
News, news analysis, and commentary on the latest trends in cybersecurity technology.
Entitle Brings Fine-Grained Cloud Permissions Management Out of Stealth
The platform uses no-code policy workflows to automate the provisioning and revoking of permissions.
February 22, 2023

To keep businesses running smoothly in a multicloud environment, people and applications both need a web of permissions to access all the tools required to complete their tasks. Getting the balance right, however, is a perennial challenge at which most companies fail. A startup named Entitle aims to change that.
The company is debuting a permissioning system that the company says spreads decision-making responsibility beyond the IT department, to the business unit leaders who actually know who the users are and what they need in the way of permissions.
The fundamental problem has been around for years. In 2021, CloudKnox revealed that nearly all of the identities on the major cloud platforms (90% to 95%, depending on platform) used no more than 5% of the permissions granted. And a 2022 year-end wrap-up from Permiso showed that the average user and role still only uses 5.3% of their permissions.
The more lax the permission situation, the more likely it is that a bad actor will leverage their way into the network via an insecure account that has more access than it needs.
Entitle works to remedy that risk by issuing just-in-time permissions that can be revoked after a certain period or when a task has been completed. It also makes it easy to grant, change, and revoke permissions in bulk for people — employees or third parties — who are joining, leaving, or changing jobs, with what the startup calls "one-click on/offboarding." An access review panel collects the details of all permissions each human or machine identity has for overview, auditing, and compliance purposes.
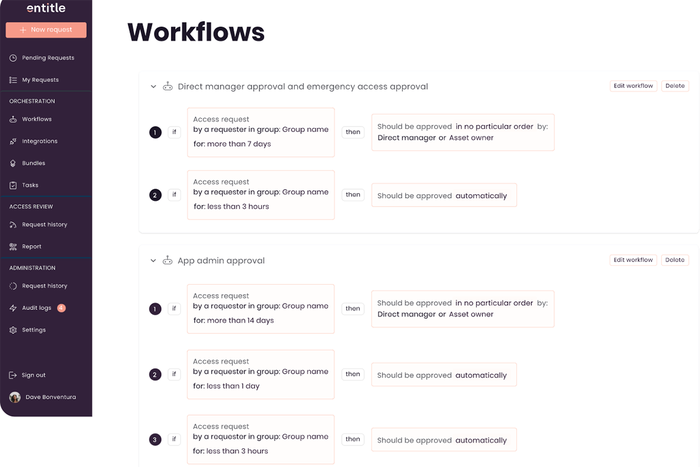
Entitle's Workflows function. Source: Entitle
Perhaps the most unusual aspect of the Entitle platform is its Workflows function, shown above, which is where a company can set rules to automatically approve permissions requests or send them to the proper role (for instance, direct manager or app admin) for approval. That should cut down on manual work and improve the ability of programs and people to get emergency access in order to reduce bottlenecks — a serious consideration when balancing productivity and security.
Of course, Entitle is not the first or only company to embrace the principle of least privilege. Authomize, for example, launched in 2020 with its own version of automated permissioning, and Delinea created a way for users to execute a privileged action without having to expand their role. But considering the security and business risks posed by access creep, ensuring that every user gets only the access they need is an important function.
About the Author
You May Also Like
Cybersecurity Day: How to Automate Security Analytics with AI and ML
Dec 17, 2024The Dirt on ROT Data
Dec 18, 2024

