Slide Show: Security Gets Graphic
Notice that security companies have started producing a lot of infographics? We sure have. Here's a selection

Already have an account?
Security companies used to have the worst presentation graphics. Engineers creating PowerPoint presentation using clip art never made for captivating artwork.
Times have changed. Now firms have found that publishers and bloggers want art and have started producing slick graphics to accompany data-heavy news or, in some cases, advice posters. The industry ramped up their production of graphics just before this year's RSA Security Conference.
Here's a sampling of the beautified world of security:
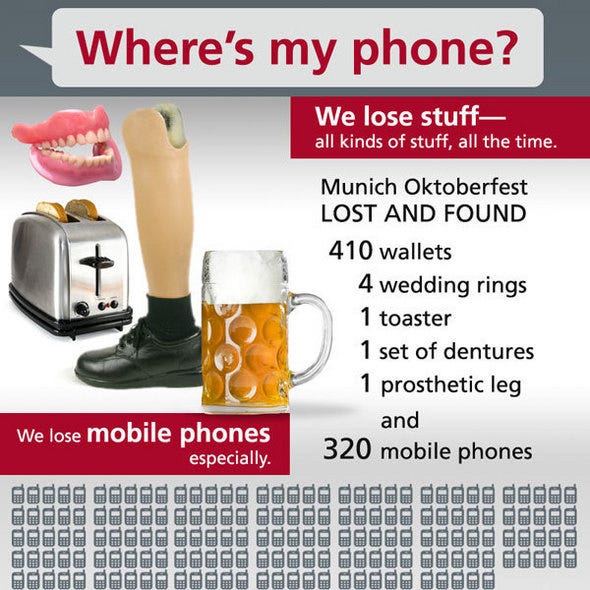
Kicking off the deluge of data-oriented graphics, McAfee released a somewhat crowded chart compiling various statistics regarding lost phones. At Oktoberfest in Munich in 2010, for example, mobile phones were the second most-lost item, right behind wallets.
The artwork shows the security industry on the cusp of moving from the clip art graphics of the past.
About the Author
You May Also Like




