Trump Suggests, Then Pulls Back on Joint Russian Cybersecurity Unit
President Donald Trump proposed, and quickly rescinded, the idea of a joint cybersecurity unit with Russian President Vladimir Putin during this week's G20 summit.
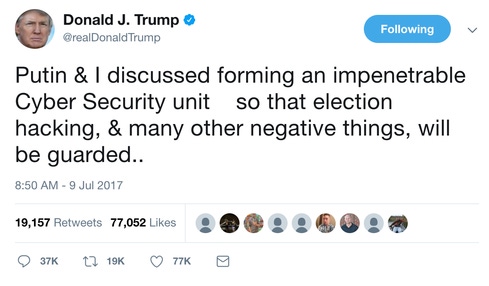
On Saturday, July 9, President Donald Trump suggested via a tweet the formation of a cybersecurity alliance with Russia following a conversation with Russian President Vladimir Putin. But later that day, Trump pulled back from that statement.
The two leaders met during the G20 summit in Hamburg, Germany. Their meeting, which lasted two hours and fifteen minutes, centered on the current and future nature of the relationship between the United States and Russia.
Trump tweeted about the potential for a cybersecurity unit after, he claimed, Putin "vehemently denied" Russia's meddling in the 2016 US presidential election. The "impenetrable Cyber Security unit" would guard against "election hacking, & many other negative things."
The tweet instantly sparked criticism from officials who were outraged at the idea that Moscow could be trusted in such a collaboration. US intelligence has discovered evidence indicating Russia did interfere with the 2016 election and targeted voting systems in multiple states.
Some security experts took Trump's tweet with a grain of salt.
"As a professional, I tune out his tweets to a degree … you couldn't take them literally as serious policy statements unless there's a follow-up," says John Bambenek, manager of threat systems at Fidelis Cybersecurity. "It seems so out of left field it's hard to take it seriously."
However, he continues, the idea could have serious implications if it became reality, as "a large part of our cybersecurity concerns emanate from that part of the world." Further, Russian intelligence services have relationships with many of the same criminals to share information, a structural impediment that would prevent the two from collaborating.
"How that cooperation would work would be awkward," he notes.
Michael McFaul, former US ambassador to Russia, said such a collaboration "just will not happen," Reuters reports. Restrictions on sharing information with Russia would prevent giving the country a closer look at US cyber capabilities; similarly, Moscow would also be resistant to sharing its own capabilities with the US.
Never Mind
When Trump changed his tune later on July 9 after his initial Russian cybersecurity unit statement, he said his mention of a joint cybersecurity unit with Russia does not mean he thinks it will become reality.
"It can't," he noted, though a ceasefire in Syria did happen. Trump also mentions the negotiation of a ceasefire in a separate tweet, adding how it's time to "move forward" in collaborating with Russia.

(Image: Twitter)
Russian Foreign Minister Sergey Lavrov reported after the meeting that Trump accepted Putin's statements claiming Russia was not involved in the election, according to a CNN translation. A White House briefing on the meeting, which has since been deleted, placed more focus on moving forward than enforcing consequences for the alleged interference.
"I think what the two Presidents, I think rightly, focused on is how do we move forward; how do we move forward from here," said Secretary of State Rex Tillerson in a statement. "Because it's not clear to me that we will ever come to some agreed-upon resolution of that question between the two nations."
Bambenek says he would be surprised if there is anything legitimate behind Trump's tweet. He does acknowledge the US and Russia will eventually need to cooperate on cybersecurity -- though doing so for elections "would be amusing."
"As a general rule, all things being equal, we're nations with our own laws," he explains. "But the Internet respects no international boundaries. We're not going to solve cybercrime unless we get nations to play in the sandbox somehow."
Such a collaboration would ideally focus on solving conventional cybercrime and protecting citizens from threat actors. While it's theoretically conceivable for nation-states to work together on this, it's tricky because of how foreign policy works.
"Is it possible? Yes, human beings can decide to play nice," he says. "Is it reasonable to expect they would? All foreign policy is based on exchanges. If they ask for 'X', they'll want 'X' in return. There could be a deal, but nations will act in their own self-interest."
Related Content:
About the Author(s)
You May Also Like
Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024Finding Your Way on the Path to Zero Trust
May 22, 2024Extending Access Management: Securing Access for all Identities, Devices, and Applications
June 4, 2024Assessing Software Supply Chain Risk
June 6, 2024Preventing Attackers From Wandering Through Your Enterprise Infrastructure
June 19, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




