Beware Weaponized YouTube Channels Spreading Lumma Stealer
Videos promoting how to crack popular software circumvent Web filters by using GitHub and MediaFire to propagate the malware.
January 9, 2024
Attackers have been spreading a variant of the Lumma Stealer via YouTube channels that feature content related to cracking popular applications, eluding Web filters by using open source platforms like GitHub and MediaFire instead of proprietary malicious servers to distribute the malware.
Researchers at FortiGuard said the campaign is similar to an attack discovered last March that used artificial intelligence (AI) to spread step-by-step tutorials on how to install programs like Photoshop, Autodesk 3ds Max, AutoCAD, and others without a license.
"These YouTube videos typically feature content related to cracked applications, presenting users with similar installation guides and incorporating malicious URLs often shortened using services like TinyURL and Cuttly," Cara Lin, Fortinet senior analyst, wrote in a blog post published Jan. 8 by Fortinet.
Links shared in the videos use link-shortening services like TinyURL and Cuttly, and lead to the direct download of a new, private .NET loader responsible for fetching the final malware, Lumma Stealer, she wrote.
Lumma targets sensitive information, including user credentials, system details, browser data, and extensions. The malware has been featured on ads on the Dark Web and a Telegram channel since 2022, with more than a dozen command-and-control servers in the wild and multiple updates, according to Fortinet.
How the Lumma Stealer Attack Works
The attack starts with a hacker breaching a YouTube account and uploading videos that purport to share tips on cracked software, accompanied by descriptions of the videos that embed malicious URLs. The descriptions also invite the users to download a .ZIP file that includes malicious content.
The videos observed by Fortinet were uploaded earlier this year; however, the files on the file-sharing site receive regular updates, and the number of downloads continues to grow, suggesting that the campaign is reaching victims. "This indicates that the ZIP file is always new and that this method effectively spreads malware," Lin wrote.
The .ZIP file includes an .LNK file that calls PowerShell to download a .NET execution file via the GitHub repository "New" owned by John1323456. The other two repositories, "LNK" and "LNK-Ex," also include .NET loaders and spread Lumma as the final payload.
"The crafted installation .ZIP file serves as an effective bait to deliver the payload, exploiting the user's intention to install the application and prompting them to click the installation file without hesitation," Lin wrote.
The .NET loader is obfuscated using SmartAssembly, a legitimate obfuscation tool. The loader proceeds by acquiring the system's environment value and, once the number of the data is correct, it loads the PowerShell script. Otherwise, the process exits the program.
YouTube Malware Evasion & Caution
The malware is built to avoid detection: The ProcessStartInfo object launches the PowerShell process which ultimately invokes a DLL file for the next stage of the attack, which scans its environment using various techniques to evade detection. This process includes checking for debuggers; security appliances or sandboxes; virtual machines; and other services or files that might block a malicious process.
"After completing all environment checks, the program decrypts the resource data and invokes the 'SuspendThread; function," Lin wrote. "This function is employed to transition the thread into a 'suspended' state, a crucial step in the process of payload injection."
Once launched, the payload, Lumma, communicates with the command-and-control server (C2) and sets up a connection to send compressed stolen data back to attackers. The variant used in the campaign is marked as version 4.0, but has updated its exfiltration to leverage HTTPS to better evade detection, Lin noted.
However, infection can be tracked. Fortinet included a list of indicators of compromise (IoCs) in the post, and advised the users exercise caution regarding "unclear application sources." If people aim to download applications from YouTube or any other platform, they should ensure they come from reputable and secure origins, Fortinet noted.
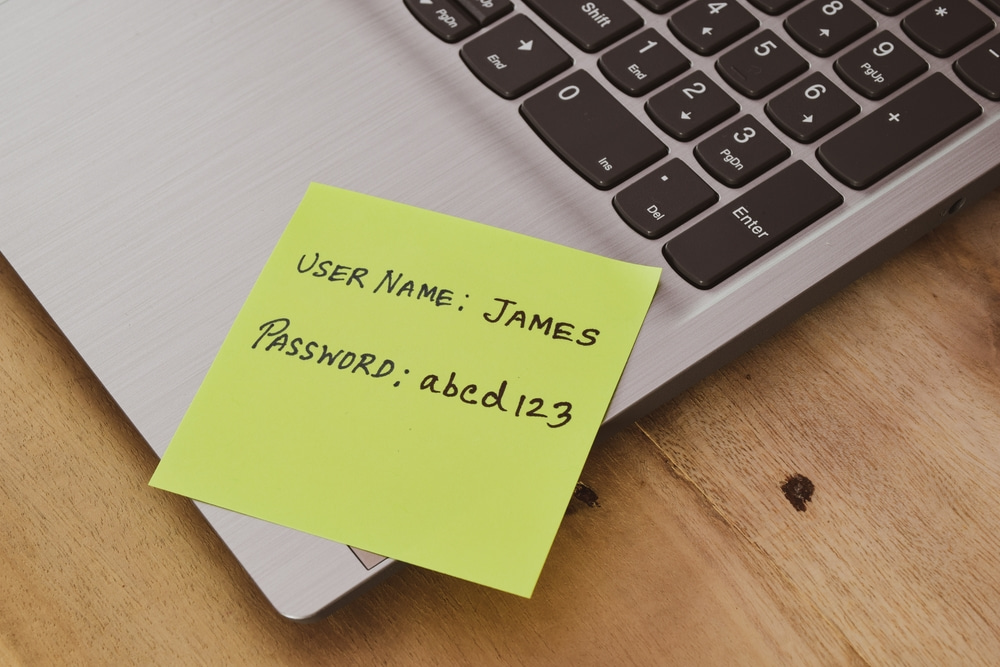
Organizations should also provide basic cybersecurity training to their employees to promote situational awareness about the current threat landscape, as well as learn basic cybersecurity concepts and technology, according to the post. This will help avoid scenarios in which employees download malicious files to corporate environments.
About the Author
You May Also Like
Cybersecurity Day: How to Automate Security Analytics with AI and ML
Dec 17, 2024The Dirt on ROT Data
Dec 18, 2024




