Attackers Sell Growing Number of Legitimate SSL Certificates
Network security applications performing deep packet inspections are increasingly getting duped by these rogue legitimate certificates, according to a new report.

Sales of legitimate SSL certificates are on the rise on the Dark Web, as attackers find an effective means to trick network security applications into allowing their malicious payloads to come through, according to a recent report.
A sharp spike in code signing certificates used as a layered obfuscation technique to distribute malicious payloads began making the rounds across the globe last year, security researchers at Recorded Future note in a report issued February 22.
Attackers are stealing data from companies and submitting it to certificate authorities like Comodo, Thawte and Symantec and receiving legitimate SSL certificates for those particular companies, the report notes.
"The certificates are created for a specific buyer per request only and are registered using stolen corporate identities, making traditional network security appliances less effective," states Andrei Barysevich, director of advanced collection at Recorded Future, in the report.
He added that the legitimate business owners are often unaware their data was stolen and used for nefarious purposes.
History and demand for legit SSL certificates
Use of legitimate SSL certificates are believed to have first appeared in 2011, when an attacker managed to pilfer 500 legitimate SSL certificates from certificate authority DigiNotar, according to the book Android Apps Securityby Sheran Gunasekera. The attacker used the rogue SSL certificates to carry out man-in-the-middle attacks and because DigiNotar had its root certificate in all modern browsers the attacker was able to validate them with ease.
According to Gunasekera's book, websites that accepted the rogue SSL certificates included *.google.com, *.android.com, *microsoft.com, and others. Eventually, web developers began to blacklist DigiNotar's certificate and the company later filed for bankruptcy, the book notes.
Four groups of malicious attackers are well known in this area of code signing certificates and have been active since 2011, Barysevich notes in his report. But it wasn't until 2015 that these legitimate SSL certificates were first offered for sale on the Dark Web, he adds. In 2017, demand for legitimate SSL certificates jumped higher, he notes.
Product listing advertised by a threat actor
\r\n(Source: Recorded Future)\r\n
C@T, one of the first attackers to offer rogue SSL certificates, claimed in advertisements on the Dark Web that payload installations using these SSL certificates would increase the buyer's success rate by 30% to 50%, Barysevich notes in his report.
However, despite such claims, some threat actors note that success rates are lower with Google's Chrome browser because of some advanced security metrics it uses, whereas Internet Explorer, Firefox and Safari browsers may have higher success rates, Barysevich states in the report.
Future use of rogue legitimate SSL certificates
Despite attackers increasingly purchasing rogue legitimate SSL certificates, this practice is not expected to become a common aspect of cybercrime.
"Unlike ordinary crypting services readily available at $10 to $30 per each encryption, we do not anticipate counterfeit certificates to become a mainstream staple of cybercrime due to its prohibitive cost," Barysevich states.
However, nation-state actors and more sophisticated cybercriminals who are interested in highly targeted attacks are more apt to use the rogue SSL certificates in their attacks, he adds.
And just how expensive are fake SSL certificates?
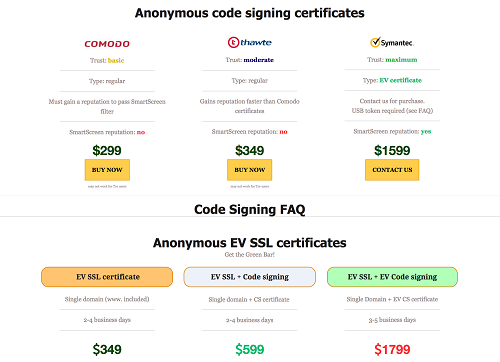
The most affordable version of these rogue SSL certificates costs $299. Meanwhile, the starting price for a domain name registration with an EV SSL certificate costs $349, and a comprehensive Extended Validation (EV) certificate with a rating for a SmartScreen reputation goes for $1,599.
Related posts:
— Dawn Kawamoto is an award-winning technology and business journalist, whose work has appeared in CNET's News.com, Dark Reading, TheStreet.com, AOL's DailyFinance, and The Motley Fool.
Read more about:
Security NowAbout the Author
You May Also Like




