What You Need to Know About Zero Trust Security
The zero trust model might be the answer to a world in which perimeters are made to be breached. Is it right for your organization?
May 22, 2019
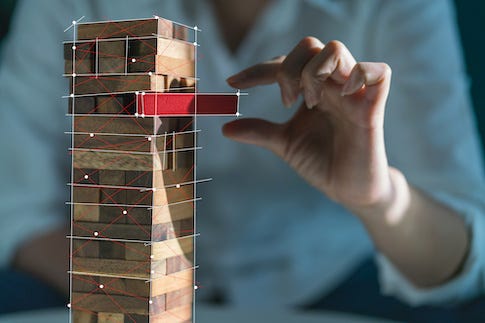
If your network has a perimeter, it will someday be breached. That's both the lesson the "real world" works so hard to teach and the premise behind a key security model: zero trust.
"Don't trust, and verify" might be a nutshell description of the zero trust model — "don't trust" because no user or endpoint within the network is considered intrinsically secure, and "verify" because each user and endpoint accessing any resources of the network must authenticate and be verified at every point, not just at the perimeter or large network segment boundaries.
This often-repeated authentication throughout the network and application infrastructure relies on the concept of "microsegmentation," in which boundaries are defined around individual applications and logical network segments. This kind of frequent check point can go a long way toward putting an end to lateral infection in malware outbreaks, and it doesn't have to be as cumbersome to users as it sounds — as long as technology is used to deal with some of the logins and authentications along the way.
While the concept behind the zero trust model is simple, implementation can be anything but. Before a company decides to invest in the technology and processes, it should understand what is involved in the model and its application. Dark Reading has identified seven issues to resolve before launching into a zero trust environment.
If you have helped your organization move to a zero trust environment, we'd like to hear about your experience. Do you agree with our list? DId you find other issues more important? Let us know in the comments, below.
(Image: whyframeshot VIA Adobe Stock)
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


