Number of iOS devices running malicious apps more than tripled in three consecutive quarters, while infected Android devices remained largely flat, report shows.

iPhones and other devices running Apple's iOS have seen a jump in malicious apps attacking them while Android malware infections have remained largely stable, according to a report released today by mobile security company Skycure.
Enterprise iOS devices scanned by Skycure found 0.65% had "high-severity" malicious apps running on them in the first quarter, up from 0.21% in the third quarter last year, according to Skycure's Mobile Threat Intelligence report. Android, however, remained flat during this time period, Skycure noted.
"iOS is used on one of the more popular devices and that is where hackers are focusing and that is where the money is. A more affluent community tends to use the iPhone," says Varun Kohli, Skycure's vice president of marketing. An increase in sophistication of iOS exploits is also a contributor too, Kohli notes.
Source: Skycure
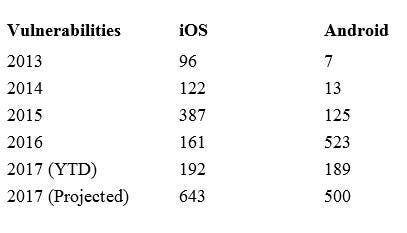
iOS vulnerabilities, meanwhile, have surged dramatically this year, reaching 192 exploitable flaws – far exceeding the 161 vulnerabilities discovered during all of 2016, the report notes. And iOS vulnerabilities are expected to hit 643 this year, a four-fold increase over the previous year, Skycure projects. Android, in comparison, is expected to post a slight dip to 500 from 523.
The report is based on results found from mobile devices Skycure scans from its enterprise customers and also consumers who download its free app. Symantec will soon be able to leverage this capability, given the industry titan recently revealed plans to snap up Skycure.
iOS users overwhelmingly are attentive in updating their software compared to Android users. Nearly 91.4% of iOS users have migrated to iOS 10, compared to the roughly 20.8% of Android users running Android 7, according to the report.
But the proactive OS updates are not preventing the rise in malware and other problems for iOS users.
"Even if it is more patched than Android, malware is only part of the problem," Kohli says. He pointed to three other threats mobile devices face, including physical loss of the device, WiFi network attacks, and vulnerability exploits.
 Black Hat USA returns to the fabulous Mandalay Bay in Las Vegas, Nevada, July 22-27, 2017. Click for information on the conference schedule and to register.
Black Hat USA returns to the fabulous Mandalay Bay in Las Vegas, Nevada, July 22-27, 2017. Click for information on the conference schedule and to register.
Some of the threats Skycure has run across that exploit iOS include the XcodeGhost campaign via the App Store, AceDeceiver malicious app that uses an Apple-approved certificate, and the Yispecter campaign that uses an app loaded from a third-party app store.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




