Cobalt Group Returns With Downloader Malware
Proofpoint found new campaigns by the notorious cybercrime gang using its CobInt modular downloader.

The Cobalt Group, which has made a name for itself over the past couple of years for stealing millions of dollars from banks and ATMs across Europe and Russia, is using a modular downloader in its latest campaign, according to researchers at security vendor Proofpoint.
The cybercriminal gang, which came onto the scene in 2016 primarily targeting financial institutions, is using malware that was dubbed "CobInt" by Group-IB when the Russian threat intelligence firm first detected the modular downloader. According to a blog post this week by the Proofpoint researchers, the Cobalt Group apparently stopped using CobInt as a first-stage downloader around the time Group-IB published its findings. However, it now seems the cybercrime group is back using CobInt, starting in July. Cobalt also was dealt a setback in March when the group's suspected leader was arrested.
Analysts at NetScout's Arbor Networks unit wrote about the return of CobInt last month, and now Proofpoint researchers note that they have found evidence of the Cobalt Gang's renewed effort with CobInt.
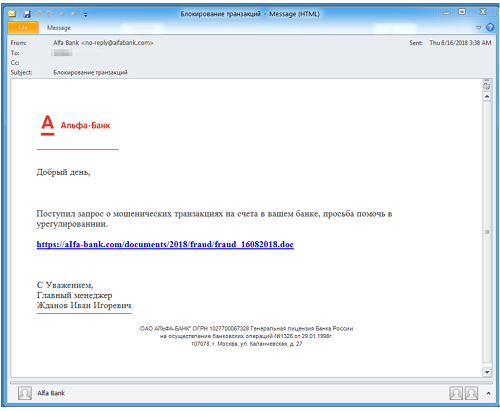
Email campaign designed to deliver CobInt malware
\r\n(Source: Proofpoint)\r\n
"Threat actors that are trying to avoid attention will often pause their activities when they feel too many eyes on them," Bryan Burns, vice president of threat research and engineering at Proofpoint, told Security Now in an email. "Sometimes that means changing tools and payloads, or it may mean going dark entirely for a while. Sophisticated malware is a sizeable investment, however, so we often see it returning at a later date once the pressure is off."
CobInt is the latest modular downloader campaign Proofpoint has seen in recent weeks.
Earlier in the summer, researchers discovered Marap -- which targeted financial institutions -- and AdvisorsBot, which focused more on hotels, restaurants and telecommunications companies. Both downloader campaigns came with relatively small footprints, were designed to evade detection by cybersecurity solutions and were focused on reconnaissance of the infected systems, according to Proofpoint researchers. CobInt shares similar qualities. (See AZORult Downloader Adds Cryptomining, Ransomware Capabilities.)
Modular downloaders are designed to enable attackers to modify and update the software after it has been installed onto a victim's system.
"Modular downloaders give the threat actors more flexibility, subtlety, and control," Burns wrote. "By collecting data on the infected system, they can tailor the next payload to the victim to maximize returns or skip further infections entirely if the system doesn't match what they're after. Because these downloaders are relatively simple compared to a full Trojan or other final payload, they are easier to mutate and obfuscate to avoid detection."
Proofpoint researchers in August and September detected email campaigns designed to deliver the CobInt malware. The first, seen on August 2 and also detected by Arbor Networks, involved messages written in Russian with subject lines reading "Suspicion of fraud." The messages contained two URLs, with the first linked to a macro document that installed the downloader. The second URL linked directly to the CobInt Stage 1 executable.
The second round of messages were seen August 14 and spoofed the Single Euro Payments Area (SEPA) with sender domains that look legitimate. The subject lines used such words as "notification," "letter," "message" and "notice." These messages contained a Word document that was a ThreatKit exploit document that would execute the embedded CobInt Stage 1 payload. Some of the messages contained URLs linking directly to the CobInt downloader, the analysts said.
The CobInt downloader malware is written in C and can be seen in three stages. The first is an initial stage, which according to Proofpoint researchers, "is a basic downloader with the purpose of downloading the main CobInt component. As with other downloaders we have examined recently, its functionality is disguised by the use of Windows API function hashing. The command and control (C&C) host and URI are stored as encrypted strings."
The second stage is the main component, in which various modules from the C&C server are downloaded. The third stage follows with downloading and executing additional modules.
In their blog post, Proofpoint researchers note that CobInt shows that threat actors like the Cobalt Group and others "are increasingly looking to stealthy downloaders to initially infect systems and then only install additional malware on systems of interest."
Burn told Security Now that it also "tells us that collectively we are getting better at detecting and defending against these types of attacks. This is ultimately an arms race, and the attackers are evolving their tools to try to stay ahead of modern defenses. Also, with the spate of recent arrests and indictments against cyber-threat actors, there must be increased pressure to try to fly beneath the radar of the global intelligence community."
Related posts:
— Jeffrey Burt is a long-time tech journalist whose work has appeared in such publications as eWEEK, The Next Platform and Channelnomics.
Read more about:
Security NowAbout the Author
You May Also Like




