Real-World Threats That Trump Spectre & Meltdown
New side-channel attacks are getting lots of attention, but other more serious threats should top your list of threats.
January 22, 2019
If you judged the severity of a security vulnerability by its number of mentions in the press and social media — a silly thing to do, by the way — side-channel exploits would seem to be the end of the computing world. But does the reality of the situation really match the hype?
Many side-channel attacks actually require both technical sophistication and patience. Speculative execution side-channel attacks like Spectre and Meltdown require quite a lot of each of those qualities. Other types of side-channel attacks, such as the recent page cache vulnerability, require less sophistication on the part of the attacker but are more easily thwarted via software updates.
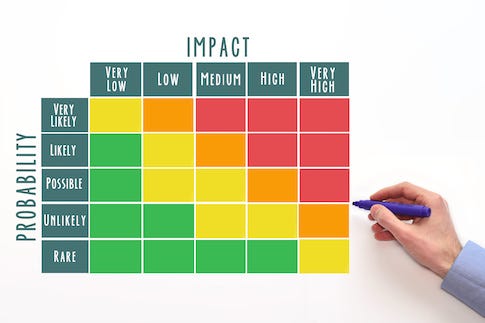
The bottom line is that there are many other cyber threats that your organization most likely will face today than a side-channel attack, security experts say. The more severe threat candidates encompass common attacks and vulnerabilities, as well as user behavior - most of which have been responsible for real-world business losses. The new generation of side-channel vulnerabilities are mostly still - as far as we know - the stuff of research, not crime.
That doesn't mean you should ignore side-channel threats. Mounir Hahad, head of Juniper Threat Labs, noted that the "latest side-channel attack is severe, in my opinion."
With that caution, here is a rundown of threats that are more imminent than those splashy side-channel attacks.
(Where do you place Spectre, Meltdown, and their malicious kin in your hierarchy of threats? Which threat keeps you up at night? We'd love to know your thoughts — the comment section is open).
(Image: Andrew Stefanovskiy — Adobe Stock)
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


