Active Directory Is Dead: 3 Reasons
These days, Active Directory smells gangrenous to innovative companies born in the cloud and connecting customers, employees, and partners across devices at light speed.
Ninety-five percent of Fortune 500 companies use Active Directory, a 1990s technology, because their infrastructures are based on a 90s network architecture of on-premises PCs, applications, servers, and tools. But look around. Today’s hottest startups –- companies like Dropbox, Uber, Pinterest, and Tumblr -- just snort, and say, “The 90s called, and they want their infrastructure back.”
Full disclosure: I am the CEO and Founder of OneLogin, a cloud-based identity and access management company. Active Directory integration is one of our focus areas. And though I have other fond memories of the 90s -- Nirvana, X-Files, Hale-Bopp -- Active Directory isn’t one of them. These days, Active Directory smells gangrenous to innovative companies that were born in the cloud and operate at light speed interconnecting customers, employees, and partners across an array of devices and time zones.
Before laughing off the death of Active Directory, remember we also never imagined that Apple would one day have a bigger market capitalization than IBM, or Google would be nine times more valuable than General Motors. Today’s 30-person company is positioning itself to be tomorrow’s 1,500-person company.
Why am I predicting the death of Active Directory?
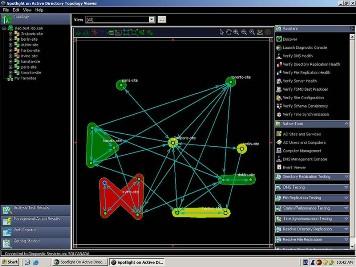
Fact 1: Active Directory’s complexity slows IT’s ability to respond to business needs. Originally crafted when IT owned and dictated everything, including the look, feel, and operation of user applications, Active Directory has failed to keep up. Have you tried to implement Single-Sign-On for your legacy, cloud, and mobile apps with Active Directory? If so, this custom integration likely took you months to complete, and probably lacked advanced functionality like multi-factor authentication and rapid deprovisioning (a must when employees or contractors leave an organization). Rinse and repeat the next time you need to add new apps. In an era where business runs on Red Bull, Active Directory is old and bloated.
Fact 2: Active Directory increases the daily IT workload. IT managers tell me they spend too much time integrating new apps into their aging Active Directory infrastructures. This is especially true because most new apps come from the cloud. Furthermore, different user communities require different security policies, and creating a new Active Directory group for every use case is time consuming. Active Directory’s provisioning complexity, coupled with different authentication procedures and decentralized administration, leads to higher identity management costs and frustrated, overworked IT teams. Getting a short-term contractor access to the right apps with the right entitlements should take minutes, not hours or days. Business is constantly being asked to "do more with less," but with Active Directory we get "less with more."
Fact 3: Active Directory encourages bad behavior and increases security risks. Facts 1 and 2 give rise to Shadow IT. Users have figured out they can easily bypass traditional IT to get the services and capabilities they need. But this has resulted in raising security risk-levels inside the enterprise. For example, poor password hygiene in Shadow IT is rampant. Our own survey of 200 IT leaders showed that 71 percent admit to using unsanctioned apps like Dropbox and Google Apps to get work done, and 44 percent said employees manage passwords on sticky notes and spreadsheets. It’s an IT security nightmare.
What has been your experience getting Active Directory into the 21st Century? Have you successfully integrated it with your cloud apps? Was that seamless or seemingly endless? What have been your biggest challenges, and what have been the biggest gaps? Share your success stories as well!
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




