Threat Actor Exploits Zero-Day in WinRAR to Target Crypto Accounts
Attacks targeting the now-patched bug have been going on since at least April 2023, security vendor says.
August 23, 2023
A threat actor with possible connections to Russia's financially motivated Evilnum group is targeting users in online cryptocurrency trading forums via a now-patched bug in the popular WinRAR file compression and archiving utility.
The bug, tracked as CVE-2023-38831, allowed the attackers to hide malicious code in zip archives masquerading as ".jpg," ".txt," and other file formats, and then distribute them in online cryptocurrency trading forums.
Months-Long Campaign
The attacks have been going on since at least April — some three months before researchers at Group-IB discovered the vulnerability and reported it to Rarlab, the company that develops and distributes WinRAR.
Rarlab issued a beta patch for the issue on July 20 and an updated version of WinRAR (version 6.23) on Aug. 2. Even so, at least 130 systems on forums that people use to trade cryptocurrency remain infected, Group-IB said in a report this week. The security vendor urged WinRAR users — currently estimated at 500 million — to install the new version immediately to mitigate their exposure to attacks targeting the vulnerability.
Researchers at Group-IB discovered the then zero-day vulnerability in WinRAR when investigating threat activity related to DarkMe, a remote access Trojan that security vendor NSFocus first discovered last year and attributed to Evilnum. The malware packs a variety of functions for spying on targets or for use as a loader for other malware. NSFocus observed the Evilnum group deploying DarkMe in attacks that targeted online casinos and trading platforms in several countries.
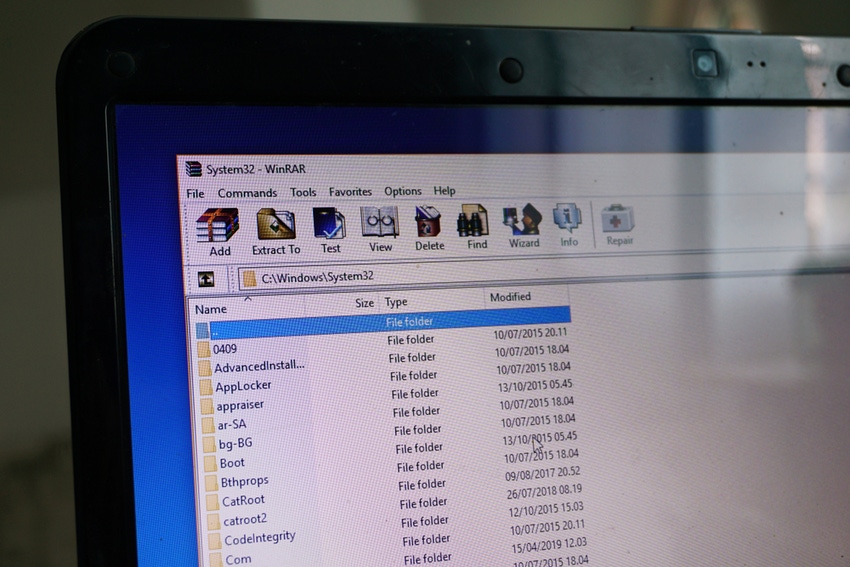
The vulnerability that Group-IB found stemmed from how WinRAR processes the zip file format. It essentially gave attackers a way to conceal various types of malware tools in zip archives and distribute them to target systems. Group-IB researchers observed the threat actor deliver at least three malware families this way: DarkMe, GuLoader, and Remcos RAT.
The threat actor then distributed the weaponized zip archives on at least eight public forums that online traders use regularly to share information and discuss topics of mutual interest.
Weaponized Zip Archives
In most cases, the adversary attached the malware-loaded zip archive to a forum post or in private messages to other forum members. The topic of the posts tended to be something that would grab the attention of a forum member. For example, in one post, the threat actor purported to offer their best personal strategy for trading with bitcoin and attached the malicious zip archive to that post. Group-IB says it also observed the threat actor gain access to forum accounts and insert their malware in existing discussion threads.
In a few instances, the attacker distributed the zip archives via a free file storage service called catbox.moe.
Once installed on a system, the malware gained access to the trading accounts of the victim and executed unauthorized transactions to withdraw funds from it.
On a few occasions, forum administrators became aware of malicious files being distributed via their sites and attempted to warn members about the threat. Despite these warnings, the threat actor continued to make posts on the forum with malicious attachments. "Our researchers also saw evidence that the threat actors were able to unblock accounts that were disabled by forum administrators to continue spreading malicious files, whether by posting in threats or sending private messages," Group-IB said.
According to the security vendor, while the DarkMe Trojan suggests Evilnum is associated with the campaign, Group-IB itself has not been able to attribute the WinRAR attacks definitively to the threat group.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




