Top 10 Security Predictions For 2011
More malware, botnets, and mayhem, including online protests and political attacks, are in store for this year, according to security experts.


Top 10 Security Stories Of 2010
(click image for larger view)
Slideshow: Top 10 Security Stories Of 2010
How didn't the information security landscape change in 2010?
The year began with Google's assertions that the Chinese government had attacked its servers. By the end of the year, the WikiLeaks release of U.S. State Department cables appeared to confirm that was true, thus redefining many people's notions of the extent to which state-sponsored attacks and reconnaissance occur online and provoking furious debates over the freedom of information as well as the Internet.
In 2010, Stuxnet emerged from mysterious origins, proving that malware could have a physical, real-world impact. The volume of malware also continued to rise, as a seemingly nonstop wave of targeted attacks, spam, and botnets continued to target people's personal financial details. In short, little was quiet.
With all that in mind, what's in store for 2011? Here are 10 predictions from security experts:
1) Smaller Botnets Muscle Up
In 2011, malware and botnets will get better, because they're not going to get worse. While security researchers will keep finding innovative ways to combat botnets, "malware authors are finding new ways to evade detection and keep the money flowing," according to a recent report from M86 Security.
Botnets remain too lucrative and pose too little risk to their operators to disappear. Indeed, botnet operators seem relatively immune to prosecution, especially if they're based in Russia (and don't attack Russians). Furthermore, despite some high-profile arrests and takedowns, for example of Lethic, Pushdo, and Bredolab, knocking botnets offline permanently seems difficult.
In fact if anything, the increased tempo of arrests will likely cause botnet creators to better hide their tracks, according to the M86 report."We expect to see the command and control architectures become more and more layered and complex, making it difficult for security researchers and authorities to bring down the entire bot networks."

How Firesheep Can Hijack Web Sessions
(click image for larger view)
Slideshow: How Firesheep Can Hijack Web Sessions
2) DDoS Attacks Deny More With Less
Expect many current types of attacks to become more nuanced, including distributed denial of service (DDoS) attacks. Today, the majority involve brute force -- overwhelming targeted data centers and carrier backbone links with traffic, at a rate of sometimes more than 50 Gbps, said Craig Labovitz, chief scientist at Arbor Networks.
But more pinpointed attacks are also growing more sophisticated and therefore more effective. "Service or application-level attacks may focus on a series of Web or API calls that force an expensive database transaction or calls to slow storage servers," he said. In these cases, brute force isn't required, but rather knowing how, when, and where to strike.
Accordingly, attackers may spend weeks reconnoitering and identifying weak links, then unleash a highly tuned attack that is effective, yet may be barely noticeable. "Unlike massive DDoS traffic floods, application attacks can be far more subtle and may only register as increased load on servers or a precipitous drop in five minute real-time sales revenue charts," said Labovitz.
3) Smartphones Trigger Data Breaches
Consumers will bring their 2010 holiday toys to work. Of course, when those "toys" include devices that can connect to the enterprise network and store sensitive information, organizations must take steps to either block or secure such devices.
The smartphone upside for the enterprise is that workers become more of "an always connected resource -- juggling emails at 10 at night," said Steve Vinsik, VP for integrated security at Unisys. "You're going to be a little more productive, potentially," without the IT department having to budget hundreds of dollars per device, per person. Meanwhile the benefit for workers -- aka consumers -- is they don't need to juggle multiple devices. Plus they get to use their new toy at work.
The downside, however, is that historically when such devices are allowed to connect to the corporate network, little is done to secure them. Accordingly, said Patricia Titus, chief information security officer at Unisys, "security officers and professionals now must figure out how to address the new security challenges that arise as hundreds or thousands of these new devices and their associated applications are introduced into the enterprise infrastructure."
Might it take a high profile disaster in 2011 to really jumpstart mobile device security? Already, many see mobile devices as a data breach disaster waiting to happen. "With just half a gig, you can have half a million data records that outline first name, last name, some contact information, emails. We saw that in the past with laptops, and similarly, lost laptops lead to a lot of data breaches," said Rob Rachwald, security strategist at Imperva.
The difference with mobile devices, however, is that "it's much easier to lose your cell phone than it is to lose a laptop," he said. Accordingly, "some of the same issues that we've seen with data leakage in the past will be deja vu all over again."
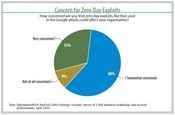
Strategic Security Survey: Global Threat, Local Pain
Strategic Security Survey: Global Threat, Local Pain (click image for larger view and for full slideshow)
4) Hacking Gets Industrialized -- More Effective, Less Expensive
Almost any software development firm or consulting outfit today relies on industrialization -- offshoring highly technical, repetitive, or non-customer-facing project activities to a highly skilled but lower-cost region. Unsurprisingly, the same is already happening with hacking. "A big trend we predict for 2011 is the industrialization of hacking, with advanced persistent treats, and the government folks starting to use private sector tricks," said Rachwald.
On the latter front, for example, 2010 saw at least two incidents where "governments apparently rented botnets to conduct large-scale attacks," he said. In addition, the U.S. State Department cables released by WikiLeaks quoted a source with knowledge of Chinese government activities who said that the politburo had directed the late-2009 attacks against Google.
"What I thought was most interesting was how they described how the Chinese government goes about it. They don't have a dedicated group of people. They hire cyber-mercenaries, if you like, to do what they want to do," he said.
5) Social Networks Feel More Pain
Social networks are predicated on people liking and trusting each other -- they're meant to be online friendships, after all. But with social networks such as Facebook now recording 500 million users, and Twitter 200 million, these sites also provide an effective, one-stop-shop for attackers seeking to extract personal financial information or log-on credentials. "This is because there is more success and payoff in assuming the identity of someone a user knows," according to M86 Security.
Arguably, attackers -- not Facebook, Twitter, or their ilk -- are winning the social networking security wars. "From recent cross-site scripting and cross-site request forgery attacks to the 'likejacking' attacks, increase in spam, and sensationalized headline applications on Facebook, cybercriminals are constantly tooling and retooling, finding ways to exploit the social networks," said M86 Security. Expect this trend to continue in 2011.
6) Crimeware As A Service
In 2011, security experts predict that the cloud computing model -- most famously applied by the likes of Salesforce.com and Amazon.com -- will also become a go-to template for crimeware vendors.
To date, crimeware toolkits have lowered the barrier to entry to conducting online attacks, because they inexpensively automate many types of attacks; no computer science degree or coding acumen required.
Now, according to M86 Security, "our research indicates that a shift is occurring whereby exploit kit developers have started to provide services," as opposed to just selling crimeware applications. "For example, the NeoSploit and Phoenix exploit kits offer different malware services to their customers. With the NeoSploit kit, customers can purchase a specific Web server configuration that redirects victims' requests to a Neosploit back-end server, which is apparently handled by the NeoSploit team."
But don't expect crimeware toolkits to die out. Rather, expect toolkit creators to add malware-as-a-service, providing their customers a bigger choice of attack capabilities.
Inside DHS' Classified Cyber-Coordination Headquarters
(click image for larger view)
Slideshow: Inside DHS' Classified Cyber-Coordination Headquarters
7) Specialized Malware Moves Past PCs And Servers
Stuxnet highlighted how viruses can affect more than just PCs and servers, and Symantec predicts more of the same: "Specialized malware will move beyond PCs and servers, following the lead of the Stuxnet Trojan's recent attack on programmable logic controllers."
Where might the next attack happen? "Any technology that can be exploited for financial gain or influence will become a potential target," said Symantec. Accordingly, attackers will likely target "the obvious targets like smartphones, to any number of less obvious -- yet critical -- systems like power grid controls or electronic voting systems."
On the other hand, Stuxnet's purpose wasn't financial or influential, but rather -- apparently -- to wreck high-frequency drives used to refine uranium. Furthermore, security researchers estimate that the team behind Stuxnet had substantial backing, including a test environment that fully mirrored their target. In other words, Stuxnet may very well have been a one-off.
Accordingly, future Stuxnets would seem to be less of a concern for corporate IT departments than other types of threats. With obvious exceptions made for the odd CEO running a shadow offshore uranium enrichment program.
8) Insider Attacks Still Unstoppable
One 2010 lesson, thanks to WikiLeaks: Never underestimate the security risk posed by a malicious insider. But another lesson might be that it's nearly impossible to prevent such attacks.
"Although sentiment has begun to shift, organizations have traditionally approached information security with a technological focus through investment in firewalls, network detection systems, and monitoring technologies," said John D'Arcy, an information security expert at the University of Notre Dame. "However, these technologies are useless against the motivated insider who wants to damage the organization by leaking sensitive information."
That said, many organizations could close more of their security holes, to at least mitigate the size of any breaches. For example, by December 2010, the Department of Defense -- by its own estimate -- could only track unusual patterns of access to sensitive information on 60% of its systems.
Hence this 2011 prediction: Expect more insider attacks, divulging new information. Notably, WikiLeaks has said it's in possession of sensitive internal documents from a U.S. bank, believed to be Bank of America.

Top 10 Security Stories Of 2010
(click image for larger view)
Slideshow: Top 10 Security Stories Of 2010
9) Government Security Gets A "Fraud Department"
Speaking of malicious insiders, given the embarrassing release of the State Department cables, expect U.S. bureaucrats to demand that their agencies' networks remain locked down, at least until government information security experts better secure them and restrict access.
But will those efforts actually succeed? "Eventually they might be successful, but it's a lot of work to get there," said Impera's Rachwald. "It's the defender's dilemma: you need to lock up everything, and the bad guy only needs to find one hole."
On the other hand, for the government, "this is really going to help them take a look at how they look at file security," he said. The issue isn't just one of data classification, but also establishing identify, as well as each person's normal document-retrieval usage patterns. Expect to see the government borrow a page from credit card issuers' fraud departments. When data-usage patterns start to look unusual, it's time to investigate.
10) Cyber War Vs. Online Protests, Censorship, Political Attacks
Stuxnet. Web site defacement. Operation Payback. What do they have in common? At one point or another in 2010, each was referenced -- often by media outlets or bureaucrats -- as a sign that cyber war was on the rise.
Whether or not that's true, this very discussion highlights how security in 2011 will evolve. "While the Wikileaks and retaliatory attacks may not represent the start of 'cyberwar,' governments clearly view cyberspace as the battlefield of the future," said Arbor Networks' Labovitz. Furthermore, "the trend towards militarization of the Internet and DDoS used as means of protest, censorship, and political attack is cause for concern," not least because it will continue to have an impact on corporate networks and data security.
Expect the "cyber war" debate to keep raging, along with all that it implies. "The world was a simpler place when DDoS was mainly driven by crime, Internet relay chat spats, and hacker bragging rights," said Labovitz.
Welcome to 2011.
SEE ALSO:
WikiLeaks Tests Feasibility Of Government Data Security
Cheap Botnets A Boon To Hackers
Apple, Social Networks Top Cybercrime Targets In 2011
Symantec Finds Stuxnet Targets Iranian Nuclear Enrichment
Read more about:
2011About the Author(s)
You May Also Like
CISO Perspectives: How to make AI an Accelerator, Not a Blocker
August 20, 2024Securing Your Cloud Assets
August 27, 2024




