Sneaky Windows Folder Poisoning Attack Steals Access Rights
Windows challenge-response authentication protocol could be abused by PC hackers to easily access wider corporate networks.

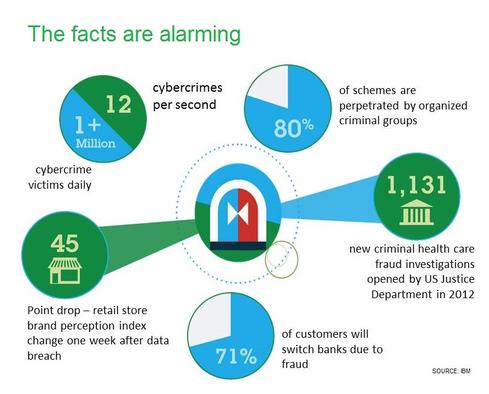
10 Ways To Fight Digital Theft & Fraud
10 Ways To Fight Digital Theft & Fraud (Click image for larger view and slideshow.)
Beware of an attack that uses modified shortcut icons to trick Windows machines into sharing their network-access rights with a hacked PC.
That warning was sounded Tuesday by researchers at data center security vendor Imperva, who said they've discovered a way to poison Windows folders and gain the access rights of anyone who browses to that folder. The hack involves exploiting a relaying feature in Microsoft NT LAN Manager (NTLM), which is a widely used Windows challenge-response authentication protocol.
"Poisoning is a big word for saying I'm creating a file in that folder that has an icon pointing back to my computer; that's GUI stuff," said Amichai Shulman, CTO of Imperva, in an interview at last week's Infosecurity Europe conference.
Anyone who can be tricked into clicking on a folder containing such a shortcut icon will launch an NTLM relay, which passes their authentication credentials via the compromised PC to Active Directory and then gives the compromised PC the same access rights. Furthermore, it's easy for would-be relay attackers to disguise any related malicious shortcuts simply by right-clicking on a shortcut file and changing its icon.
[More than 250 data breaches occurred in Q1 2014, report says. Read Report: Nearly 200 Million Records Compromised In Q1.]
Riffing on the advanced persistent threat (APT) concept, Shulman called this type of attack a "non-advanced persistent threat" since it requires only basic skills but still allows an attacker who's able to hack into a corporate PC -- for example, via a malware infection -- to gain access to further network-connected systems. "Most of the setup is manual, using the GUI, and you probably need to download one tool from the Internet," he added.
Shulman said similar types of attacks can be launched beyond Windows. Other potential targets include Jive, SharePoint, or other collaboration software, especially if it includes the ability to publish small blurbs of information via feeds, together with small images, as these images can used by attackers to point to remote machines and launch NTLM relay attacks.
According to a related research report published Tuesday by Imperva, the flaws that enable this attack to be launched are present in both version 1 and version 2 of NTLM.
{image 1}
While declining to detail exactly how the flaws could be exploited -- and noting that Imperva has no indication that these attacks have been used in the wild -- Shulman said would-be attackers could quickly work out the specifics, if they hadn't already done so. "I think there's enough detail to reconstruct the attack. It's hard not to... it's not like I have to describe some esoteric buffer overflow vulnerability. It's just something you can achieve using a shell command line and GUI in Windows."
The attack detailed by Imperva isn't the first NTLM-related vulnerability to be discovered. Indeed, in recent years, information security professionals have urged businesses to ditch the authentication protocol. "NTLM is to be avoided... especially in high-security environments," said Senne Van Laer, a consultant at ITS Group Benelux, in a 2011 post to the official Microsoft NTLM page inside the Windows Dev Center community.
That's because prior to the attack outlined by Imperva, researchers discovered multiple weaknesses in NTLM that allow attackers who can eavesdrop on an NTLM challenge and response to calculate the hash that's used for authentication. Attackers can then use this hash to authenticate to network resources.
The solution to these NTLM weaknesses is ostensibly simple: Disable NTLM. "However, disabling NTLM can be quite a challenge as authentication with third-party tools, applications or appliances often relies on it, and the fact that Kerberos requires the hostname to be able to authenticate," Van Laer wrote in his post. "A lot of issues can be expected for applications that connect using IP only." Accordingly, he recommends that any organization that still employs NTLM implement strong and long passwords involving more than 10 characters, at least for administrative accounts, to make them less susceptible to rainbow table attacks.
Imperva's Shulman said that NTLM-using businesses can also create baselines of file-access behavior -- users, which files they typically access, and when -- and watch for deviations, which may be signs of high-level abuse patterns.
Cyber criminals wielding APTs have plenty of innovative techniques to evade network and endpoint defenses. It's scary stuff, and ignorance is definitely not bliss. How to fight back? Think security that's distributed, stratified, and adaptive. Read our Advanced Attacks Demand New Defenses report today. (Free registration required.)
About the Author
You May Also Like




