Americans feel like they've lost control over their online lives, but they still aren't always practicing proper security.
A new survey by the Pew Research Center on how Americans view cybersecurity finds that most people are concerned about online security but forgo the necessary steps to protect themselves.
The survey of 1,040 US adults shows that 41% of them have shared the password to one of their online accounts with friends or family members. Young adults are especially likely to engage in this behavior – 56% of online adults ages 18- to 29 have shared passwords.
Along with sharing passwords, 39% say they use the same password or very similar passwords for many of their online accounts. And 25% often use passwords that are less secure than they’d like because simpler passwords are easier to remember than more complex passwords.
"When it comes to passwords, very few of us are acing the test," says Aaron Smith, a co-author of the report, and associate director, research, at Pew. "And no age group is doing particularly well."
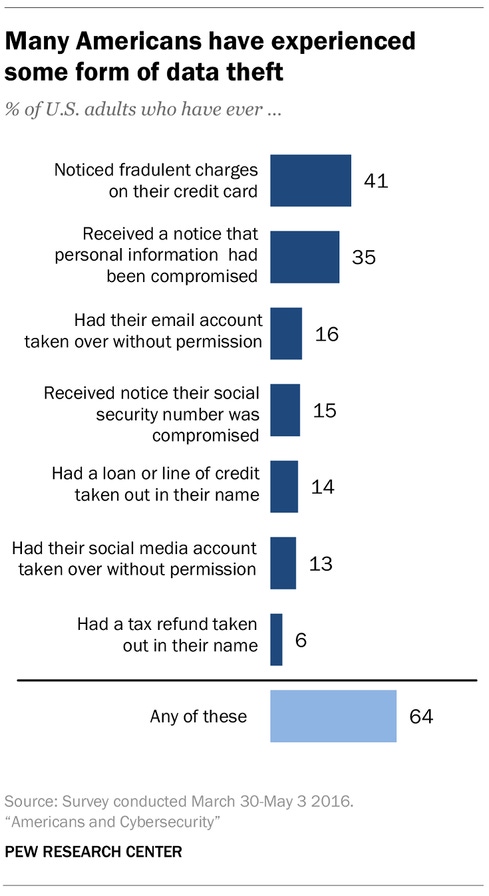
Smith says the study also found that people feel that they have lost control over their personal information. For example, the study found that 64% have directly experienced some type of significant data theft or fraud and 49% think their personal data has become less secure in recent years.
Americans have also lost confidence in major institutions to protect their data, mostly notably the federal government (28%) and social media sites (24%). In contrast, 42% of respondents say they are "somewhat confident" and another 27% say they are "very confident" that their credit card companies can be trusted to protect their data.
"In some ways it’s not a fair comparison because social media sites especially don’t have a full customer service staff and 1-800 numbers to call," says Eddie Schwartz, board director at ISACA. "Social media sites like Facebook are free and you get what you pay for."
Schwartz adds that for the most part the Pew data meshes with a recent ISACA/RSA study from last year where 74% of respondents said they expected to fall prey to a cyberattack in the next year, and 60% hsf experienced a phishing attack.
"So yes, we know these cyberattacks are happening, we know they are bad, we’re afraid, but not always willing to do something about it," Schwartz says.

On a more positive note, the Pew study found that 52% of those surveyed use two-factor authentication on at least some of their online accounts. And 57% say they vary their passwords across their online accounts.
Here’s a sampling of some of the other findings of the report:
Roughly 10% of those surveyed say they never update the apps on their smartphone, and only 32% do so automatically. Another 14% say they never update the operating system.
51% surveyed say a major attack on our nation’s public infrastructure will "probably" happen in the next five years, while 18% say it will "definitely" happen.
75% of American have heard at least something about the Target breach, and 47% has heard "a lot" about it. Only 33% of those surveyed are aware of the OPM attack with only 12% hearing "a lot" about it.
Americans are divided over encryption. 46% believe that the government should be able to access encrypted communications to investigate crimes, while 44% says that technology companies should be able to use encryption tools that are unbreakable to law enforcement. Democrats and younger adults tend to support strong encryption, while Republicans side with law enforcement.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




