How & Why the Cybersecurity Landscape Is Changing
A comprehensive new report from Cisco should "scare the pants off" enterprise security leaders.
Cisco recently published its 2018 annual cybersecurity report. The study is far more comprehensive than previous surveys and includes threat research from its Talos group and a number of technology partners, along with a survey of 3,600 chief security officers and security operations managers from all over the world. Even more important: the report underscores the need to change the way cybersecurity is done. It should scare the pants off today's security leaders.
Highlights of the study include four key assertions:
1. Malware is becoming self-propagating.
Historically, malware required a user to click on a link, open an attachment, or take some other kind of action before it could spread. Today, newer forms of malware, like ransomware cryptoworms, are network-based, which obviates the need for humans to spread it. Self-propagating malware is much more difficult to find and can propagate at network speeds. Cisco warns that self-propagating malware has the potential to take down the Internet.
2. Ransomware isn't only for ransom.
In security circles, 2017 may well be remembered as the year of ransomware. It made headlines as it wreaked havoc on companies large and small. One healthcare security professional I talked to admitted his company had been breached several times and now just pays the ransom as a "cost of doing business." Ransomware even hit pop culture as shown by a recent episode of one of my favorite TV shows, Homeland, when the ex-CIA agent and heroine Carrie Mathison got stung by it. The Cisco security report indicates that some hackers aren't just looking to make a few bucks from the ransom threat. Rather, their main goal is the destruction of systems and data. The recent Nyetya (NotPetya) threat posed as tax software but was actually something called "wiper malware" that killed organizations' supply chain systems.
3. Adversaries are stepping up their evasion capabilities.
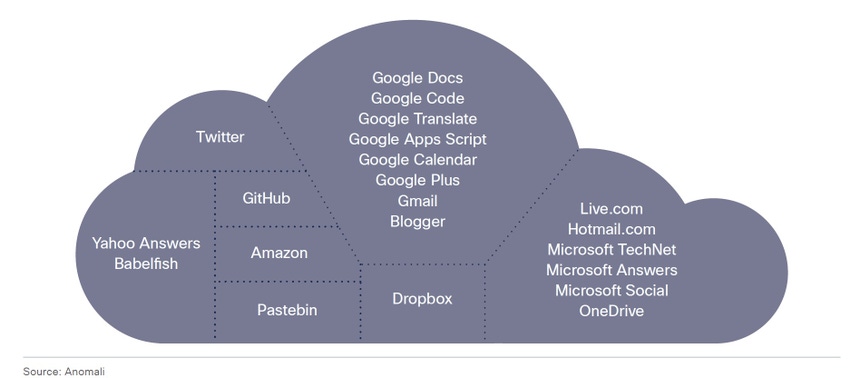
The ability to skirt sandboxes has been something that the bad guys have been getting steadily better at executing. In no way am I saying sandboxes don't work. They do, but some malware has gotten smart enough to evade detection. A growing technique is to hide the threat in encrypted traffic. The use of encryption has grown as a way of protecting payloads but it can also conceal bad traffic from security systems. Threat actors are also using popular cloud services for command and control, making malware very difficult to find with traditional security tools because it looks like normal traffic. The graphic below, from Anomali, offers some examples of cloud services that were abused by malware for command and control.
4. The Internet of Things (IoT) is becoming a significant threat vector.
Businesses of all sizes are deploying IoT devices at a furious rate. This may be a critical component of digital transformation, but it also poses a number of new security problems, according to the study, because of the following:
60% of IoT devices are deployed by operational technology not IT.
Many IoT devices are unmonitored.
IoT devices created "back doors" to other systems.
Patching for IoT devices is often done poorly.
IoT endpoints often have no inherent security capabilities.
Any one of these points can be problematic, but put them together and it spells disaster for many companies. Mirai and Reaper may have been the first couple of highly publicized IoT botnets, but they certainly won't be the last.
The lesson of the report is that the bad guys are getting smarter, are creating more damage, and have more tools at their disposal. But the big issue for security professionals is what to do about it. Clearly, doing what you did before isn't going to protect your business. If the hackers and threats keep evolving, so must an organization's security strategies. Here are four "no-brainer" recommendations.
Recommendation 1: Implement segmentation. One of the facts of life in security is that businesses will get breached. The challenge is to minimize the blast radius when this happens. Segmentation ensures that when a breach occurs, damage is limited to a small, confined area.
Recommendation 2: Use machine learning-based tools. Machine learning can connect dots faster than people can. That's why the bad guys are using it. Signature-based anti-malware was once state-of-the-art, but the industry changes too fast. Instead, shift to machine learning-based tools that can sift through the massive amounts of data and find those small anomalies before they become big security problems.
Recommendation 3: Automate the onboarding and security of IoT devices. This requires coordination of IT, security operations, and operational technology. There are a number of access control solutions that enable the entire IoT onboarding process to be automated so the devices can reach only the other devices they need to and, if a breach occurs, it won't impact other critical systems.
Recommendation 4: Extend security to the cloud. The concept that security teams are only responsible for traffic and data on the company network is a complete fallacy today. Security tools must extend to public cloud services. The first step in this is to implement a process of doing periodic audits to ensure that all the cloud services that are being used are actually known.
Related Content:

Black Hat Asia returns to Singapore with hands-on technical Trainings, cutting-edge Briefings, Arsenal open-source tool demonstrations, top-tier solutions and service providers in the Business Hall. Click for information on the conference and to register.
About the Author(s)
You May Also Like
Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




