Security Geek Gift Guide 2
Whether you're looking for a gift to give at the IT department's holiday party, for your science-loving kids, or for a true friend battling the bad guys in the cube beside you, these gifts are sure winners.
November 30, 2015
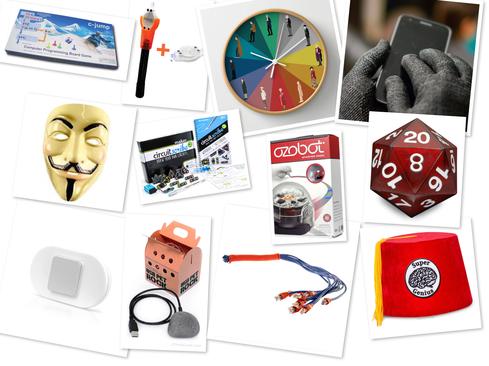
Attention, IT shoppers. Put down those Starbucks sampler packs and generic gift cards. Nothing says "I don't know you that well and don't really care" more than those things. If you are like many folks looking for a creative gift for an office mate, industry colleague, or an otherwise lovable nerd, there's no reason to go that route. In this day and age of geek chic, the creative options for nerdy gift-giving are off the charts. So much so that the options are almost overwhelming. Fortunately, we've done the dirty work and rounded up a whole bunch of fun gifts that will be a hit whether it is for a cube mate, boss' gag gift, office gift exchange, or just a regular old under-the-tree gift for kids or kids-at-heart.
Remember: it’s not just the spirit of giving, it’s also being remembered as the person who bought that really cool gift. Which is just the reputation you want the next time you really need someone to cover your butt when incidents start lighting up the SOC dashboard like a Christmas tree.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




