Leveraging Behavioral Analysis to Catch Living-Off-the-Land Attacks
Attackers are increasingly staying under the radar by using your own tools against you. Only behavioral AI can catch these stealthy attacks.
March 16, 2023

The most advanced cyberattackers try to look like your administrators, abusing legitimate credentials, using legitimate system binaries or tools that are natively utilized in the victim's environment. These "living-off-the-land' (LotL) cyberattacks continue to cause headaches for security teams, which often have no effective means of differentiating between malicious behavior and legitimate administrative behavior.
When an attacker uses applications and services native to your environment, your own staff also use these systems, and a signature- or rules-based detection system will either miss the activity or end up alerting or disrupting your own employees' actions.
It is no surprise then that these attacks have been found to be highly effective, with the Ponemon Institute finding that fileless malware attacks are about 10 times more likely to succeed than file-based attacks.
LotL cyberattackers rely on a variety of tools and techniques, including:
Using PowerShell to launch malicious scripts, escalate privileges, install backdoors, create new tasks on remote machines, identify configuration settings, evade defences, exfiltrate data, access Active Directory information, and more
Using Windows Command Processor (CMD.exe), to run batch scripts, and (WScript.exe) and Console Based Script Host (CScript.exe) to execute Visual Basic scripts, offering them more automation.
.NET applications for resource installation via the .NET Framework. Installutil.exe allows attackers to execute untrusted code via the trusted program
Using the Registry Console Tool (reg.exe) to maintain persistence, store settings for malware, and store executables in subkeys.
And many others, including WMI (Windows Management Instrumentation), Service Control Manager Configuration Tool (sc.exe), Scheduled Tasks (AT.EXE Process), and Sysinternals such as PSExec.
LotL techniques involving Remote Desktop Protocol (RDP) connections can be some of the most difficult activities to triage for security teams, as RDP often represents a critical service for system administrators. For security teams, it can be exceptionally difficult to parse through and identify which RDP connections are legitimate and which are not, especially when administrative credentials are involved.
Defensive systems focused on "known bads" and historical attack data fail to catch the malicious use of some of the tools described above. Stopping these attacks requires a business-centric defensive strategy that uses AI to understand "normal" behavior of every user and device in your organization to detect anomalous activity in real time.
Take, for example, this real-world attack that targeted a Darktrace customer in July 2022.

Figure 1: A timeline of the attack. Source: Darktrace
The first sign of a compromise was observed when Darktrace's AI revealed an internal workstation and domain controller (DC) engaging in unusual scanning activity, before the DC made an outbound connection to a suspicious endpoint that was highly rare for the environment. The contents of this connection revealed that the threat actor was exporting passwords from a successful cracking attempt via Mimikatz — a presence that previously had been unknown to the security team.
Several devices then began initiating outbound connections to AnyDesk-related websites, a possible means of persistence or a backdoor for the attacker. In their first demonstration of LotL methods, the attacker initiated a "golden ticket attack" culminating in new admin logins. With their new position of privilege, use of the automating "ITaskSchedulerService" and Hydra brute-force tool the next day allowed for even deeper insights and enumeration of the customer's environment.
One device even remotely induced a living-off-the-land binary (LOLBin) attack. By creating and running a new service on three different destinations, the attacker retrieved MiniDump memory contents and feed any information of interest back through Mimikatz. Not only can this strategy be used to identify further passwords, but it allows for lateral movement via code executions and new file operations such as downloading or moving.
On the final day, a new DC was seen engaging in an uncommonly high volume of outbound calls to the DCE-RPC operations "samr" and "srvsvc" (both of which are legitimate WMI services). Later, the DC responsible for the initial compromise began engaging in outbound SSH connections to a rare endpoint and uploading significant volumes of data over multiple connections.
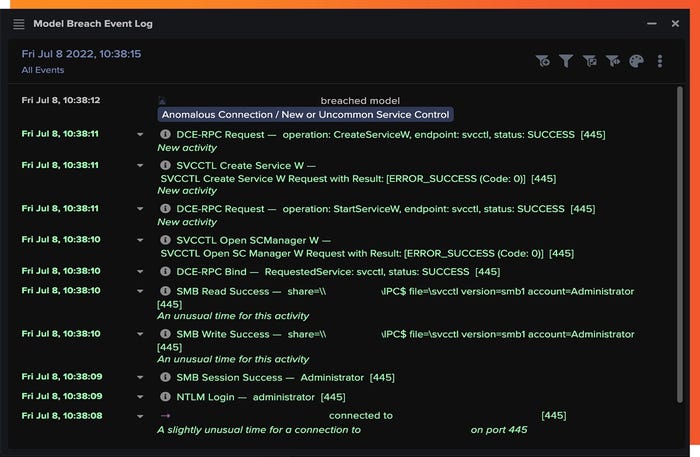
Figure 2: Darktrace's Device Event Log reveals some of the LotL techniques used by the attacker
The attacker's use of legitimate and widely used tools throughout this attack meant the attack flew under the radar of the rest of the security teams' stack, but Darktrace's AI stitched together multiple anomalies indicative of an attack and revealed the full scope of the incident to the security team, with every stage of the attack outlined.
This technology can go further than just threat detection. Its understanding of what's "normal" for the business allows it to initiate a targeted response, containing only the malicious activity. In this case, this autonomous response functionality was not configured, but the customer turned it on soon after. Even so, the security team was able to use the information gathered by Darktrace to contain the attack and prevent any further data exfiltration or mission success.
LotL attacks are proving successful for attackers and are unlikely to go away as a result. For this reason, security teams are increasingly moving away from "legacy" defenses and toward AI that understands "'normal" for everyone and everything in the business to shine a light on the subtle anomalies that comprise a cyberattack — even if that attack relies primarily on legitimate tools.
About the Author

Tony Jarvis is Director of Enterprise Security, Asia-Pacific and Japan, at Darktrace. Tony is a seasoned cybersecurity strategist who has advised Fortune 500 companies around the world on best practice for managing cyber-risk. He has counseled governments, major banks, and multinational companies, and his comments on cybersecurity and the rising threat to critical national infrastructure have been reported in local and international media including CNBC, Channel News Asia, and The Straits Times. Tony holds a BA in Information Systems from the University of Melbourne.
You May Also Like
Cybersecurity Day: How to Automate Security Analytics with AI and ML
Dec 17, 2024The Dirt on ROT Data
Dec 18, 2024


