Experts Urge Firms to Patch Trivial-to-Exploit Flaw in Linux PolicyKit
The memory corruption vulnerability in a policy component installed by default on most Linux distributions allows any user to become root. Researchers have already reproduced the exploit.
January 26, 2022
A local privilege escalation of (LPE) vulnerability in the software used to handle authorizations — and installed by default — on most major distributions of Linux is trivial to exploit, with one researcher already re-creating the attack just from a detailed description of the flaw.
The vulnerability affects polkit, formerly known as PolicyKit, which is included in the default installation of a variety of Linux distributions, including Fedora, Ubuntu, Debian, and CentOS, according to an advisory issued by vulnerability-management firm Qualys, whose researchers originally discovered the issue. Exploiting the vulnerability allows any user to gain root privileges on the system. Security researchers have recommended that Linux administrators, especially owners of multiuser Linux systems, immediately patch this flaw.
The vulnerability is very serious because of how easy it is to trigger the exploit, which Qualys dubbed PwnKit, and how widely used Linux distributions are in enterprises and in cloud platforms, says Bharat Jogi, director of vulnerability and threat research at Qualys.
"A large percentage of today’s IT infrastructure is run on Linux and other open source technologies. Due to the operating system's ubiquity, vulnerabilities found have the tendency to be rather severe," he says. "PwnKit has been hiding in plain sight for 12-plus years with an exploit so trivial that just hours after the vulnerability went live, researchers had already built and released their own exploits."
By yesterday evening, Croatian penetration tester Bojan Zdrnja had reproduced the exploit using the description of the flaw published by Qualys. The exploit was simple to create and "100% reliable," Zdrnja stated in a post on the SANS Institute's InfoSec Handlers Diary.
"I successfully recreated it ... where it is executed on a fully patched Ubuntu 20.04 system—before the polkit patches being installed (sic), which are luckily already out," he wrote. "We expect that the exploit will become public soon and that attackers will start exploiting it—this is especially dangerous for any multi-user system that allows shell access to users."
In the past, LPE vulnerabilities, such as the polkit issue, have been considered second-class vulnerabilities because they are not remotely exploitable. However, attacks increasingly require a chain of exploits to compromise a system, and LPE issues are a critical part of that chain, says Dustin Childs, communications manager at Trend Micro’s Zero Day Initiative (ZDI), a third-party bug bounty program.
"Local privilege escalation bugs should be treated seriously. While these bugs do require previous access to the target system, they are often paired with code execution bugs to take over a system," he says. "These types of bugs are often used by malware and ransomware and should be taken seriously."
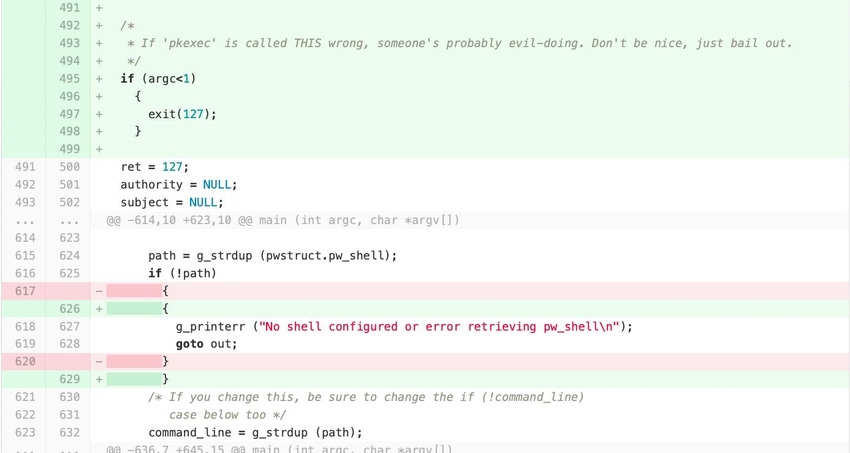
The PwnKit exploits a memory vulnerability in the way that polkit's main executable, pkexec, processes arguments. When sending no arguments, the program is placed in a state that can be exploited, Qualys said. The vulnerability has been assigned CVE-2021-4034 under the Common Vulnerability Enumeration (CVE) system.
The fact that the software is installed by default means the vulnerability represents a widespread risk, say Qualys's Jogi.
"These vulnerabilities continue to underscore the criticality of securing Linux and open source technologies," he says. "Failing to do so could expose critical assets of businesses and organizations across every sector — public and private — and within every industry."
The issue could even impact cloud infrastructure underpinning a variety of applications, since containerized applications and virtual systems often run on Linux, says Karl Sigler, senior security research manager at Trustwave SpiderLabs.
"Any cloud-based system running an affected Linux system would be vulnerable to this, and if the hypervisor is itself Linux based, this could put all virtual systems under the hypervisor at risk," he says.
The issue should be remediated across both enterprise and cloud environments as well, especially any multiuser environments that allow shell access, says Qualys's Jogi.
While the vulnerability has been in polkit since 2009, Linux distributions continue to be one of the most secure operating systems. The issue underscores, however, that companies need to have a playbook in place to quickly remediate critical flaws because you never know when the next widespread issue will be found, Jogi says.
"Although auditing open source software is much easier than auditing closed source software — because the time-consuming reverse-engineering step is not needed — there is still no silver bullet for discovering vulnerabilities," Jogi says. "As researchers continue to do their due diligence in hunting down vulnerabilities, cybersecurity professionals must create processes to prioritize fixes and release patches within their organizations."
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




