Cyber Forensics: The Next Frontier in Cybersecurity
We can now recover evidence from the RAM on a cellphone, even if the account is locked, and use it to prosecute a case.
November 27, 2017
Every day at Georgia Tech's College of Engineering, my lab helps to solve real crimes through cyber forensics, the application of investigation and analysis techniques to gather and preserve evidence from a computing device that can be presented in a court of law. My research has large-scale crime-solving implications, and my goal is to figure out how we can collect as much evidence as possible from any device involved in the crime to help put away the criminal.
Since I arrived at Georgia Tech, my lab has been hard at work to create forensic techniques that help investigators solve human crimes, in addition to tackling malware and cyber attacks. If someone robs a bank and drops his phone at the scene of the crime, we can mine that digital device for evidence that will help prosecute the case.
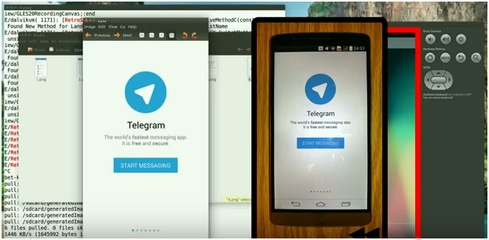
One of the primary focuses of my research is memory image forensics, the process of recovering evidence from the RAM (random access memory) of a device. I recently developed a cyber-forensic technique called RetroScope to recover encrypted information on a device, even if the user has locked his or her accounts. RetroScope leverages a copy of the memory (RAM data) from the device and recreates information such as texts or emails. An investigator can see entire sequences of app screens that were previously accessed by the user.
Terrorists are known to use an application called Telegram that is extremely secure and encrypts everything on the phone. With RetroScope, the data on the phone is recreated and made available to law enforcement. An investigator can see exactly what the suspect was communicating before or during the crime. Any data left on the memory of the device can be extracted and used as evidence.
In a recent case, cyber forensics was used at a restaurant where patrons' credit card information was being stolen. A forensic investigator was called in, but he couldn't crack the case. With more customers being hacked, the restaurant was finally sued, and management called in a more-advanced forensic analyst to look over its systems. The forensic analyst realized there was malware on the restaurant's point-of-sale system, exporting credit card information with each swipe. The hacker was leveraging the volatile RAM (e.g., the system's short-term memory) to hide the malware, and the first investigator missed it.
The first investigator was only considering the static files stored on the disk of the computer. At the time, the forensic investigator wasn't considering volatile RAM as a hiding place for malware. From research like mine, investigators now know that a device's RAM is a viable place to harbor malware. You have to look everywhere in these investigations, leaving no stone unturned. My lab and I are continuing to pioneer the investigation of volatile RAM and the power of memory forensics in cases such as this.
At present, investigating crimes that involve digital devices as evidence is done in a very ad hoc manner, with much digital evidence being left behind. We need to design more holistic cyber-forensic techniques that take into account the entire digital system, and not just a single piece of evidence that investigators happen to find. This requires a paradigm shift in the way people think about cyber forensics. It's no longer just a tool to be used in a larger investigation; it's actually the driver of the investigation itself.
Related Content:

Join Dark Reading LIVE for two days of practical cyber defense discussions. Learn from the industry's most knowledgeable IT security experts. Check out the INsecurity agenda here.
About the Author(s)
You May Also Like
Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




