Apple Patches Multiple Major Security Flaws
New security updates cross all Apple platforms.
October 31, 2018
Apple yesterday released security updates to deal with serious vulnerabilities in multiple products including a handful of "critical" flaws that should be patched immediately.
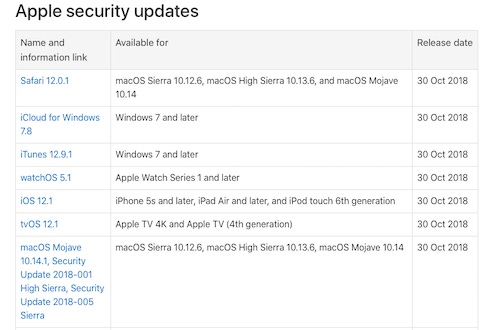
According to US-CERT, the patches released cover Safari 12.0.1, iCloud for Windows 7.8, iTunes 12.9.1, watchOS 5.1, iOS 12.1, tvOS 12.1, macOS Mojave 10.14.1, macOS Security Update 2018-001 High Sierra, and macOS Security Update 2018-005 Sierra. While the patched vulnerabilities are present in a wide variety of products, according to security researchers at Semmle, at least six of the critical vulnerabilities are within the XNU kernel that sits at the core of all current Apple operating systems.
In a post on the Semmle blog, researcher Kevin Backhouse described how he discovered the vulnerabilities using variant analysis to search for patterns in code. In an interview with Dark Reading, Oege de Moor, CEO and co-founder of Semmle, explained that the bugs fall into two categories: "The ICMP packet handler vulnerability is a classical heap buffer overflow. The second second category is the NFS client, and it's responsible for five independent, but highly related, vulnerabilities."
de Moor says that Backhouse found the first of the NFS vulnerabilities through the sort of general code exploration common to threat researchers. Backhouse then used the discovered code to feed a variant analysis engine that ran on other operating systems and found the related vulnerabilities.
"In this case, it's a critical vulnerability, allowing an attacker to mount a malicious NFS volume and gain kernel-level privileges," says de Moor.
According to Semmle's findings, those kernel privileges could allow a malicious actor to read, write, and delete files on disk and in memory, install new applications, or wipe and reset the device to factory settings.
The five related NFS vulnerabilities were patched in macOS with this latest round of updates. The ICMP vulnerability doesn't grant the same depth of privilege, but it has a broader footprint and the possibility of easier exploitation.
Backhouse found a vulnerability in the ICMP packet-handling module in the XNU kernel. de Moor says the bug could be exploited through a classic buffer overflow technique and could allow an attacker to cause affected systems to reboot at arbitrary times. It was remediated in the latest releases of MacOS Sierra, High Sierra, and Mojave; and in iOS 12. It was not, de Moor says, patched for iOS 11, so the roughly 40% of iOS devices that have not (or cannot) upgrade to the latest operating system version are still vulnerable.
Team Effort
While Backhouse was responsible for finding nearly half of the vulnerabilities patched in the latest releases, other researchers also contributed to the vulnerability count.
Jake Massimo, of the University of London, discovered a flaw in the way that Apple implemented a check for prime numbers in its corecrypto module. In his blog post announcing the flaw, Massimo describes how the function can be spoofed into labeling a composite (or non-prime) number as prime, and through doing so render an encryption algorithm far more vulnerable to cracking. Massimo, with colleagues, has issued a full paper on the flaw, with details about the algorithm used to determine whether a number is prime and the effects of getting it wrong.
Apple includes details on all of the new updates on the Apple support site.
Related Content:

Black Hat Europe returns to London Dec 3-6 2018 with hands-on technical Trainings, cutting-edge Briefings, Arsenal open-source tool demonstrations, top-tier security solutions and service providers in the Business Hall. Click for information on the conference and to register.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


