8 Alternatives to Selfie Authentication
How to definitively prove your identity? A variety of anatomical parts and functions may soon be able to vouch for you.
August 4, 2016
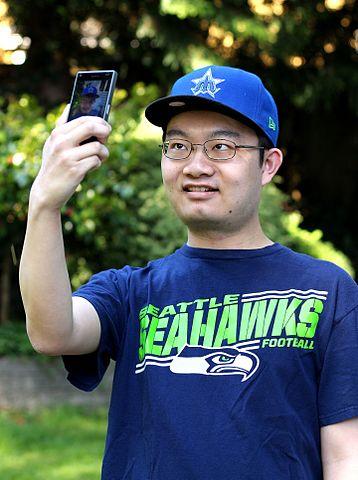
With MasterCard deciding to test the selfie as an authentication method for payments earlier this year, we cheered that the self-authentication conversation had moved beyond fingerprints and retinas. It's a welcome changeup that taps into facial recognition and also requires users to blink into a live camera to ensure it's not a photo of a selfie.
It also got us thinking about other common, readily access physiological features that would determine beyond a doubt, that's you.
So many candidates have come and gone in the last several years. Gait recognition, which collects data on how we walk, emerged post-9/11 for potential use in airports. Voice recognition remains in play, but has challenges with ambient noise, making it difficult to use in a shopping center, on the street or in an airport.
But the more we dug into this, the more we came to agree with noted security expert (and pop singer) John Mayer, that indeed, your body is a wonderland. Researchers and startups are using all kinds of body parts to uniquely and definitively identify us. We've highlighted some candidates here as well as a few that are, well, lighter in spirit.
In the meantime, once you're done closing your left eye and sticking out your tongue to pay down your credit card balance, check out our suggestions for futuristic authentication alternatives and let us know in the comments what we missed.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




