What the Conti Ransomware Group Data Leak Tells Us
Knowing the inner workings of Conti will not only help ransomware negotiators but also help organizations to better handle a ransomware attack when it happens.
As tensions continue to rise regarding Russia's invasion of Ukraine, the Conti ransomware group — a Russia-based organization responsible for high-profile attacks on large enterprises as well as critical infrastructure networks — initially announced its support of Putin's invasion on the group's data leak site before issuing a retraction, claiming it condemns "the ongoing war." Conti noted in a follow-up statement on March 1 that "retaliatory measures" would be taken if the West launched cyberattacks against Russia or Russian-speaking countries.
However, on Feb. 27, a Ukrainian security researcher leaked almost two years' worth of internal chat logs from the group, which contain approximately 400 files, including thousands of internal chat logs.
At GroupSense, we maintain a thorough library of intelligence on ransomware groups, including Conti, developed through our ongoing research and ransomware negotiations. Most notably, we knew that Conti operated like a traditional business as well as about its ties to Russia; however, the leaks revealed more details about the inner workings of Conti — its ransomware-as-a-service (RaaS) structure, the business challenges it faces, certain behaviors, and more. Here's some of the key data we learned so that you can better understand the group and protect your organization.
Operational and Pay Structure
Just like other as-a-service business structures, Conti's structure consists of upper and middle management with entry-level employees who do much of the legwork. Their roles include specialized functions such as ransomware negotiators and deal closers. The leaked chat logs also revealed there are dedicated negotiation trainers. The entry-level employees rely on initial access brokers — the individuals who gain access to company networks — that work on weekends to ensure the higher-ups of the group have enough work (negotiating and collecting ransoms from victims) to keep them busy that next week.
As part of the leak, cryptocurrency wallet keys were exposed, which provided key information on how much Conti's employees get paid. Initial access brokers get paid a large portion of the ransom collected, usually about 20% to 30%, given how critical they are to Conti's revenue stream and their weekend work. Upper management takes the highest percentage from the ransom, while middle managers — who work a normal 9-to-5 schedule — collect an average salary of $80,000 a year. New entry-level employees, the workhorses of the organization, make just half of a percent of the ransom until they are promoted, and then they receive 1% of the ransom.
False Claims and Business Challenges
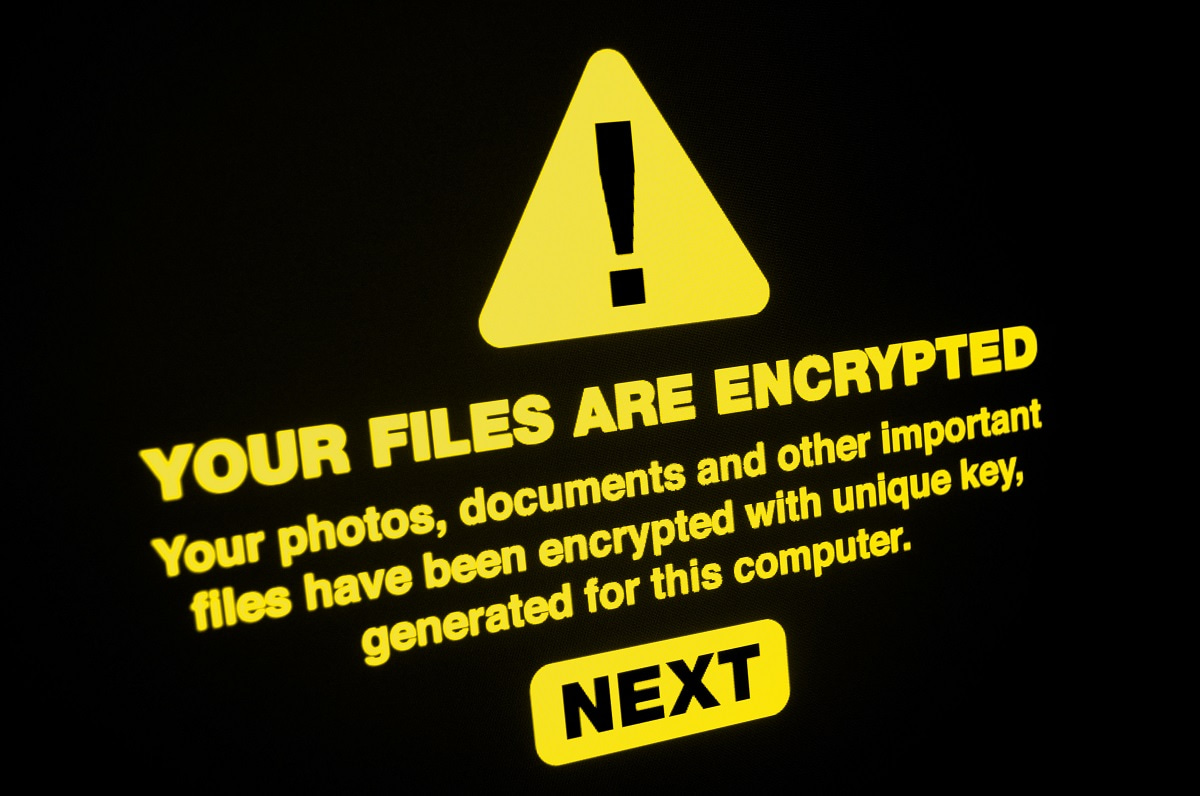
Conti's attacks typically begin with the initial access brokers launching phishing campaigns to gain access to a network, encrypting devices and data before dropping a ransom note on infected machines. However, the logs exposed that Conti employees often claim to have all their client's data — but it's not always true. In most cases, the group can gain access to only a fraction of the client's data that it claims to have even though it will tell victims that it has "all their data." This is especially important to note because with this information, your organization can better understand the extent of an attack, allowing negotiators and threat intelligence teams to be able to call Conti's bluffs.
In addition, over the past several months, Conti has had issues cashing out its cryptocurrency wallets. In the leaked chats, Conti operatives discussed the distance to different banks in kilometers so as not to reveal their exact locations. This means Conti operatives are forced to move from city to city to access different banks to make payouts possible. Conti operatives also discussed weekend trips in kilometers to protect the location of their offices.
Office Politics and Negotiation Behavior
The leaked chat logs also revealed Conti's office politics. The chat logs had several instances of entry-level employees complaining about how middle and upper management treats them and how many hours they work. There also appears to be a promotion structure involving more prestigious offices, the best and most sought-after location being in Dubai. If promoted to that location, employees get more high-profile cases, bigger payouts, and even bonuses.
For ransomware payout sums in the millions, we learned employees are told to "be nice" to their victims and put on their best customer service voices, per the chat logs. The organization doesn't care as much about optics for victims who aren't able to pay large ransoms. Also, we found that when the group's victim is a lawyer, Conti negotiators are told to never negotiate because lawyers will always pay the full price.
With this data leak comes a lot of valuable data to sift through, and these findings are the most significant of what we've found thus far. Knowing the inner workings of Conti will not only help ransomware negotiators but also help organizations to better handle a ransomware attack when and if it happens. The other good news is that in the long run, leaks like these can enable law enforcement groups to target specific threat actors to take down their organizations, making Conti especially vulnerable.
About the Author
You May Also Like




