Spiderbot, Spiderbot, Does Whatever A Hacker Thought
Virtual machine, she ignores, owns the bot, then controls yours.

At this week’s Intel Developer Forum, CEO Brian Krzanich demonstrated some gesture-controlled spiderbots during his opening keynote that lit up and danced across the stage, entertaining the crowd. These robots spawned from Intel’s investments in the maker movement, demonstrating the limitless creativity and innovation of the developer community.

Big Mama spiderbot, reporting for duty
One significant upside to the evolution of technology is lowering the barrier to entry for developers. Innovations like Intel’s Edison board enable an individual or small team to create sophisticated, autonomous robots in days instead of weeks. During the mega-session of Chris Young, senior VP and general manager of Intel Security Group, the bots were assigned sentry duty, guarding a big donut because software developers need to protect important assets such as sugary food and drinks. All joking aside, the reality is that we really do need to protect key assets, and sound coding is critical to securing our infrastructure.

Spiderbot on duty, guarding the donut
Along with this development agility, however, come new risks that need to be understood by Intel Security and developers. As connected devices become more sophisticated, they are inherently more susceptible to attacks. We took the opportunity during Young’s mega-session to showcase how vulnerabilities in the computing ecosystem can be exploited if platform and application developers are not careful in their coding practices.
We replicated a common cloud environment with multiple virtual machines running on the same physical server. In this case, the robots had a control application running in a virtual machine, which was communicating wirelessly and giving the spiderbot commands. Then we asked one of our senior software engineers, Jenny Mankin, to see if she could commandeer the robot for her own nefarious purposes. She could, and she commanded the robot to stop performing its sentry duty.
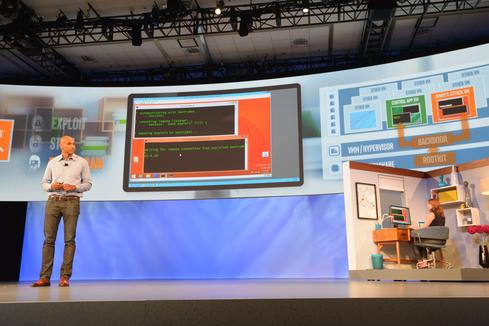
Jenny Mankin commandeering Steve Grobman's spiderbot
First, Jenny needed to steal credentials from the control application in the virtual machine. She took advantage of a vulnerability in the firmware implementation to install a rootkit inside the firmware. The rootkit allowed her to remap memory from the controlling VM to her own VM and monitor all activity in the controlling VM. (For more information on this class of attack, refer to the presentation from Black Hat USA 2015 by Intel’s Advanced Threat Research team.) This is a BIOS implementation vulnerability that breaks the VM isolation, moving the classic issue of privilege escalation in the realm of cloud, virtualization, and the Internet of Things. It also shows the attack technique of lateral movement, where the attacker uses her position in the environment (in this case, being on the physical machine) to take the next step in her attack.
In this case, once Jenny had the credentials she was able to reprogram the spiderbot by sending a return-oriented programming (ROP) exploit remotely to open a reverse-shell on the spiderbot. With ROP attacks, instead of trying to inject her own code into the software on the spiderbot, Jenny uses instructions that are already in memory and exploits a buffer-overflow vulnerability to chain together short sequences of instructions in an unintended order to execute the functionality she wants.
With Capabilities Comes Risk
As IoT devices become connected, we get much greater capabilities, but at the same time we expose ourselves to new risks. I think of the challenges demonstrated last month on automotive hacking, where a remote attacker completely took over control of a car. It is a big issue and one that developers need to comprehend in the world of rapid development, which can lead to quick but sloppy coding practices that are functional but susceptible to security vulnerabilities.
In the short term, our focus is helping the developer community understand good security coding practices. For more information, check out the following resources:
CERT’s Secure Coding standards and practices: https://www.securecoding.cert.org/confluence/display/seccode/SEI+CERT+Coding+Standards and/or https://www.cert.org/secure-coding/
Intel Security using its own secure software/product security practices: http://www.mcafee.com/us/resources/misc/ms-product-software-security-practices.pdf
Book recommendation from our Advanced Threat Research team on good software security practices: "The Art of Software Security Assessment," by Mark Dowd et al.
In the long term, Intel and Intel Security are looking at technology to detect and prevent this type of exploitation so that your spiderbot -- and your donuts -- remain yours.
About the Author(s)
You May Also Like
Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024Finding Your Way on the Path to Zero Trust
May 22, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




