
Breaking cybersecurity news, news analysis, commentary, and other content from around the world, with an initial focus on the Middle East & Africa and the Asia Pacific
Middle East Leads in Deployment of DMARC Email Security
Yet challenges remain as many nation's policies for the email authentication protocol remain lax and could run afoul of Google's and Yahoo's restrictions.
March 4, 2024

Following stricter email handling mandates by Google and Yahoo, organizations worldwide have quickly adopted a trio of email authentication technologies, and organizations in the Middle East are adopting them as quickly — or in some cases faster than — the global average.
Compared to about three-quarters (73%) of global organizations, about 90% of organizations in the Kingdom of Saudi Arabia and 80% in United Arab Emirates have implemented the most basic version of Domain-based Message Authentication Reporting and Conformance (DMARC), which — along with two other specifications, the Sender Policy Framework (SPF) and Domain Key Identified Mail (DKIM) protocols — makes email-based impersonation much more difficult for attackers.
On February 1, both Google and Yahoo started mandating that all email sent to their users have verifiable SPF and DKIM records, while bulk senders — companies sending out more than 5,000 emails per day — must also have a valid DMARC record.
The new rules implemented by Google and Yahoo have had a dramatic impact on adoption worldwide, says Matt Cooke, cybersecurity strategist at Proofpoint.
"After the deadline, organizations across the globe can no longer assume with confidence that their emails will arrive in an inbox if their business is not taking their email authentication seriously," he says. "Up until this point, very few businesses demanded the people and businesses they communicate with authenticated their emails. Now, it will — and must — become an acceptable practice."
While the requirements of the large email providers have lent significant momentum to the adoption of DMARC and its associated authentication mechanisms, government regulations have also prompted companies to push for adoption. The countries of the Gulf Cooperation Council (GCC) — including Bahrain, Kuwait, Oman, Qatar, Saudi Arabia, and the United Arab Emirates — have created a variety of industry and national regulations, such as the Saudi Arabia Monetary Authority (SAMA) cybersecurity framework, that are prompting organizations to adopt stricter email controls, Cooke says.
Google, Yahoo Mandates
While the vast majority of regulations implemented by nations in the Middle East do not specify that organizations must adopt DMARC, some European governments are mandating the email authentication protocol, as well as the Payment Card Industry Association's PCI DSS 4.0 for any entity that processes credit cards.
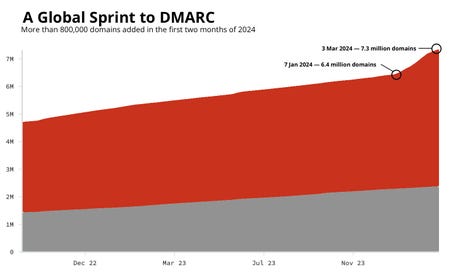
In the first two months of 2024, more than 12% of domains had a DMARC recorded added. Source: Red Sift
Overall, Middle Eastern nations are ahead in adoption of DMARC. About 80% of the members of the S&P's Pan Arab Composite Index have a strict DMARC policy, which is higher than the FTSE100's 72%, and higher still than the 61% of France’s CAC40 index, according to Nadim Lahoud, vice president of strategy and operations for Red Sift, a threat intelligence firm.
There is "a strong maturity that is beginning to trickle down the supply chain of the region," says Red Sift's Lahoud. "Widespread adoption promises a transformed landscape: drastically lowering the success rate of phishing scams, enhancing email reliability, and bolstering overall digital security."
Like most parts of the world, strict enforcement of DMARC — setting the domain record to reject nonconforming email — is lagging. Only 43% of domains in the UAE are set to reject suspicious emails, while 57% of those domains in Saudi Arabia have the most strict setting. However, both countries are ahead of the third of the Global 2000 companies (31%) that have set DMARC to strictly reject emails, according to Proofpoint's data.
The mandates by Google and Yahoo for email senders to use email authentication technologies has led to accelerated adoption of DMARC. More than 2 million new DMARC records were created in the first six weeks of 2024, including a 41% increase in records in the African market and a 29% increase in the Middle East, says Seth Blank, chief technology officer of Valimail, an email authentication platform.
"Implementation across organizations can be cumbersome and time consuming, especially given the new requirements from Google and Yahoo," he says. "It's critical to ascertain your security posture and understand your gaps now, so that you don't get caught with undeliverable mail, or worse, abuse of your company's email to defraud users."
Start Small With DMARC
Security teams and email administrators that have not yet implemented SPF, DKIM, and DMARC should use the Google mandate as impetus to get the project off the ground, says Proofpoint's Cooke.
"If you communicate with customers via Gmail and Yahoo and have not yet implemented email authentication protocols such as SPF, DKIM, and DMARC, the biggest challenge you face is time," he says. "Rollout takes multiple steps for each protocol and can be tricky, especially if you have several domains. Once you have the protocols in place, you face additional challenges, as you must maintain your DMARC, SPF, and DKIM records over time."
In South Africa, for example, 94% of banks and insurance companies have deployed Sender Policy Framework (SPF), one of the foundational protocols on which DMARC relies, while a smaller share of organizations — 78% of banks and 51% of insurance companies — had implemented DMARC.
Because email is used in almost all phishing attacks, and about 90% of successful cyberattacks start with a phishing email, updated email authentication regulations are essential for every company, especially in the Middle East, says Gerasim Hovhannisyan, CEO and co-founder of EasyDMARC, a provider of email authentication services.
"As political tensions escalate both within the Middle East and globally, the likelihood of cyberattacks targeting critical infrastructure significantly increases, underscoring the imperative for enhanced cybersecurity protocols," he says. "Given the prevalent use of email as a conduit for such attacks, the implementation of robust email authentication measures emerges as a crucial strategy to safeguard businesses and nation-states in the foreseeable future."
Read more about:
DR Global Middle East & AfricaAbout the Author
You May Also Like




