's not transparent at launch; if you just bought a new iPhone 15, you have no official commitment from Apple that it will be supported for two years or five. But with the UK's Product Security and Telecommunications Infrastructure (PSTI) Act, the support period must be stated at the point of sale, from April 2024.
The UK PSTI is just one example, with guidance and legislation being proposed in the US, EU, China, Japan, Korea, and more. While mobile devices are sometimes out of the scope of IoT legislation and government guidance, the proposed EU Cyber Resilience Act will include operating systems for mobile devices — mandating security updates for at least five years, among other requirements.
All manufacturers of connected devices should prioritize and adopt standards and guidance such as the widely referenced ETSI EN 303 645 (Cybersecurity for Consumer IoT) or TS 103 732 (Consumer Mobile Device Protection Profile) to future-proof for upcoming regulation. Further, although at the current time labelling is voluntary, device makers can and should ensure and empower consumer choice by opting in to labelling and certification schemes.
About the Authors
You May Also Like