Standing Privilege: The Attacker's Advantage
The credential is a commodity and will continue to be breached. As a result, focus and spending must shift toward the access that the credentials provide.
The credential has become a hot commodity for hackers, with 74% of breached organizations admitting the breach involved access to a privileged account. In fact, the "Verizon Data Breach Investigations Report" (DBIR) found that out of all attacks, 29% of total breaches involved the use of stolen credentials, second only to phishing. Once a credential is compromised, privileged access management solutions are rendered useless.
The underlying reason behind this is the access credentials provide — specifically, the 24x7x365 always-on, high levels of access that administrator credentials allow, which can be used to move laterally across a network, steal sensitive data, or deploy ransomware. Unfortunately, the average privileged access management or endpoint privilege management solution was not purpose-built to address the risks associated with standing privilege.
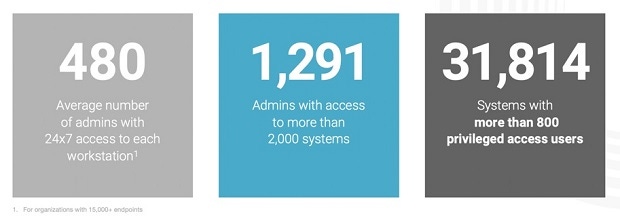
As a result, we discovered that, on average, in enterprises with over 15,000 devices, there are nearly 500 users with admin access to the average employee workstation.
How and Why Does Standing Privilege Get So Messy?
Privileges are typically in the form of group memberships or device-level permissions that allow the execution of privileged commands. Even if a user is not explicitly given access to a server or workstation, that user's domain or group-level permissions often allow access whenever that person needs or wants it.

Figure 2: How administrator privileges spread. (Source: Remediant)
When faced with an IT issue in the workplace, we look for and expect the fastest resolution so we can move forward with our work duties. In the world of permissions, this means access is being provided through groups to IT help desks and server administrators to ensure they can do their job effectively. Managing groups at a granular level becomes very complex very quickly, so admins always tend to have more access than they need. In addition, administrator rights change over time for a variety of reasons; attackers know this and use it to their benefit. The end result: Many security teams are left in the dark. They need to be more diligent when new members are added, and especially as help desk and administrator access is given.
This isn't the only way the amount of privileged access in an ecosystem changes. For example, old members who leave their teams or the company aren't always removed in a timely fashion, group memberships change, local accounts get added and removed, and the list goes on. In some cases, all of these are traps organizations fall into on a regular basis that ultimately result in an invisible sprawl of administrator access across an enterprise. Not only is 24x7x365 access unnecessary for employees, but, more importantly, it's available to an attacker using the average employee workstation as an entry point. If an attacker is able to phish their way into an employee's workstation, that person now has the proverbial "keys to the kingdom."
Addressing the Problem: Introducing Zero Standing Privilege
The reason our industry has failed miserably at addressing standing privilege is because we struggle to answer two simple questions: What admin credentials exist and have standing access? And, how do you protect them?
Coined by Gartner, zero standing privileges (ZSP) is an emerging, reframed approach to privileged access management that addresses both questions.
If we agree that standing privilege is defined as accounts that have persistent privilege access across a set of systems, ZSP is the exact opposite. It is the purest form of just-in-time administrator access, ensuring that the principle of least privilege is enforced by granting, to authorized users, the privileged access they need for the minimum time and only the minimum rights that they need. This elimination of standing privilege through zero standing privilege is really a key inflection point in the understanding of privilege access today. The figure below outlines the risk exposure of an account with standing privileges versus an account in a ZSP environment:

Figure 3: Risk exposure of an account with standing privileges versus an account with zero standing privilege. (Source: Gartner)
To reach this goal of ZSP, begin by measuring the organization's standing privilege to understand what administrator credentials exist. This includes discovering and identifying persistent accounts across workstations and servers, as well as mapping out admin access on a system-by-system basis.
Once standing privilege is measured, it can be managed, and from there it is a phased approach to protecting an enterprise environment and achieving ZSP. Start by "stopping the bleeding" by preventing the creation of new rogue administrator accounts. It is critical that firms have the ability to do this across all types of systems (Windows, Mac, Linux) and all types of access (local, group, domain). Once the "bleeding" has stopped, it's time to determine which accounts are authorized and which accounts are not, and to what systems. Unauthorized access should then be revoked, ideally in bulk, to quickly mitigate one of the accounts being compromised.
The last step to achieving ZSP is to shift administrators into just-in-time mode that allows them to gain access to the system when they need to perform required tasks, but only for the right time frame and only to the right system(s). Access should be revoked once the work is complete and only provisioned back (limited to the right system for the right time frame) when needed again.
ZSP is an inflection point in privilege management. It is encouraging to see the market has started to recognize standing privilege as a key risk that needs to be addressed and that vaulting secrets and rotating local admin passwords on critical servers are not sufficient. Attackers are targeting workstations as the low-hanging fruit and using the admin access available from those workstations to spread across networks.
The credential has become a commodity that will continue to be breached. As a result, the focus and spending must shift toward the access the credentials provide. As an industry, if we do not take a ZSP stance in our environments, stolen credentials will continue as the attacker's low-hanging fruit and continue contributing to 80% of all data breaches today.
Related Content:
 Check out The Edge, Dark Reading's new section for features, threat data, and in-depth perspectives. Today's featured story: "The Entertainment Biz Is Changing, but the Cybersecurity Script Is One We've Read Before."
Check out The Edge, Dark Reading's new section for features, threat data, and in-depth perspectives. Today's featured story: "The Entertainment Biz Is Changing, but the Cybersecurity Script Is One We've Read Before."
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




