Lack of security talent, low security awareness among employees, and too much data to analyze tops the list of cyberthreats in the 2018 Cyberthreat Defense Threat Report from CyberEdge group.
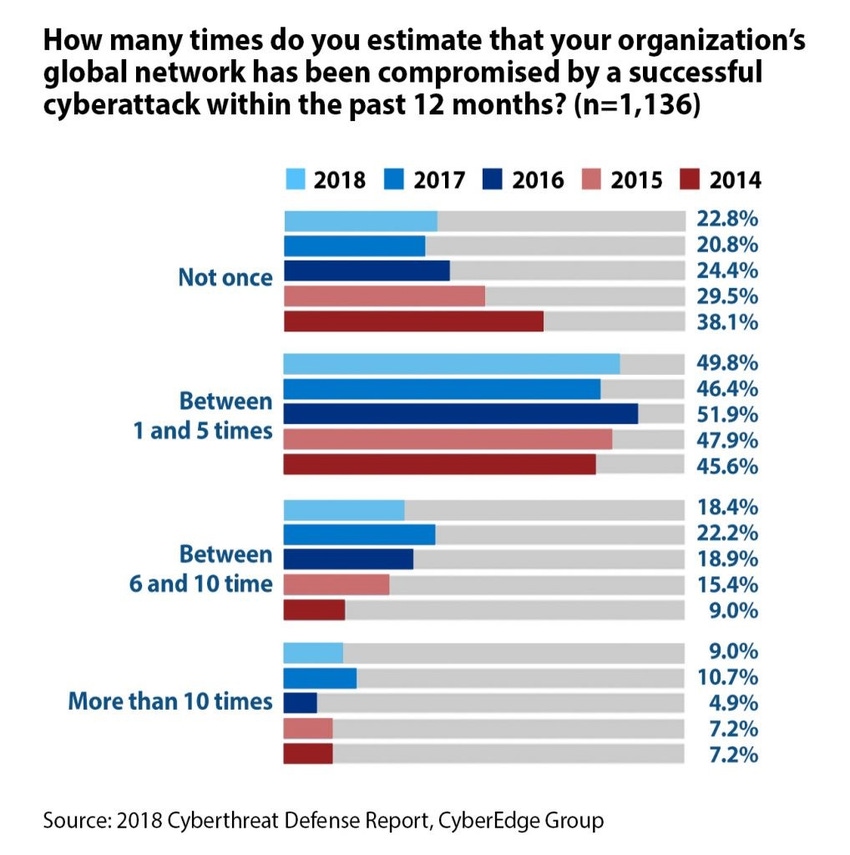
Despite companies increasing their security budgets and investing a fortune in the best cybersecurity tools, organizations today are subject to more successful breaches than ever before – with five million data records lost or stolen every day, according to the fifth annual Cyberthreat Defense Report from CyberEdge group and sponsored by Gigamon. A full 77.2% of respondents report that their company had been successfully breached at least once in 2017, with 27.4% reportedly breached more than six times. More than 62% say they expect to be breached this year.
Even more astonishing is the fact that the high breach counts are occurring despite companies' large investment in security tools. According to the Cyberthreat report, security currently consumes more than 12% of the overall IT budget globally, with security budgets set to rise nearly five percent this year.
Compounding this problem is a lack of cybersecurity talent. Increasing budgets do no good if you can’t find the right people. In 2017, nearly nine out of 10 organizations experienced a shortage of IT security talent, validating recurring headlines about a global shortage of one to two million cybersecurity professionals. This year, there is a slight improvement in the problem organizations face finding security professions with the right mix of security skills, with only eight out of 10 respondents indicating that their organizations are impacted by the security talent shortfall.
Still, it’s first in a list of the highest-rated cyberthreats.

It all adds up to a scary picture, as – despite increasing security budgets - companies struggle to deal with headaches ranging from low security awareness, lack of management support, small budgets, simply too much data even for new tools to analyze, and little confidence in current investments.
Learn more about the 2018 Cyberthreat Defense Report, including an infographic with some of the statistics we used in this blog post and an executive brief that delivers key findings.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




