What Keeps the CISO Awake at Night
How to keep your CISO sleeping soundly


How to keep your CISO sleeping soundly
One of the CISO's biggest fears is waking up to find their organization in the headlines reporting a security failure - which they do not have under control. Have you ever considered how prepared you are to respond to the question “what have you done about it”? Replace YOURCOMPANY with your organization’s name in the examples below, and consider your answers to the questions that follow:
Headline: Business comes to a halt as all workstations at YOURCOMPANY are encrypted with the latest ransomware
This scenario still happens every day, all it requires is a new zero-day vulnerability, and some hapless users who click on an email attachment. Would you be able to:
- Refer to a crisis plan to restore your machines?
- Identify the patterns of the vulnerability/malware?
- Identify patient zero?
- Ensure re-infections aren’t spreading?
Headline: Leaked HR and Payroll information sparks equal pay outrage at YOURCOMPANY
This might not “just” be a personal data breach, but a potential cause of internal tensions if payroll information of all employees became publicly available. Would you be able to:
- Identify how the attacker gained access?
- Understand which users or privileges were used?
- Stop the access for affected user accounts, in case exfiltration is still happening?
Headline: Undetected for two years, YOURCOMPANY hosts Command and Control Server for large scale botnet on careers webpage
You may think this one is unlikely as command and control servers are mostly hosted on unknown net-new servers, or websites that have vulnerabilities. However, every registration page your company owns where someone can sign up, upload and download data (such as a CV to your careers page), can be utilized as a command and control server. Would you be able to:
- Look for newly registered users?
- Monitor the standard deviations from the usual frequency or count of logins per user, or the volume of distinct source IP’s by individual users?
Headline: Energy and AWS costs explode due to unnoticed duo malware at YOURCOMPANY
Crypto-jacking for cyber criminals is an attractive way to monetize the infected hosts they have taken over, or cloud environments they have gained access to. Abusing the processing power for crypto mining, if done in a strategically, can stay unnoticed for some time, and often detected when it’s too late. Would you be able to run an investigation by putting a security lens on traditional IT-Operations metrics, such as CPU utilization?
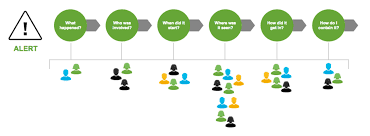
Remember, it's not the headlines that CISOs fear, it's not being prepared enough to respond with "we have this under control". So, whether or not it makes the news, would you be able answer these six questions in the face of a security breach?
Most of the answers will be hidden in your machine data, and harnessing all machine data will allow your team to be prepared. Take the first steps in facing your CISO’s fears; start to centralize your machine data and learn more about the four easy ways central logging improves your security posture.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




