Profile of a Hacker: The Real Sabu
There are multiple stories about how the capture of the infamous Anonymous leader Sabu went down. Here’s one, and another about what he is doing today.
The capture of Sabu was perhaps the most spectacular fall from grace this century — at least in the security world. He went from being the most beloved figure in the hacktivist group, Anonymous, to being its most hated.
From 2011 to 2012, Sabu was the unofficial leader of the online activist group. He was the charismatic spokesman for Anonymous where there hadn’t been any before—and hasn’t been any since.
During Sabu’s reign, Anonymous became adept at handling the media, making effective use of Twitter to claim victory (even if they were hollow victories at best). Screenshots of "site down" pages were taken, tweeted, and trumpeted to the media, which eagerly wrote about the fearsome prowess of Anonymous. These were the salad days of Anonymous, when they seemed untouchable and everywhere.
To maximize the glory, Sabu collected a smaller cadre of hacktivists from Anonymous and named it LulzSec, which became famous very quickly for a series of high-profile hacks. Where many people passively supported the egalitarian goals of Anonymous, they were turned off by the actions of LulzSec, which were seen as creating much collateral damage to innocent citizenry.
The LulzSec attack of Sony Pictures is an illustrative example. Sony Pictures was running several prize giveaways as part of a marketing campaign. LulzSec used a basic SQL injection to breach the SonyPictures.com database and grabbed the usernames, passwords, and personal profiles of over one million registered users. They then dumped the data to Pastebin. LulzSec’s justification at the time was that Sony Pictures’ security was "… disgraceful and insecure: they were asking for it." But the justification seemed little more than braggadocio to the community. When someone asked LulzSec why they would compromise the credentials of so many innocent television watchers, they replied "we do it for lulz" (the laughs).
Well, LulzSec wasn’t going to keep laughing for long.
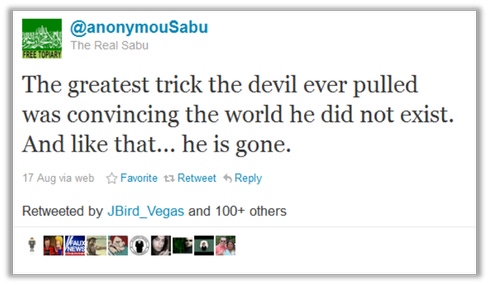
By that time, Sabu had achieved an almost messianic following among Anonymous, and his twitter account, @anonymouSabu, had hundreds of thousands of followers. He was number one on the FBI’s most wanted cybercriminal list.
If that weren’t enough heat, Sabu had also attracted the attention of his polar opposite: the famous pro-U.S., ex-Special Ops service member and hacker known as The Jester. The Jester, too, was known for distributed denial-of-service attacks and had been spending months attacking Jihadist websites in order to drive their users into more centralized, resilient networks where they could be monitored by the various agencies that track terrorist activity.
As an ex-military operative, The Jester loathed Sabu. The two stood at opposite sides on nearly any given topic: WikiLeaks, Anonymous, the Occupy movement, the forum 4chan, the CIA, and the Palestinian/Israeli conflict, to name just a few. One notable exception was the Westboro Baptist Church (WBC), which is known for conducting anti-gay protests at military funerals. Both Sabu and the Jester agreed about this group, and they both attacked the WBC repeatedly.
During the first half of 2011, Sabu and The Jester tried repeatedly to uncover each other’s identity. The conflict between Sabu and the Jester reached a fever pitch at DEF CON 19, the nineteenth annual security convention in Las Vegas. Both hackers claimed to be in attendance along with the 20,000 other hackers, researchers, and undercover FBI agents. The Jester taunted Sabu to come out and meet him face-to-face. Sabu replied that of course he would not. The Jester was suspected to be in collusion with, or at least sanctioned by, the U.S. government. Sabu protested that if he were to expose his own identity, even privately, to The Jester, he would be immediately pounced upon by the authorities.
Sabu did not come out to meet The Jester, and a few months later we found out why. Sabu had already been nabbed and turned by the FBI. There are multiple stories about how the capture of Sabu went down. The simplest one goes like this: Of course, Sabu used anonymization networks to hide his identity and make source tracing impossible. Network anonymization would have been a basic precaution for the most-wanted cybercriminal at the time.
According to one story, Sabu forgot to activate his Tor link a single time, and logged into a server using his real IP address. The authorities traced his real IP address, and Sabu was quickly and quietly detained.
Sabu’s real name, as it turns out, was Hector Xavier Monsegur, from the Puerto Rican island of Viecques. Monsegur had been implicated in, or bragged about dozens of illegal, high-profile hacks, not to mention multiple DDoS attacks. Facing a sentence of 25 to 100 years in prison, he struck a deal in which he agreed to turn over his friends from LulzSec to the authorities.
As part of Monsegur’s plea deal, the authorities were given access to his Twitter account and used it to collect information about Anonymous and LulzSec sympathizers. The judge in Monsegur’s case praised him for his "extraordinary cooperation" with the FBI. Armed with their informant’s information, the authorities apprehended the members of LulzSec. Many are now serving long jail sentences and owe hundreds of thousands of dollars in restitution to the organizations they once brazenly penetrated. Many in Anonymous felt betrayed by Monsegur’s cooperation with the authorities and publicly called him out. He has had little comment about it since.
Monsegur himself was freed on May 27, 2014 after time served. He now lives in New York City, where he, on occasion, gives interviews. He no longer Tweets as Sabu, but instead as Hector X. Monsegur.
With LulzSec members behind bars, and Monsegur neutralized, The Jester went back to attacking Jihadist websites and gathering intel on ISIS. He blogs vociferously against the Trump Administration and maintains a store of "JesterGear" when he’s not running his own Minecraft server.
The Jester remains undoxxed to this day.
Get the latest application threat intelligence from F5 Labs.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




