Report: Only 2 in 3 Cyber Attacks Can Be Stopped with Current Defenses
A recent Bitdefender survey of 250 US IT execs in companies with 1000 or more PCs paints a disturbing picture of cybersecurity preparedness in the enterprise.
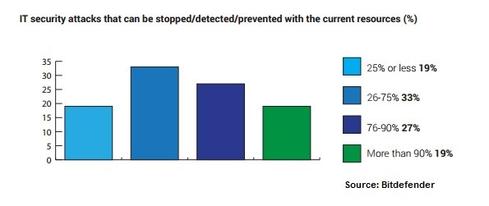
Only 64% of cyber attacks can be stopped, detected or prevented with the current resources, on average, according to a Bitdefender survey of 250 IT decision makers at companies in the US with more than 1,000 PCs.
Bitdefender’s survey shows that 64% of IT decision makers think their IT security budget is sufficient, 2% say the budget is enough, but they are understaffed, and 7% percent say funding is sufficient but can’t accommodate future expansion. Only 3% of IT decision makers surveyed said the security budget in their company is insufficient.
Less than 20% of IT decision makers say they could stop more than 90% of cyberattacks, while another 20% say they could detect and prevent less than a quarter.
Bitdefender’s survey shows 34% of respondent companies were breached in the past 12 months, with 74% reporting they don’t know how their company was breached. As a result, some 73% of IT decision makers fear a breach would force their companies to pay financial compensation, while 66% fear losing their jobs.
Cloud Spending Up
Cloud security spending at 48% of respondent companies increased in the past year while spending for other security activities remained the same, Bitdefender’s survey shows. While almost two-thirds of IT decision makers say their security budget is sufficient, the rest would need an increase of 34% percent, on average, to deliver efficient IT security policies. This is mainly because migrating information from traditional data centers to a cloud infrastructure has significantly increased companies’ attackable surface, bringing new threats and more worries to CIO offices about the safety of their data.
For example, cybercriminals can spend large amounts of time inside organizations without being detected. Advanced persistent threats, or APTs, for instance, are often defined as threats designed to evade detection. In the virtualization paradigm, since nothing being executed in raw memory is encrypted – just scrambled – APTs that try to execute malicious code on a virtual machine can be intercepted by Bitdefender’s Hypervisor Introspection technology long before they actually compromise the operating system. In fact, as soon as the malicious code - even delivered via a zero-day exploit - tries to execute in the VM’s memory, the introspection engine will immediately “see” the malicious action and the code that was trying to execute.
This survey was conducted in October 2016 by iSense Solutions for Bitdefender on 250 IT security purchase professionals (CIOs/CEOs/ CISOs, 26%; IT managers/directors, 56%; IT system administrators, 10%; IT support specialists, 5%) and othersfrom enterprises with 1,000+ PCs based in the United States.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




