The Phishie Awards: (Dis)Honoring The Best Of The Worst Phishing Attacks
From the costly to the clever to the just plain creepy, here are the recent phishing campaigns that have earned our reluctant recognition.
11 Slides

Phony Breach Notifications
After a phishing attack resulted in the breach at Anthem, other opportunistic criminals took advantage of the unfortunate situation, victimizing some breach victims a second time.
Knowing that people would be on the lookout for breach notifications, they sent out this message:
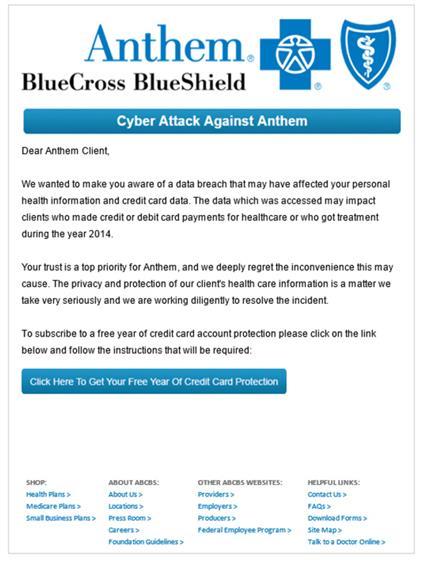
Users who clicked to sign up for credit protection received something much less helpful.
(Message courtesy of KnowBe4)
About the Author
Keep up with the latest cybersecurity threats, newly discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or weekly right to your email inbox.
You May Also Like
More Insights



_Daniren_Alamy.jpg?width=700&auto=webp&quality=80&disable=upscale)
