Identity Protection 101: Building a Modern ITDR Practice
Identities are your new corporate security boundary. Put the right identity threat detection and response (ITDR) in place before it's too late.
January 22, 2024

By Rob Lefferts, Corporate Vice President of The Threat Protection organization, Microsoft
How would you prove you are you? What sounds like a discussion for Philosophy 101 is one of the biggest challenges security and identity teams face thousands of times every second. Identities have become one of the most common cyber-threat vectors. For example, Microsoft blocks more than 4,000 identity attacks every second.
Why Identities? Why Now?
A digital identity is a collection of unique identifiers or attributes that represent a human, software component, machine, asset, or other resource. These attributes are typically used to authenticate and authorize access to corporate resources. Proving who you are often occurs at login where you provide two or more verification factors. These can be something only you should know, like a password, or something only you should have, like a device, security key, or biometrics (fingerprint).
So why does any of this matter? Various trends have pushed identities to center stage in defining your organization's corporate security boundary. For instance, controlling digital access used to rely on traditional network controls when most of the data, applications, and employees were located within the corporate network. The rapid increase in cloud applications and remote workers means that the physical barrier is gone, and managing access to your corporate resources now hinges on identities. By adopting a comprehensive defense-in-depth strategy that spans identity and security, you can help your organization be better prepared for the opportunities and challenges we face in 2024 and beyond.
How to Build an Effective ITDR Practice
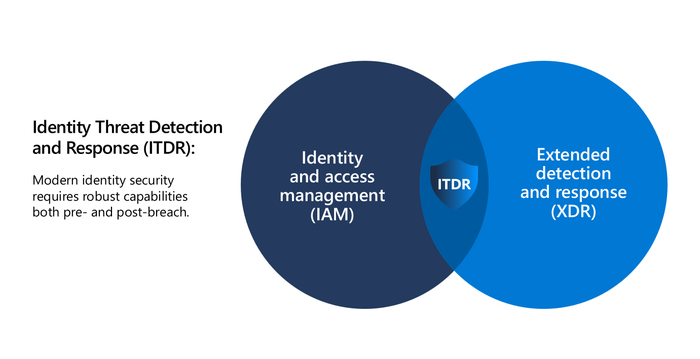
While the idea of identity protection isn't new, identity threat detection and response (ITDR) is emerging in the market. Successful ITDR practices start with an integrated partnership between identity and access management (IAM) and security operations center (SOC) teams.
At its core, this approach is about having the right mix of pre- and post-breach capabilities, where pre-breach measures are designed to prevent and mitigate potential threats before they happen, and post-breach methods focus on quickly detecting and responding when they do.
Neither prevention nor detection capabilities alone are enough; successful ITDR strategies require a comprehensive mix of both.
Pre-Breach: Preventing Security Incidents Before They Happen
Pre-identity breach measures refer to the capabilities that enable a zero-trust security strategy. The zero trust security model assumes a breach and verifies each request.
In the context of ITDR, this means that whenever an identity attempts to access a resource, you must verify that identity with strong authentication and ensure access is compliant. By leveraging real-time data and insights to dynamically change whether access should be granted, organizations can better prevent compromise with secure, adaptive access.
The real magic behind these conditional access policies is advanced user and entity behavioral analytics (UEBA) capabilities that provide real-time data and insights into the potential risk. Using behavioral baselines, UEBA can flag the slightest anomalies and trigger additional investigation or authorization requirements. For instance, if a user consistently logs in from a device in country A but then moments later those same credentials are used from country B, the identity may be compromised and thus the risk associated to that user would be elevated and additional verification such as multifactor authentication or a password change would be enforced.
Another core preventative element of ITDR is posture. The cybersecurity landscape is constantly evolving, and organizations need ongoing insights into their changing IT footprint to understand vulnerabilities and lateral movement paths. ITDR solutions need to give you this level of insight and recommendations on how to limit your exposure.
Post-Breach: Minimize Impact by Catching Threats Early and Taking Decisive Action
The zero-trust principle of assuming a breach highlights the fact that while preventative measures are fundamental, effective post-breach detection and response capabilities are equally critical and therefore key to a successful ITDR practice.
To that end, identity detections help spot anomalous activity after access has been granted, using UEBA and other identifiers of compromise. However, identity detections are only as powerful as the data that feeds them, so you need comprehensive coverage for your unique landscape. This should include support for on-premises and cloud identities, as well as all relevant infrastructure components including federation services and certificate services, as cybercriminals will look to exploit even the smallest gap in protection.
To detect sophisticated attack strategies such as adversary in the middle, identity detections alone are not enough. ITDR needs to be a core element of your broader extended detection and response (XDR) system to correlate identity signals with signals from endpoints, email, software-as-a-service (SaaS) apps, and cloud workloads to understand and identify complex threats. Correlating a broad set of signals will enable SOC teams to gain complete visibility into advanced attack techniques and enable a faster response, while leading XDR systems can even automate the disruption of those attacks.
For example, an integrated and comprehensive XDR system would piece together the execution of a suspicious script on an endpoint, connections to unusual external Internet protocol (IP) addresses, account logins from untrusted locations, and unusual lateral resource access patterns to form a bigger picture, even with a sophisticated attacker moving "low and slow."
Lastly, due to the rapid innovations in artificial intelligence (AI), automation is reshaping the ability of security and identity teams to handle attacks. Check that your ITDR vendor is effectively implementing AI to upskill your talent and allow them to use natural language to complete even the most advanced tasks.
Streamline Your Approach Across Security and Identity Teams
ITDR is critical to any modern identity security practice. A "defenders building defenses" mentality leverages internal expertise in identity and security to help organizations better protect their identities. Apply a similar design goal to building an effective ITDR practice within your organization by having your identity and SOC teams work seamlessly in tandem to effectively protect your identity landscape.
About the Author

Rob Lefferts is corporate vice president of The Threat Protection organization at Microsoft. He leads the team responsible for Microsoft Defender XDR and Microsoft Sentinel products which provide end-to end comprehensive and cohesive Microsoft security experiences and technology for all of our customers. Lefferts holds a BS and MS from Carnegie Mellon in Pittsburgh, Pa.
Read more about:
Sponsor Resource CenterYou May Also Like



