Education Now Suffers The Most Ransomware Attacks
New data shows ransomware rates worldwide doubling and tripling in past 12 months.
September 21, 2016
When you think ransomware victim, most likely your first thought is a hospital. But a new survey of ransomware's spread among different industry sectors shows that education is actually the biggest target right now.
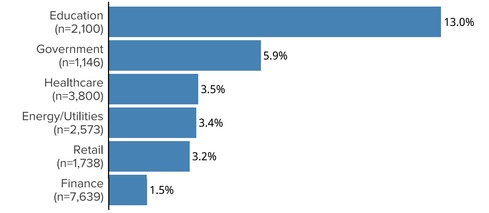
BitSight, which rates the security posture of organizations based on external data showing malicious activity surrounding them, in a new report today found that education is hit most by ransomware attacks, followed by government, healthcare, energy/utilities, retail, and finance.
The firm's analysts studied ransomware activity at some 20,000 organizations and found that one in 10 education organizations had been hit with malware on their networks, followed by 6% of government entities; 3.5% of healthcare organizations; 3.4% of energy/utilities; 3.2% of retailers; and 1.5% of financial organizations. According to BitSight, the rate of ransomware attacks has doubled or tripled among various industries in the past 12 months.
BitSight's ransomware data is based on traffic by the malware; for instance, as it communicates to its command-and-control servers. It shows infected victim machines in those organizations, but doesn't necessarily mean the victims were unable to retrieve their data from backups, for example.
A recent Osterman Research survey found that both phishing and ransomware attacks had jumped several hundred percent per quarter in the past 12 months. That survey, commissioned by DomainTools, also named ransomware in the top three concerns for IT and security pros.
Law enforcement has been relatively vocal about noticeable spikes in ransomware of late: the FBI issued a public service announcement late last week urging ransomware victims to report attacks to the agency. This, after an FBI official told attendees of a Federal Trade Commission (FTC) event to immediately contact the FBI or IC3.gov if they suffer a ransomware infection, and not to pay any ransom fees.
"People have to remember that ransomware does not affect just one person or one business," Will Bales, supervisory agent for the FBI's Cyber Division, said. "It will more than likely move on and affect somebody else. And for those who pay the ransom, it only encourages them to extort the next person."
One ransomware variant infected 100,000 computers in just one day, the FBI noted in its announcement. "Cyber security companies reported that in the first several months of 2016, global ransomware infections were at an all-time high," the alert said. The FBI also noted that it needs to get a better handle on the actual number of victims, hence the call for reporting to them.
Stephen Boyer, co-founder and CTO of BitSight, says he and his team were surprised that education tops healthcare in ransomware attacks. "Protections in higher ed are lower" he says, given universities' open culture and complex user environment, for example.
To date, healthcare organizations—namely hospitals—have been the most high-profile ransomware victims, from Hollywood Presbyterian Medical Center in Los Angeles, Calif., to Washington, DC-area MedStar. Hollywood Presbyterian ultimately ponied up with $17,000 to the attackers to release its systems. MedStar had to temporarily shut down its computers, email system, and large record database to inhibit its spread to other locations in the region, and reportedly did not pay the attackers any ransom.
More unnerving is that BitSight's new data represents just a snapshot of the attacks, Boyer says. "We know we're not seeing all of the ransomware" here, Boyer says. "But we're seeing hundreds of companies in just about every sector."
BitSight also found that two particular ransomware variants were the most prevalent: Nymaim and Locky. More than 11% of education organizations were hit by Nymaim, and 4%, with Locky, which came on the ransomware scene about eight months ago. Nymaim hit about 4% of the government entities, and 3%, Locky.
"Another important fact to note is that Nymaim, although typically associated with ransomware, is actually a Trojan that can be used to install a variety of malware," the report said.
The big takeaway from the BitSight data on ransomware: "No sector is immune," Boyer says.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


