Vulnerability Scanning Triples, Leading to Two-Thirds Fewer Flaws
Companies are scanning more applications for vulnerabilities — and more often.
February 8, 2022
Companies have increased the cadence of application-security testing — with triple the number of applications scanned and 20 times more scans per application — compared to a decade ago, according to Veracode's new "State of Software Security" report.
The focus on increasing the frequency of scanning, automating testing and deployment, and educating developers — all hallmarks of the cultural shift known as DevSecOps — has led to a two-thirds reduction in the number of vulnerable libraries and a one-third reduction in the time required to fix flaws, the company states. While 77% of third-party libraries still have a known vulnerability three months after disclosure, the half-life of flaws in those libraries (meaning the time it takes to fix half of the flaws) is three times faster.
Overall, developers are moving in the right direction, but they still have a long way to go, says Chris Eng, chief research officer at Veracode.
"Things are moving in a nice direction, showing that people are paying more attention to [finding vulnerabilities earlier]," he says. "We are seeing an increase in the adoption of different scanning types, with a significant decrease in vulnerable libraries — not shrinking just a little bit, but a lot."
The report is the result of Veracode looking at every application in the company's database and analyzing the trends over years.
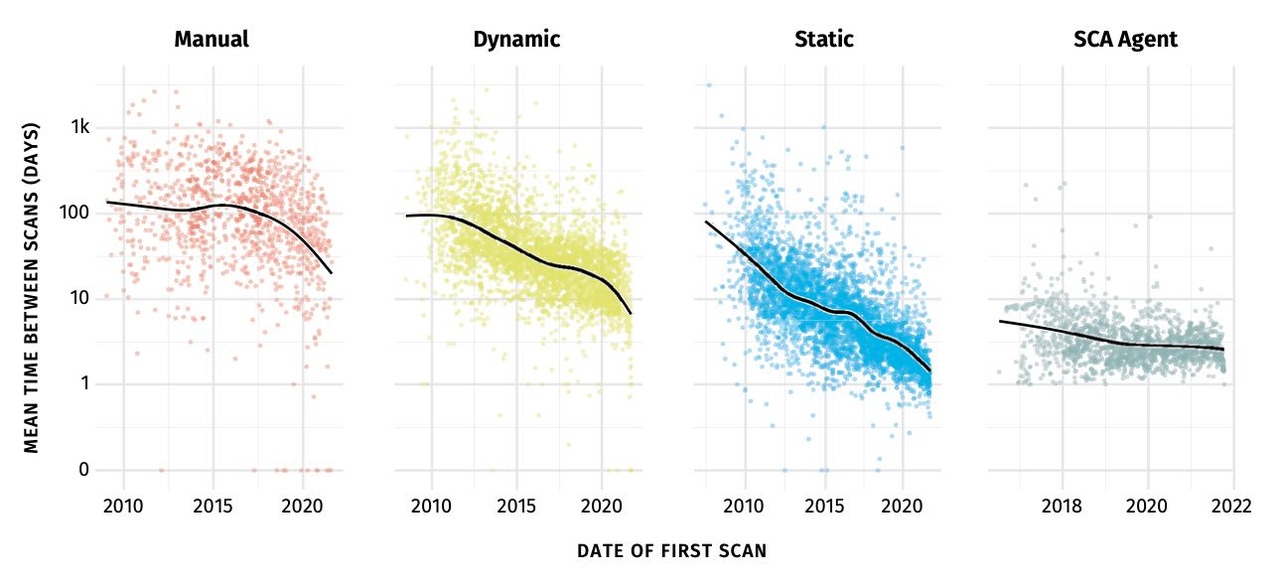
A decade ago, the typical Veracode customer averaged two or three scans a year, but now most developers run daily static-analysis scans and weekly dynamic-analysis scans, Veracode states in the report. In 2010, for example, only 10% of applications were scanned at least weekly, not even once a month for the average application. In 2021, 90% of applications are scanned more frequently than once a week, the report stated.
"Continuous testing and integration, which includes security scanning into pipelines, is becoming the norm, and we can see that reflected in how often users are scanning their applications," the report states. "The sooner in the life cycle you discover problems, the more likely you'll be able to solve them quickly, before they become a bigger problem down the road."
Another trend that suggests agile development is taking off and having an impact on vulnerabilities is that development teams appear to be moving to breaking up monolithic programs into smaller collections of services, or microservices. In 2021, less than 5% of applications used multiple frameworks and languages, down from 20% in 2018, suggesting that large software projects involving multiple languages are becoming more rare, according to Veracode.
"You think that applications always get bigger and bigger over time — they get bloated with code, and people don't get rid of functionality," Eng says. "But we see that they are getting smaller, that these single-language applications indicate that developers are adopting microservice architectures."
The different types of testing tended to find different types of vulnerabilities, with the exception of information leakage, a common issue found by every testing technique. The most common flaws discovered by static analysis, for example, were CRLF injection, information leakage, and cryptographic issues, while dynamics analysis commonly found server configuration, insecure dependencies, and information leakage issues. Software composition analysis (SCA) discovered insufficient input validation, information leakage, and encapsulation issues most commonly.
Every language had its particular propensity for vulnerabilities as well. Java applications tended to have CRLF injection issues, while Python programs' most common flaws were related to cryptographic issues, and C++'s top mistakes involved error-handling.
Vulnerabilities discovered by software composition analysis took the longest to remediate, likely because the fixes have to flow up to the developer from the project maintainers. Fixing half of the flaws discovered by each technique took 143 days for dynamics analysis, 290 days for static analysis, and 397 days for SCA, Veracode states in the report. However, the response-to-SCA result is actually a significant improvement — in 2017, it took more than three years to patch half of the issues.
"Given that we know that more scanning using multiple tools means faster fix times and less security debt, this shift can only be viewed as good for the future of application security," the company says. "It’s yet to be seen whether the pendulum of history will swing back to monolithic applications and waterfall development, but that doesn’t seem likely now."
In terms of open source libraries, Veracode found that the most popular libraries continued to remain the same over the last five years. More than 97% of the code in Java applications, for example, are from open source libraries. However, the share of flawed libraries has declined over the past five years, with Java, JavaScript, and Python seeing a significant reduction in vulnerable libraries.
"The larger lesson here is that developers are going to stick with tried-and-true libraries and likely aren’t going to attempt to refactor their code base to pick up the latest hot commodity," the report states. "Updates happened slowly when libraries didn’t have flaws but relatively quickly when they did. As long as open source developers continue to fix security flaws, developers will keep on using those libraries."
About the Author
You May Also Like




