Google Targets Deceptive Sites with New Chrome Tools
A new extension and browser alert aim to help users report deceptive sites and prevent them from encountering fraud.
Today Google announced two new features intended to protect Chrome users from deceptive sites, which are becoming a broader threat as cybercriminals advance their fraud strategies.
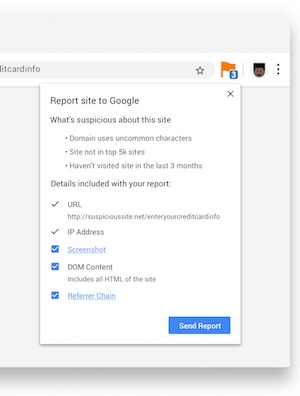
Google Safe Browsing has been blocking phishing attacks for more than a decade, the company reports in a blog post on the updates. It automatically analyzes websites known via Google Search Web crawlers and creates lists of sites considered deceptive or dangerous. The new Suspicious Site Reporter extension lets users help to identify and report suspicious sites.
Those who install the extension will see an icon appear when they arrive on a potentially malicious website, as well as more details about why the site was deemed suspicious. If they click the icon, users can report these unsafe sites to Safe Browsing for further investigation.
Google is also taking steps to weed out deceptive websites with confusing URLs — for example, go0gle[.]com. Chrome 75 will bring a new warning to direct users away from these URLs, which many often click without taking a closer look at the text. The warning compares the URL of the page someone is visiting with URLs of pages the person previously visited. If the URL looks similar and may cause confusion, an alert displays a warning to help the user virtually relocate to safety.
{image 1}
Read more details here.
About the Author(s)
You May Also Like
Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




