Millennials Could Learn From Baby Boomers When It Comes To Security
New reports show baby boomers have their millennial children beat when it comes to information security.
Millennials may be tech-savvy, but they have a lot to learn when it comes to security, several new studies reveal.
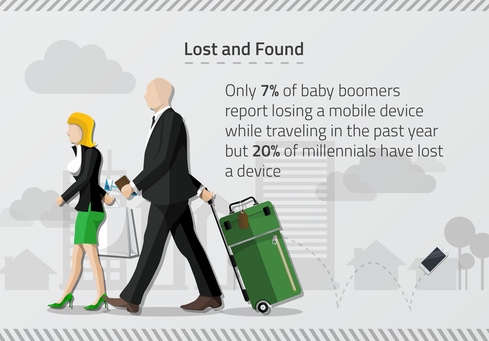
According to a survey commissioned by Webroot, 59% of millennials share their travel plans on social media sites whereas 71% of baby boomers do not. A Wakefield Research survey on behalf of SecureAuth found that 78% of millennials have disclosed personal information online over public WiFi, versus only 38% of respondents aged 55-64, and 33% aged 65 and over.
Not only are millennials taking risks when it comes to what they share and where they browse, but they’re also not great at creating strong passwords. A survey conducted by OnePoll and commissioned by Gigya found that only 33% of millennials versus 53% of baby boomers create secure passwords for all of their accounts. (That means passwords stronger than “1234” or a birthday or some other personally identifiable piece of information).
And it may come as no surprise that of the 26% respondents in the Gigya survey that have experienced a data breach, millennials were at number one (35%). Baby boomers made up 18% of those breached.
But while baby boomers tend to have more secure habits than millennials, Milbourne says that baby boomers are still slightly more at risk because they’re more likely to fall for Internet-based scams. “Millennials are more savvy at detecting malicious activity on the Web,” he says.
Two of the surveys blame the millennial mentality of “always be connected” for their nonchalant security practices. “Millennials have grown up so connected to so many social media sites that it doesn’t occur to them that there is danger there that they’re giving out info, and their preference for being connected is more important to them than their potential for risk,” says Craig Lund, CEO of SecureAuth.
"If people really realized how much information is out there ... and tied back to social security numbers and driver’s license numbers, passport; couple that with credit history and where you went to school -- those things collectively make up your digital identity,” Lund says.
Millennials need to understand that if that information is compromised, it can affect you in the long-run, ruining your credit and hurting your chances of renting an apartment or buying a car.
Lund admits that completely avoiding connecting to public WiFi isn’t realistic nor the solution to helping millennials practice good information security.
“I admit, I’ve given up my address [on public WiFi]; it’s just an ecommerce world we live in,” he says. Education is the key to helping millennials understand the risks when they don’t practice good security, and knowing what type of data should never be disclosed -- social security number, passport, driver’s license -- over public WiFi. And suffering from a breach, though not ideal, can certainly help change behavior quickly. “Sometimes negative experience can be a great teacher,” he says.
Grayson Milbourne, security intelligence director for Webroot, advises people to invest in a mobile antivirus app because it’s lightweight and not the battery drain that is perceived. He also warns against traveling without a connectivity plan.
“What we see is when people travel, they might not be prepared for Internet usage so they’ll seek out a hot-spot to connect. We strongly discourage this type of behavior because there’s no way to know it isn’t being sniffed by someone else,” he says.
Milbourne suggests planning ahead, especially as summer plans start to form: call service providers to enable roaming, and invest in some cheap, disposable SIM cards to protect data.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




