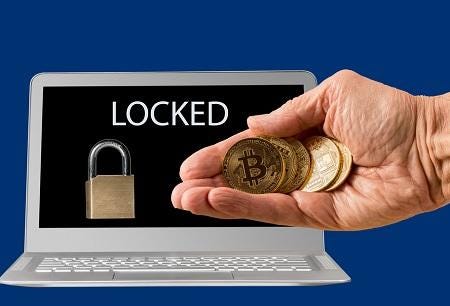
Paying ransom in a ransomware attack isn't recommended, but sometimes, it's necessary. Here's how to pay by cryptocurrency.
Against their better judgment, sometimes IT security professionals are pressured to help their CEOs, chief financial officers, or boards of directors make a ransomware payment.
Paying ransom in a ransomware attack is not as easy as wiring money from a bank, or filling a suitcase full of hundred-dollar bills. Ransomware attacks typically call for sending cryptocurrency to unlock kidnapped data, with values ranging from a few hundred to even millions of dollars
And although traditional financial institutions reportedly are beginning to show interest in cyrptocurrencies, that payment avenue will likely remain blocked for ransomware payments under anti-money laundering and know-your-customer regulations that institutions must abide by. Last year, New York prosecutors charged a Bitcoin exchange operator with violating anti-money laundering laws when it facilitated making a ransomware payment, according to a Fortune report. However, Coin Center, a nonprofit cryptocurrency research and advocacy group, contended it should not be a crime to help ransomware victims.
Meanwhile, cybercriminals are ramping up the deadlines for victims to make ransom payments, or face the potential of having their locked up data, files, photos, and video destroyed. Some attacks delete files if a victim can't meet tight deadlines in time.
"People are being put on a countdown timer and data will be deleted if they don't pay. As a result, companies want to make the payment as fast as possible. Jigsaw, for example, will delete an individual file every hour that you don't pay," says Rick McElroy, security strategist for Carbon Black.
Nearly 60% of employees hit by a ransomware attack at work personally paid the extortion money, according to a new report released today by Intermedia.
While law enforcement as well as security experts in general don't recommend paying ransom, here are seven tips for how to make a ransomware payment in that dire case where there is no other choice.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




