10 Funny Twitter Feeds For Security Geeks
These must-follow Twitter feeds offer plenty of cybersecurity humor to keep infosec pros giggling even when the attacks keep coming.
December 18, 2015
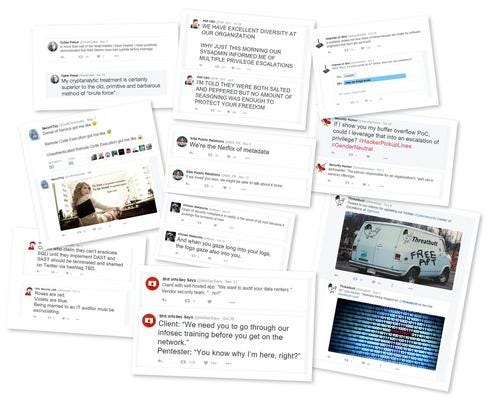
Let’s face it—information security isn’t inherently the most humorous field in the world. While the subject matter might elicit more laughs than something like periodontal dentistry, odds are it wasn’t the potential yuks that drew you to the profession. But like paramedics, morticians, and other professionals used to dealing with traumatic situations, infosec pros tend to be a pretty funny bunch of folks--even if the humor runs a little black.
Because in spite of the frustration and long hours, there’s a lot that is really hilarious about security, as long as you look at it in the right way. We’ve rounded up ten of the funniest security-related Twitter accounts that do just that. Their posts range from the daily face palm variety all the way up to some pretty strange high-concept stuff. Either way, it'll help you keep your sanity intact through some healthy exercise of the funny bone.
About the Author(s)
You May Also Like
Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024Finding Your Way on the Path to Zero Trust
May 22, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




