Passwords Be Gone! Removing 4 Barriers To Strong Authentication
As biometric factors become more prevalent on mobile devices, FIDO Alliance standards will gain traction as an industry-wide authentication solution.
Everyone knows that passwords are the weakest security for authentication, yet Internet services persist in making consumers use a password as the primary method for online access. For consumers, there are too many passwords to remember, they are difficult to type (particularly on mobile devices), and they are insecure.
More secure authentication options will require users to submit one or two extra “factors,” which may be any combination of something a user (1) knows, (2) has, or (3) is -- the classic definition of "multifactor" or "strong" authentication. Extra factors provide better protection, yet the usual reason against using them is: “Strong authentication has too many barriers.”
New technical protocols developed by the FIDO Alliance are designed to remove the barriers to strong authentication. The main principle behind FIDO is that there doesn’t have to be any tradeoff between ease-of-use and security. The protocols ensure that users receive strong security and the authentication experience is easy to use.
The following describes four major barriers to strong authentication practices and how the FIDO approach can help alleviate the significant burdens they currently place on business.
Barrier 1: Cost
Application providers face a huge business challenge authenticating a mass audience with heterogeneous devices. Scaling a solution for millions of customers with diverse PCs, smartphones, and tablets is often cost-prohibitive.
Even for a cloud-based solution that boasts a lower up-front cost, recurring expenditures can quadruple total cost of ownership (TCO). Its calculation depends on many variables: acquisition, integration, deployment, support, and annual maintenance. Internal costs swell when integrating multiple solutions for strong authentication.
The largest variable is supporting strong authentication for millions of consumers. For example, a physical USB token may cost $30 to $60. Its distribution requires packaging, postage, and support. Physical tokens must be maintained and damaged or lost tokens replaced. Consumers may also need assistance configuring credentials on their smartphones for automatic two-factor authentication via cloud-based solutions. Many calls to help desks are for password resets. Supporting resets for traditional authentication factors on a mass scale could be enormous.
Use of biometrics for authenticating consumer applications could dramatically reduce TCO because these factors are already “deployed,” and sensors for capturing biometrics are rapidly appearing in new-model smartphones.
Barrier 2: Ease of Use
Most consumer applications use simple passwords for authentication due to their ease of use. The business logic for this choice is that ease of use is a higher priority than security, and if the authentication process is too difficult consumers won’t use the provider’s application in the first place.
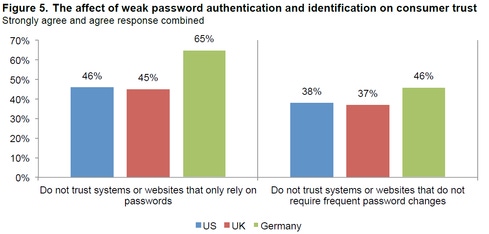
Most consumers, however, are wise to security risks, according to a recent survey by Ponemon Institute. Consumers do not trust systems or websites that only rely on passwords or do not require frequent password changes.
When consumers feel uncomfortable with online security, they withdraw. For example, a Jumio study showed the abandonment of mobile shopping carts is very high. Of the 66% of smartphone and tablet users who have tried but failed to complete a transaction, 51% were uncomfortable entering credit card information. Offering consumers strong authentication is validation of an application provider’s concern for securing personal information -- it’s the way to earn consumers’ trust. Toward this end, a wave of leading consumer applications such as DropBox, Twitter, and Evernote are now offering two-factor authentication (also called “two-step”) to help assure consumers that their data is safe.
Biometrics hold great promise because consumers are already familiar with access that is activated by a voice command, looking into an eye scanner, or pressing a fingertip or palm to a scanner. Fingerprint sensors are becoming more prevalent on mobile devices. In fact, according to Apple, just 49% of its customers used a passcode to log into their iPhones before Touch ID. Now, on the iPhone 5S, 83% of people use Touch ID or a passcode.
Barrier 3: Access Security
Strengthening access security is a key function of strong authentication. The choice of using strong authentication depends on the level of assurance required for a particular use case. Applications requiring a high confidence in user identity must use strong authentication. Applications requiring moderate-to-low confidence in user identity may deploy a single-factor solution.
By definition, strong authentication uses more than one factor -- but that does not automatically make it more secure. The characteristics related to quality of an authentication factor include: 1) The factor is not forgettable; 2) the authentication codes generated are not guessable; 3) the factor is unfeasible to replicate; 4) the factor is not prone to be surreptitiously stolen via the Internet; and 5) the factor is tamper-resistant. Adding higher-quality factors like biometrics or smartcards strengthens the authentication solution.
Barrier 4: Privacy
The privacy barrier relates to the ability of a strong authentication solution to secure factors stored in a user’s authentication profile. The user’s profile may include personally identifiable data such as name, address, birth date, birthplace, mother’s maiden name, Social Security number, credit card information, or biometric information.
All of these are stored somewhere in digital format and are at risk of a breach just like any other data. If centrally stored authentication data is breached, it can be duplicated, modified, and used to the great detriment of the consumer application provider and its users.
Biometric data is especially critical because if compromised in a server breach, the data can potentially be extracted. There are two classes of biometrics pertinent to authentication: anatomical/physiological factors and behavioral factors. Providers that centrally store biometric templates must ensure the safety of this sensitive data. Cloud solutions for strong authentication must include safeguards to preserve privacy.
The FIDO standards are intended to be used by Internet services, component and device makers, and providers of software and stacks. A key enabler for this is the latest generation of smartphones and tablets where biometric factors can be securely stored, and a strong authentication solution can leverage FIDO protocols without centrally stored authentication profiles.
By using FIDO protocols, businesses can lower costs, ensure consumer privacy, enforce stronger assurance of identity, and make strong authentication solutions easier to use.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




