
News, news analysis, and commentary on the latest trends in cybersecurity technology.
Technology Firms Delivering Much-Sought Encryption-in-Use
If the approaches stand up to scrutiny, companies may soon be able to encrypt most databases in a way that allows using data without the need to decrypt to plaintext.
March 17, 2023

Pervasive encryption that protects data not just in transit and at rest but in use — thus freeing companies of the fear of data breaches — has long been a dream of business executives, IT teams, and compliance professionals.
In 2023, those dreams may become a practical reality, with a number of database and data-security firms releasing software to allow companies to keep data encrypted while still allowing common operations, such as searching. Last year, for example, database-technology provider MongoDB released a preview of its Queryable Encryption capability, which allows companies to search for data records in "expressive" ways without needing to decrypt the data. And this week, data security firm Vaultree released a software development kit to allow application makers to try its Data-in-Use Encryption feature, which — the company says — allows more extensive operations on encrypted data.
The goal is to allow companies and their applicationsto access and search databases efficiently, while preventing unauthorized users from ever decrypting sensitive information, says Kenn White, security principal at MongoDB.
"What we hear a lot from customers is concerns around leaks, breaches, and attacks on public cloud infrastructure, including privileged users, and so we're focused on areas where we can add additional security controls and technical measures to limit who can see sensitive data in real time," he says. "[W]e believe [encryption-in-use] will continue to be an area with a lot of potential for innovation, particularly for operational workloads."
The technologies promise to help organizations minimize the so-called "blast radius" when a network or system is compromised. Typically, businesses suffering a breach face a cascade of forensic investigations, regulatory filings and fines, and the potential exposure of sensitive data and intellectual property. Encrypted data allows companies to sidestep many of the devastating impacts of a breach, but it has typically required complex data architecture designs to make sure plaintext information is not inadvertently left insecure.
Many technology companies have attempted to solve the problem and allow the secure use of data by applications by extending the use of encryption. In the 2010s, for example, Ionic Security aimed to encrypt all data on the fly and only allow its use by authorized users with specific privileges. Twilio bought the company in 2021.
If the current crop of technologies succeed where others have failed, companies could see significantly less risk in the event of a breach, says Ryan Lasmaili, CEO at Vaultree.
"We know if there's a leak and the data is fully encrypted, it reduces the company's risk immediately to regulatory compliance," he says. "But GDPR right now, for example, does not cover data-in-use encryption because, to date, it has been seen as not being there yet."
Avoiding Llamas in the Indy 500
MongoDB's Queryable Encryption encrypts database fields, meaning that the information is cryptographically secure at all times, yet it can still be used for searching. The keys for decrypting the information are stored with each client, giving only specific people and devices the ability to decrypt sensitive fields. Even a database administrator cannot decrypt every field unless they have the proper keys.
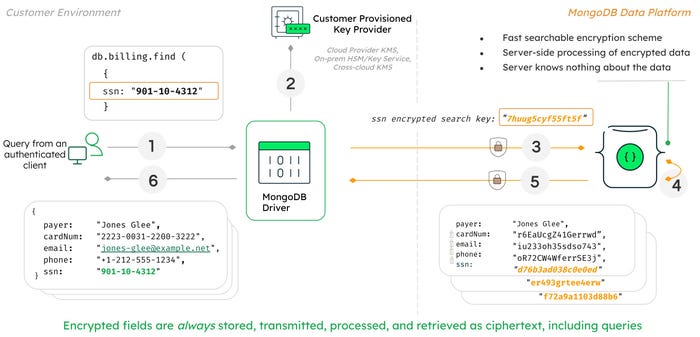
A flow chart of how Queryable Encryption works. Source: MongoDB
Making the technologies a reality relied on research by small groups of academic cryptographers. Queryable Encryption, for example, came from the work of Seny Kamara and Tarik Moataz, both of Brown University, who went on to create a startup, Aroki Software, which was purchased by MongoDB in 2021.
The goal of Queryable Encryption is to deliver technology today that can handle queries that are actually useful and make the capability easy for developers, MongoDB's White said during a presentation at the USENIX ENIGMA Conference in January. Key to all if that is that performance should not get in the way, he said.
"It has to be sub-linear — the difference between 1,000 documents, a million, 5 million, and 100 million documents, it should be sub-linear," he said. "A lot of the academic work had been done in a way that was super-linear, so it works great on 10 records, or 100, 1,000, 5,000 — beyond that, it's painful. And you can throw more CPUs at it, but, you know, it's kind of like racing the Indy 500 with llamas — there's only so much you can do."
Other technologies, like fully homomorphic encryption (FHE), promise to allow a more extensive range of operations on encrypted data and have been extensively funded by the US Department of Defense. A team from Intel and Microsoft signed a multiyear research grant with the DoD in 2021 under the DARPA Data Protection in Virtual Environments (DPRIVE) program to create a hardware accelerator to speed up the notorious processing-intensive FHE approaches. In January, Duality Technologies, another DPRIVE grant recipient, announced it was named to Phase 2 of that program to accelerate machine-learning processing on encrypted data.
"Structured encryption, like most encryption schemes, protects data confidentiality — this means that data is protected in a way where only people approved to receive the data actually have access to this data," says Kurt Rohloff, chief technology officer at Duality Technologies. "FHE also provides data confidentiality, but allows more processing on the data without requiring decryption."
More Testing Needed
New encryption models and technologies typically require a marathon of testing and evaluation. MongoDB's Queryable Encryption stemmed from academic research on structured encryption, with several papers describing the approach. FHE has had decades of research and open development. Vaultree's Data-in-Use Encryption remains, to a large degree, a black box, although CEO Lasmaili pledges that scientific papers will be forthcoming.
In a blog on the possibilities of pervasive encryption, cybersecurity firm Kaspersky warned that such technologies require a great deal of oversight because even small missteps can undermine the security of the systems.
"This happens to be a common problem of practical cryptography — when the developers of an information system feel compelled to craft something in-house that meets their particular data encryption requirements," the company stated. "This 'something' then often turns out to be vulnerable because the development process failed to take into account the latest scientific research."
While encryption-in-use may claim an early lead because it is usable in its current state, breakthroughs in FHE may win in the long run, especially as quantum computing may end up being a differentiator. FHE continues to have functional and security benefits, especially in a post-quantum encryption world, says Duality Technologies' Rohloff.
"Fully homomorphic encryption does allow many more secure operations on it as compared to general structured encryption," he says. "Not all variations of structured encryption [are] protected against quantum computing attacks, but all used fully homomorphic encryption schemes are believed to be protected against quantum computing attacks."
About the Author
You May Also Like

