Unpatched GPS Tracker Security Bugs Threaten 1.5M Vehicles With Disruption
A GPS device from MiCODUS has six security bugs that could allow attackers to monitor 1.5 million vehicles that use the tracker, or even remotely disable vehicles.
July 19, 2022

Six vulnerabilities have been found in a GPS tracking device used by businesses to monitor vehicle fleets, and by consumers as an anti-theft device. If exploited, they could allow attackers to widely disrupt fleet operations and track individual vehicles.
That's according to cybersecurity firm BitSight, which stated in a Tuesday advisory that the device, the MiCODUS MV720, has vulnerabilities in both the device and the back-end service. These pave the way for man-in-the-middle (MitM) attacks, authentication bypasses, and location tracking. The vulnerabilities include a hard-coded device password that allows access via SMS requests, and a default password on the API server, BitSight found.
"The exploitation of these vulnerabilities could have disastrous and even life-threatening implications," BitSight states in the report. "For example, an attacker could exploit some of the vulnerabilities to cut fuel to an entire fleet of commercial or emergency vehicles. Or, the attacker could leverage GPS information to monitor and abruptly stop vehicles on dangerous highways."
The vulnerabilities include a hard-coded password that could allow commands to be sent to devices, the ability to use administrator privileges for commands, and a default password of 123456. Flaws of lesser severity include a reflected cross-site scripting (XSS) issue and the ability to directly access parts of the application. Five of the vulnerabilities have been assigned identifiers under the Common Vulnerabilities and Exposures (CVE) program: CVE-2022-2107, CVE-2022-2141, CVE-2022-2199, CVE-2022-34150, and CVE-2022-33944. The default password security weakness was not considered a vulnerability, and so did not get a CVE identifier.
GPS Bugs Remain Unpatched
While the company has not observed any signs that the vulnerabilities have been exploited, the Chinese firm that manufacturers the device, MiCODUS, has not responded to attempts at discussing the issues, says Stephen Boyer, co-founder and CTO for BitSight.
BitSight originally contacted MiCODUS about the problems in September 2021, and after an initial request for more information, the company refused subsequent attempts to communicate, according to the firm. MiCODUS did not immediately respond to a request for comment from Dark Reading.
"Unfortunately, the hard-coded password means that the only real remediation strategy is to remove the MV720 device or remove the SIM card from the device," he says. The firm shared the bug information with the Department of Homeland Security, he added, in hopes that it could develop an appropriate remediation strategy.
"IoT devices are full of vulnerabilities, and this will not change going into the future no matter how many of these stories come out," Roger Grimes, data-driven defense evangelist at KnowBe4, said via email. "IoT devices are particularly hard to patch. They should all be auto-patching, but most aren't. Most require end-user interaction, and many times a physical connection."
He added, "If you think it's hard to patch regular software, it's ten times as hard to patch IoT devices. I'm purely guessing here, but I'd speculate that 90% of vulnerable GPS tracking devices will remain vulnerable and exploitable if and when the vendor actually decides to fix them. Hackers love those odds."
IoT: Still No Security by Design, Widespread Threat
The vulnerabilities underscore the risks posed by Internet of Things (IoT) devices that have not benefited from adequate attention to security design and audits. Connected devices typically have less security, but are distributed throughout many companies' infrastructure and handle physical processes — such as entry access and power control — unlike traditional information technology.
Concerned with the lack of security, the US government has established requirements for IoT device security.
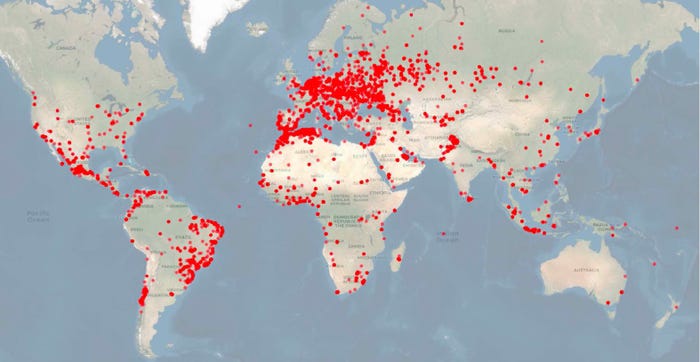
MiCODUS GPS trackers are used by businesses and individuals in 169 countries. Source: BitSight
IoT devices often are also far more widespread than most business users recognize. As shown by the BitSight research, for example, GPS devices in general are used in vehicles belonging to at least five Fortune 50 companies, as well as energy utilities and governments in the Middle East, Europe, and North America.
BitSight could not determine the prevalence of the MiCODUS MV720 specifically, but noted that MiCODUS claims that 1.5 million devices are used globally. In addition, BitSight saw nearly 2.4 million connections to the MiCODUS API server from 169 countries worldwide. The MiCODUS MV720 is a basic model sold for $20 online, but other models could account for some, or even most, of the IoT manufacturer's installed base.
The BitSight report notes that two broad use cases exist for the devices. In some countries, data suggests that the devices are used to manage fleets of vehicles. However, in other countries, the large number of individual connections per capita suggests that individuals are using the devices for anti-theft applications.
"Indonesia has many unique IP addresses communicating with the MiCODUS server, but mostly in the GPS tracker port," BitSight states in the advisory. "This may suggest there are a small number of users with a high number of devices, which is typical in a fleet-management scenario. By comparison, Mexico has a very high number of connections to the web and mobile ports, which could indicate individuals are using the GPS tracker as an anti-theft device."
Mexico, Russia, and Uzbekistan are the countries with the most individual users, the company estimates. Russia, Morocco, and Chile appear to have the greatest number of actual devices.
About the Author
You May Also Like
Cybersecurity Day: How to Automate Security Analytics with AI and ML
Dec 17, 2024The Dirt on ROT Data
Dec 18, 2024




