Survey Findings Show Link Between Data Silos and Security Vulnerabilities
A recent survey showed a surprising correlation between those who operate their businesses with risk and compliance data in silos and those who experienced data breaches in the last 24 months.
April 12, 2023

What are the consequences of operating your business with risk and compliance data in silos? Turns out, it might be more impactful than you think.
A recent 2023 survey of more than 1,000 IT risk, compliance, and security professionals found a correlation between data silos and breaches: namely, that companies operating with their risk management and compliance operations data in silos experienced a higher frequency of breaches.
Let's dig into the data.
Risk Management Confidence Remains High, but Data Silos Persist
First, let's start with risk. Survey respondents take risk management seriously, with a staggeringly high 93% of respondents feeling that they've done well in identifying and assessing risks. Additionally, 56% of infosec professionals are conducting annual security risk assessments, and 27% are conducting biannual assessments, meaning risk management is top priority for respondents. In short, confidence to address risk is high.
_(1).png/?width=700&auto=webp&quality=80&disable=upscale)
However, although respondents grasp the importance of risk management, according to the data, their processes for managing IT risks lag behind their intentions. Despite this overwhelming confidence respondents have about identifying and assessing risks, 51% said they struggle with identifying where the critical risks are to assess what remediations to prioritize. Thirty percent of respondents said their process to identify controls that can mitigate risks does not meet their company's objectives, and 39% of all respondents said they struggle with finding risk-related information when they need it.
.png/?width=700&auto=webp&quality=80&disable=upscale)
Why are survey respondents so confident in their ability to address risks but still struggling to identify risk-related critical tasks? The answer is simple: 90% of surveyed organizations are managing risk management and compliance operations activities in silos, which is opening them up to vulnerabilities. Thirty-eight percent of respondents admitted that they switch between multiple systems throughout the risk management process and that they have separate places for risk assessments vs. tracking remediation efforts, such as multiple spreadsheets containing risk assessment results or multiple platforms tracking risk.
The Connection Between Data Silos and Security Vulnerabilities
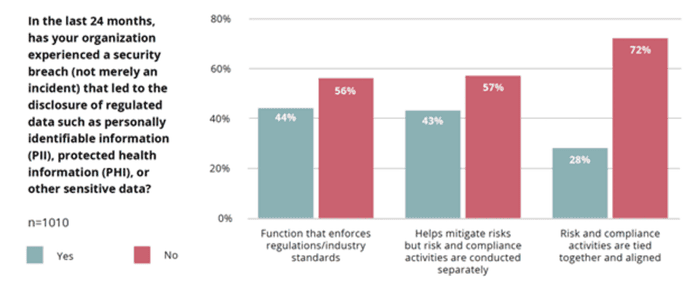
The survey uncovered that only 10% of respondents have an integrated view on how to manage their unique set of risks and have aligned their risk and compliance activities, and organizations that managed risk in an ad hoc manner or only when a negative event happened were more likely to experience a breach.
.png/?width=700&auto=webp&quality=80&disable=upscale)
Let's break these metrics down a little more:
Managing risk ad hoc or in siloed departments had negative impacts on those surveyed: One in two companies managing risk ad hoc or in siloed departments experienced a breach in 2022. Parsing this number further, we saw that 61% of companies that characterized their risk management approach as "ad hoc" experienced a breach, and 46% of those managing risk in siloed departments experienced a breach.
In contrast, only 36% of companies with an integrated approach and manual tools experienced a breach. Additionally, only 30% of companies with an integrated approach and automated tools experienced breaches.
The takeaway? Companies that unified their risk and compliance operations did not suffer the same frequency of breaches, indicating that operating in silos opens companies up to vulnerabilities.
The Power of Unifying Risk and Compliance Data
Although risk and compliance continues to operate in silos, respondents recognize the benefits of changing this reality. Fifty-seven percent of respondents said that having a solid compliance program helps them mitigate risks, even though risk management and compliance activities are typically conducted in response to separate events.
Taking an integrated approach to risk and compliance operations allows organizations to focus on their unique set of risks while avoiding duplicate activities across their risk and compliance management processes. Organizations that take this approach typically start the risk management process with conducting a risk assessment. From there, they create security policies and implement internal controls tailored to the results of their risk assessment. This allows for greater alignment throughout the organization by allowing for input from all stakeholders, not just a select few. Also, it helps create a compliance program that integrates directly with risk operations.
The survey results provided evidence that organizations taking an integrated approach have better security posture than their counterparts who view compliance solely as the function that enforces rules and regulations: On average, organizations that take an integrated approach to risk management experienced security breaches less often than those who view their compliance function as the enforcer of rules. Additionally, as a group, organizations that take an integrated approach spend less time on repetitive and administrative tasks compared to those who believe the compliance function's purpose is to enforce the rules.
To learn more, read the full survey report here.
About the Author
.jpg/?width=700&auto=webp&quality=80&disable=upscale)
Kayne McGladrey, CISSP, is the field CISO for Hyperproof and a senior member of the IEEE. He has over two decades of experience in cybersecurity and has served as a CISO and advisory board member, and focuses on the policy, social, and economic effects of cybersecurity lapses to individuals, companies, and the nation.
You May Also Like


