5 Questions Your Organization Must Ask to Prepare for a Ransomware Attack
Ransomware's evolving all the time, but here are some issues to address now to mitigate the impact of the next ransomware wave.
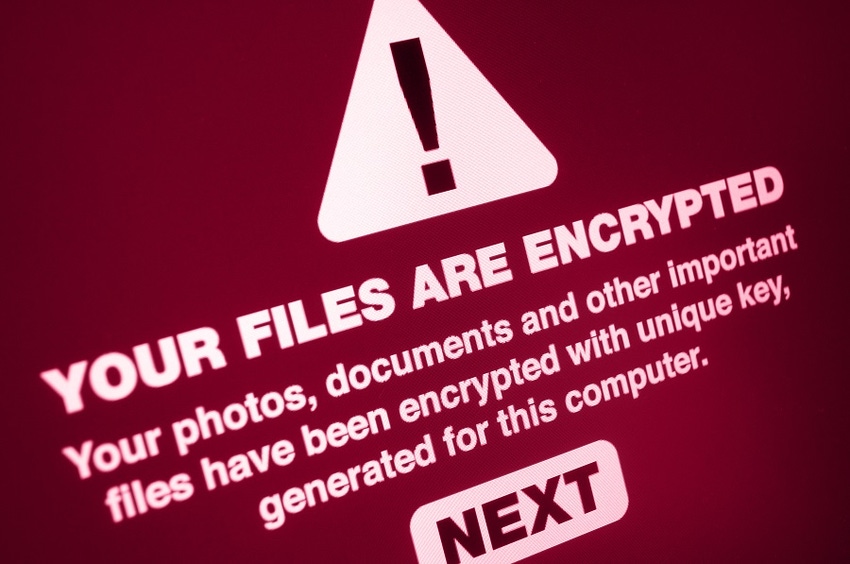
In 2020, there was a successful ransomware attack every eight minutes. That means that every time you boil an egg, another organization just fell victim to ransomware. With the ongoing scourge of ransomware only growing more voracious by the day, we can expect to see more high-impact attacks; 78% of companies anticipate another SolarWinds-style supply chain attack. But are organizations prepared to defend against increasingly nuanced threats?
The news headlines argue that not all are. Look no further than the recent ransomware attack on IT solutions developer Kaseya. This attack is the latest example of how security vulnerabilities continue to come from the most unexpected places. So what questions should organizations be asking themselves and what steps should they be taking now to mitigate the impact of the next wave of ransomware? Here's where you can start.
Ask Yourself, "Can We Effectively Defend Against a Ransomware Attack?"
Organizations should begin by understanding their current posture. Start with a threat hunting exercise to evaluate the various avenues of ransomware compromise and the strength of your defenses. Like all attacks, hackers need an entry point to carry out ransomware campaigns. Whether it's through unpatched systems, compromised credentials, spear-phishing, or a compromised vendor, the attacker must get an initial foothold into your environment. The threat hunt will show gaps that could be leveraged as an entry point across the attack surfaces. In addition, your assessment should address system redundancy and backups retained for critical business data.
Increasingly, a key part of defending against ransomware involves proactively assessing your own environment and technology vendors for ransomware mitigations. Given the current threat landscape, it is important to confirm that your vendors maintain an effective defense posture and that you timely remediate vulnerabilities on your systems before they are exploited.
Do We Have a Plan to Detect, Contain, and Recover from a Ransomware Attack?
The next step to tackling the threat of a ransomware attack is to spell out the plan to detect and respond to the threat.
Your ransomware runbooks need to address the steps and capabilities to contain ransomware, including system and network isolation. The aim is to limit the blast radius quickly after an infection is detected. In addition, your response runbooks need to address considerations beyond technical containment. In fact, ransomware response cuts across multiple processes, management layers, and functions within your organization, such as restoration of data and operations, internal and external communications, decisions on paying the ransom, specialized professional services firms, and more.
Lastly, your plan needs to be tested through cross-functional tabletop exercises that simulate a ransomware attack before a real one occurs.
Do We Have Access to the Data We Need to Understand the Impact of a Ransomware Attack?
The key resource in countering ransomware attacks is having immediate access to the right telemetry. The fingerprints of an attack are recorded in data. Organizations need the ability to systematically contact-trace their assets during an attack to understand how and how far an attacker penetrated their networks. Then, they need to work out whether any related systems in their supply chains, customers, and partner networks have also been compromised through lateral movement.
What Processes Are In Place to Ensure We're Constantly Evolving Our Approach to Cyber Resiliency?
Ransomware attacks in 2021 are not the same as they were five years ago, and tactics will continue to evolve. Adversaries have a variety of methods for encrypting and publicly shaming victims into paying. It's also worth noting that some insurance companies are increasingly reluctant to pay ransomware demands, and there are broader industry calls for both victims and insurance companies not to pay ransoms.
All of these changes will inevitably affect how organizations respond to ransomware threats and attacks, so organizations need to maintain an updated framework on how to evaluate resiliency, prevent, detect, and respond to ransomware based on threat intelligence and industry learnings from attacks.
Are We Moving Fast Enough?
To effectively respond to ransomware, organizations must move fast to understand the scope of the compromise and contain the incident. Your mean-time-to-detect (MTTD) and mean-time-to-respond (MTTR) are key. From isolating networks to sinkholing malicious domains, it's vital to have the right level of security automation to effectively detect and contain a ransomware attack. Response automation can make the difference between a minor incident and a high-profile compromise.
Preparing for the Inevitable Next Attack
The threat of ransomware isn't going away anytime soon. Acknowledging the threat ransomware poses and building a cybersecurity response plan around data is the best chance we have of navigating this constantly evolving threat.
Attacks like Kaseya and SolarWinds remind us to ensure our own organizations are prepared to withstand such an attack. When news of a major cyber incident hits, it's critical to take immediate action to confirm patches and security protocols are up to date.
Unfortunately, ransomware and supply chain attacks are here to stay. Practice cybersecurity hygiene, build your incident response plan, and prepare for the next wave of attacks to come.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




