10 Ways to Prevent Your Mobile Devices From Becoming Bots
Enterprises may not notice a huge impact on their network's bandwidth, but other repercussions may loom in the background.
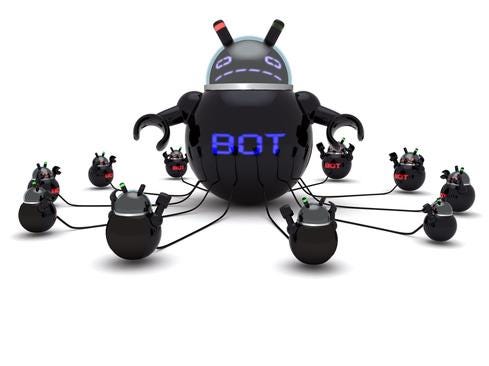
The WireX Android botnet last month snagged tens of thousands of mobile users, in order to wage DDoS attacks against organizations in multiple industries.
While it's clearly taxing to be on the receiving side of a DDoS attack, enterprises that find their mobile devices commandeered as bots also have reason for concern.
"Enterprises may notice their upstream traffic flow will be slightly constrained, but the impact will be negligible," says Robbie Forkish, Appthority CTO. However, Forkish and other security experts note it's still worth a company's time and effort to prevent their mobile devices from becoming bots.
For example, companies may find their IP addresses blacklisted if their mobile devices are swept up into a botnet, notes Andrew Blaich, a security researcher at Lookout.
James Plouffe, lead solutions architect with MobileIron, agrees.
"If you are an enterprise and part of a botnet, then you're consuming bandwidth for things not related to your company," Plouffe says. "Also, it could appear your company is the source of the attack and it could be bad for your company's reputation and you may incur some liability."
In addition to these issues, a company may find that once its mobile workforce is infected with malware, the attackers could turn the bots into another malicious purpose.
"The attacker could change the instructions and have it infiltrate confidential information on the device," says Robert Hamilton, director of product marketing at Imperva.
Here are 10 steps IT security teams can take to reduce the odds their mobile devices will get recruited as bots:
"A lot of enterprises rely on firewalls to keep things out," says MobileIron's Plouffe. "But they can also use firewalls to prevent traffic from getting out. Consider outbound filtering and what you allow out and inspect that traffic."
That advice apparently remains relevant today, even though it was once considered a forgotten technique with the advent of data leakage prevention solutions (DLP) and network access controls (NAC).
Apps that are misbehaving and communicating with an outside server can potentially drain a smartphone battery at a much faster clip than usual, says Lookout's Blaich.
For example, a battery that dies rather quickly, even though the number and type of apps that are running on the device remains status quo should send up a red flag, Blaich notes.
In the case of WireX, the commandeered Android devices could still launch attacks even when the malicious applications were not being used, burning up battery time as a result.
One potential workaround to avoid users loading shady apps on a corporate mobile device is to preload as many apps as possible on the smartphone, Plouffe says.
Most attackers who create botnets rely on social engineering to lure users into downloading malware or clicking on links that will take them to a nefarious site.
"It's better to automate the process so users are not searching for and clicking on things to get apps," he says. "You can automatically deploy the apps or have a safe space where they have been curated."
"Many enterprises have a policy to prevent jailbroken or rooted devices in their environment, because the protection mechanisms Google and Apple build into their devices have been circumvented," says Forkish.
Enterprises are usually able to keep their guard up with MTD, mobile device management (MDM), and enterprise mobility management (EMM) systems, which can usually detect a rooted or jailbroken device on their network, Forkish added.
"For CISOs, specifically, if you have a corporate VPN, keep an eye out for suspicious network behavior that might be coming from a misbehaving application," Blaich advises.
When mobile devices are connected to the network via a VPN, security teams can drill down into any misbehavior by monitoring traffic and reviewing whether it's coming from known malicious IP addresses or domain servers, Blaich adds.
Mobile security tools are designed to scan apps to evaluate them for risky behavior and determine if a device has been compromised, as well as monitor URL traffic, Blaich says, advising enterprises to use such tools.
In addition to mobile security tools, enterprises should also consider adding safe browsing features, says Blaich.
"You can scan apps and remediate, but with safe browsing you can stop a user from visiting a bad domain or URL before they get there," he says.
Mobile apps are demanding in the number of permissions they seek, but security experts note there is often no need to give an app carte blanche on the permissions.
"Only enable those permissions you know are required," Forkish says. "Many apps want permission to your contacts and calendar, but if they don't relate to the way you plan to use your app then don't enable it."
By limiting the level of permissions, it helps to reduce the potential attack area for malware writers and botnet operators.
Mobile phones are becoming the de-facto babysitter for some kids, replacing the television. But Hamilton advises employers to educate their workers on mobile security and teach them to refrain from giving their young children their smartphone to play with.
"You give your mobile device to your 6-year-old and suddenly all these games appear on your phone from third-party app sites," he warns.
He also recommended companies give their employees anti-phishing training, because social engineering is often used to get malware onto users' smartphones, which in turn can transform the devices into bots.
The WireX Android botnet last month snagged tens of thousands of mobile users, in order to wage DDoS attacks against organizations in multiple industries.
While it's clearly taxing to be on the receiving side of a DDoS attack, enterprises that find their mobile devices commandeered as bots also have reason for concern.
"Enterprises may notice their upstream traffic flow will be slightly constrained, but the impact will be negligible," says Robbie Forkish, Appthority CTO. However, Forkish and other security experts note it's still worth a company's time and effort to prevent their mobile devices from becoming bots.
For example, companies may find their IP addresses blacklisted if their mobile devices are swept up into a botnet, notes Andrew Blaich, a security researcher at Lookout.
James Plouffe, lead solutions architect with MobileIron, agrees.
"If you are an enterprise and part of a botnet, then you're consuming bandwidth for things not related to your company," Plouffe says. "Also, it could appear your company is the source of the attack and it could be bad for your company's reputation and you may incur some liability."
In addition to these issues, a company may find that once its mobile workforce is infected with malware, the attackers could turn the bots into another malicious purpose.
"The attacker could change the instructions and have it infiltrate confidential information on the device," says Robert Hamilton, director of product marketing at Imperva.
Here are 10 steps IT security teams can take to reduce the odds their mobile devices will get recruited as bots:
About the Author(s)
You May Also Like
CISO Perspectives: How to make AI an Accelerator, Not a Blocker
August 20, 2024Securing Your Cloud Assets
August 27, 2024




