Ex-Uber CISO Advocates 'Personal Incident Response Plan' for Security Execs
Why Joe Sullivan feels paying off attackers was a way of solving the problem.
December 12, 2023

BLACK HAT EUROPE 2023 – London – Former Uber CISO Joe Sullivan last week shared new details about the 2016 data breach at the company that led to his firing from Uber and, later, felony charges.
In a keynote address at Black Hat Europe, Joe Sullivan admitted he avoids listening to webinars and programs that lead with the theme of "how to avoid turning out like Joe." In an interview with Dark Reading, Sullivan said he had to "listen to and see my name in the media saying things about me that I knew weren't true."
The Uber Breach
Sullivan was in his second year as CISO of Uber when attackers stole 57 million user and driver accounts, including names, phone numbers, email addresses, and more than 600,000 US drivers' license numbers.
After the attackers alerted Uber about the breach and before Uber notified the authorities, the attackers were paid a $100,000 settlement — which Sullivan characterized as a bug bounty, where the attackers signed a nondisclosure agreement (NDA) about the incident. Uber CEO Dara Khosrowshahi later fired Sullivan, arguing that Sullivan had misled him about the breach, calling Sullivan's decision not to disclose "the wrong decision." At the time, Uber had ordered Sullivan either to resign or be fired from his role.
In 2020, when Sullivan was CISO at Cloudflare, he first learned of his pending arrest in the case when his daughter called him, asking, "Are you in jail right now?" after one of her friends heard a news report that Sullivan had been arrested.
Sullivan was charged with two counts: obstruction of justice specifically related to a Federal Trade Commission (FTC) investigation of Uber, and misprision of a felony, where he was accused of covering up a felony. The FTC's statement said that Sullivan allegedly "executed a scheme to prevent any knowledge of the breach from reaching the FTC."
That statement said contracts drafted by Sullivan and a lawyer assigned to his team falsely represented that the hackers did not take or store any data in their hack, and that Sullivan continued to work with the Uber lawyers handling or overseeing the FTC investigation, including the General Counsel of Uber. But the FTC says it was not notified about the breach or payment until 2017.
On the misprision of a felony charge, Sullivan said that the attackers violated 18 USD 1030, related to accessing a computer without permission. However, he argued, there is typically a contractual relationship between a vulnerability researcher and the company whose network they test — usually executed via third-party companies like HackerOne and Bugcrowd.
He noted that these relationships were not common in 2016, so anyone who conducted hacking research into an organization's systems was committing a felony. Sullivan is appealing: His attorneys argue that upholding the second charge could criminalize the use of bug bounty programs and create a "precedent that threatens to take away a valuable tool."
Responsible Disclosure
Sullivan said he had always promoted responsible disclosure policies — going back to his role with eBay in the 2000s, when he encouraged testers to reveal details of vulnerabilities they found. "You want all of the information you can get, and you realize if you have to pay to get results; [the results are] better than [from] all of the pen-testing companies," he told attendees at Black Hat Europe.
But that $100,000 payment and NDA haunted Sullivan and Uber: In the federal trial in May of this year, Sullivan was accused of using the NDA as a cover-up. He said in his keynote here that he believed the NDA was a way of solving the problem and of resolving the breach.
Sullivan's lawyers made the case that Sullivan issued the payment to the hackers with the full knowledge and blessing of Travis Kalanick, Uber's CEO at the time of the breach, as well as that of members of the Uber legal team.
The judge asked the prosecutor why the CEO of Uber had not been held accountable as well, saying that the CEO was just as culpable as Sullivan yet was not in court, and that Sullivan alone was being held responsible.
Offering Advice
Sullivan's experience with the Uber breach and its legal fallout has led some security professionals to consult with Sullivan for career advice. He now often gets approached by security professionals who are interviewing for their first CISO appointment. He said where they once asked for his advice on "What do I say to get the job?" but now, due to his legal case and the SEC filing charges against the SolarWinds CISO, he gets questions like "Why would I take on all of that personal risk?" and "Is the CISO role worth the stress?"
Sullivan told Dark Reading that those security executives have been seeking his advice "since that first headline in 2017; I get contacted on a weekly basis by people in the role who are worried about an incident going down at their place, or those who are thinking ahead."
He advises security professionals to be sure they have the right personal protections in place so they are prepared for the potential fallout of a data breach.
In one recent conversation, he recommended that the security professional accept a CISO job offer but to first talk with the general counsel and the CEO of the company to make sure they understand the nuances of attacks, vulnerability, and breach disclosure.
He also recommended creating a personal incident response plan and to consider how you would survive a breach personally. Look at your own legal representation, insurance, and plans for your family, he said.
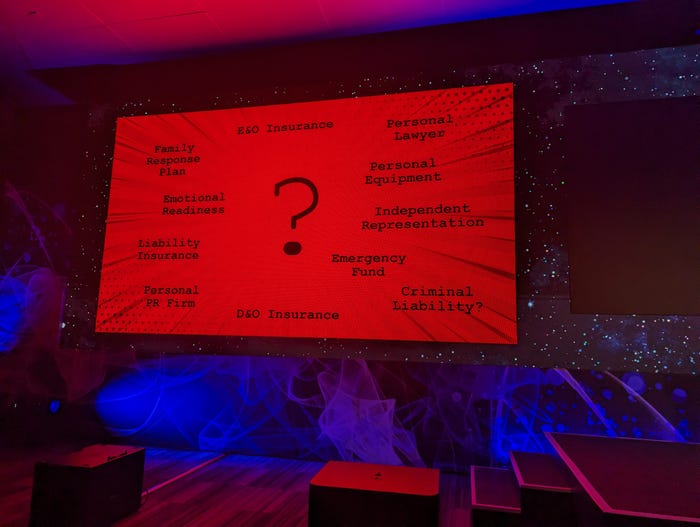
Slide showing advice on a personal incident response plan
As a strategy for preparing and surviving a breach, Sullivan used the analogy of a fire department. "While [one] team is putting out a major fire, at the fire station you'll see another team asleep [and] you'll see another team polishing the engine."
Fire departments plan ahead and have reinforcements, he pointed out, "and I think we have to do a better job building our own fire departments on our teams, and we have to get better at communicating internally. We have got to make more friends."
Read more about:
Black Hat NewsAbout the Author
You May Also Like




