
Cybersecurity In-Depth: Digging into data about the latest attacks, threats, and trends using charts and tables.
Attackers Have 'Favorite' Vulnerabilities to Exploit
While attackers continue to rely on older, unpatched vulnerabilities, many are jumping on new vulnerabilities as soon as they are disclosed.
Attackers play favorites when looking at which software vulnerabilities to target, according to researchers from Palo Alto Networks.
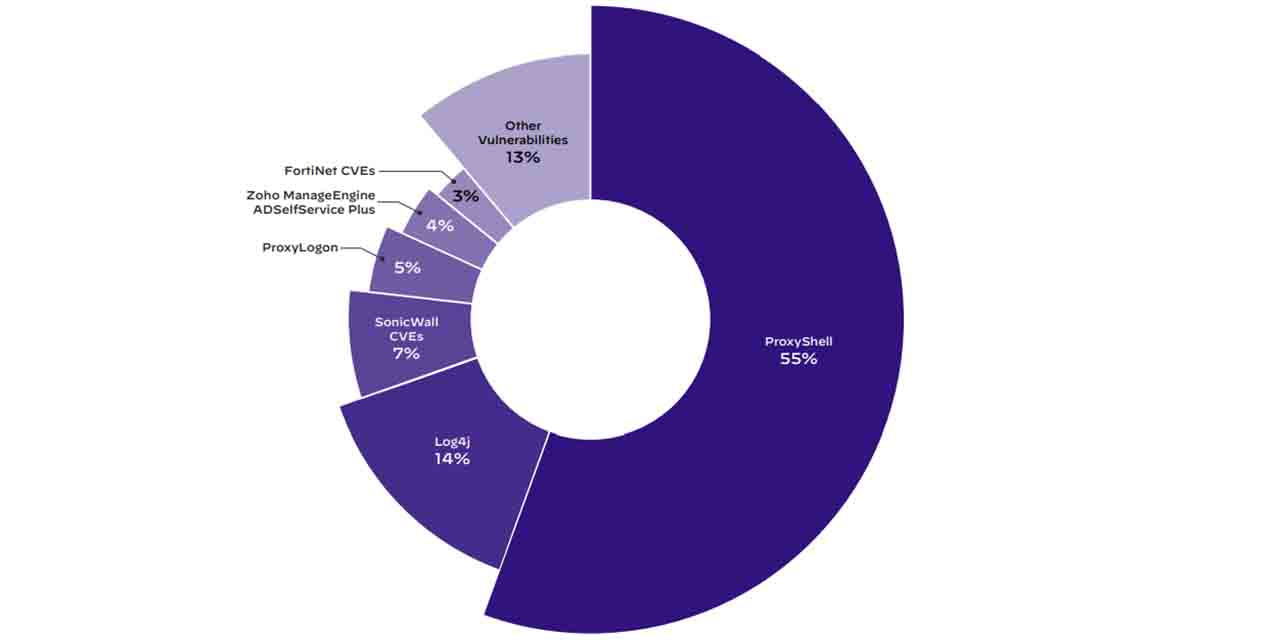
Nearly one in three, or 31%, of incidents analyzed by Unit 42 in its 2022 "Incident Response Report" resulted from attackers gaining access to the enterprise environment by exploiting a software vulnerability. Six CVE categories accounted for more than 87% of vulnerabilities being exploited: ProxyShell (CVE-2021-34473, CVE-2021-34523, CVE-2021-31207), Log4j, ProxyLogon (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065), multiple vulnerabilities in SonicWall and Fortinet products, and a vulnerability in Zoho ManageEngine ADSelfService Plus (CVE-2021-40539).
In 55% of incidents where Unit 42 was able to identify the vulnerability, the attackers had targeted ProxyShell. Just 14% of those cases involved Log4j. Unit 42 researchers analyzed data from a sampling of over 600 incident response engagements between April 2021 and May 2022 for the report.
While attackers continue to rely on older, unpatched vulnerabilities, many are looking at new vulnerabilities as well. Scanning for vulnerabilities is not a difficult task, so attackers begin scanning for systems with a newly disclosed vulnerability as soon as they learn about them.
"The 2021 Attack Surface Management Threat Report [released in April] found that attackers typically start scanning for vulnerabilities within 15 minutes of a CVE being announced," the company said in blog post accompanying the incident response report. "In fact, it can practically coincide with the reveal if the vulnerabilities themselves and the access that can be achieved by exploiting them are significant enough."
As an example, researchers detected scanning and exploitation attempts targeting the authentication bypass vulnerability in F5 BIG-IP appliances (CVE-2022-1388) 2,552 times within 10 hours.
Exploiting software vulnerabilities was the second most common attack method, according to the Unit 42 analysis. The top access vector was phishing. Brute-force credential attacks, primarily targeting Remote Desktop Protocol, rounded out the top three. These three attack vectors made up more than three-quarters of incidents (77%) analyzed in the incident response report.
About the Author
You May Also Like

